Autokms autokms.exe. is orgmode.com dangerous? 2019-05-12
orgmode.com
If something does not work, just read the instructions — everything is described in simple language for inexperienced users. If you know md5 ,size, sha1,sha256 or other attribute of the file which you want to review, then you can use Advanced Search in our. Nous partageons également des informations sur l'utilisation de notre site avec nos partenaires de médias sociaux, de publicité et d'analyse, qui peuvent combiner celles-ci avec d'autres informations que vous leur avez fournies ou qu'ils ont collectées lors de votre utilisation de leurs services. It's a false positive meaning your Anti-Virus will flag it as a thread when it's completely harmless. Over time, your computer accumulates junk files from normal web surfing and computer use. Double click the Malwarebytes icon and run mbam.
orgmode.com
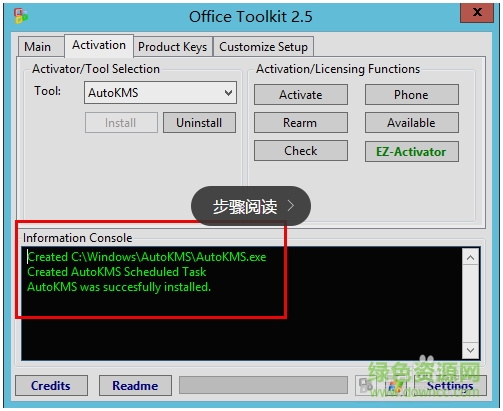
If yes, please check the properties of these files, and you will know if the file you need is 32-bit or 64-bit. Even if you are experienced at finding, downloading, and manually updating drivers, the process can still be very time consuming and extremely irritating. Keep a log of this so you can find it easily should you need to use System Restore. It is a very popular malware and spyware removal application. As with every hacking utility, use it at Your own risk. To accomplish this, you will need to restart the computer. During installation, a run registry key for all users is added that will cause the program to run each time any user logs on to Windows.
orgmode.com

This tool will help you keep your system under control. Illegally distributed software and media materials may also contain code that can lead to the infection of this malware. You will be prompted with End User License Agreement. Users who suffer from this Trojan infection will notice that the affected computer just goes bad to worst. Step 23:Keep Antivirus up to date and active. To more specific, the Trojan virus invades the contaminated system to trigger slow system performance and make it vulnerable.
What is orgmode.com ? orgmode.com info

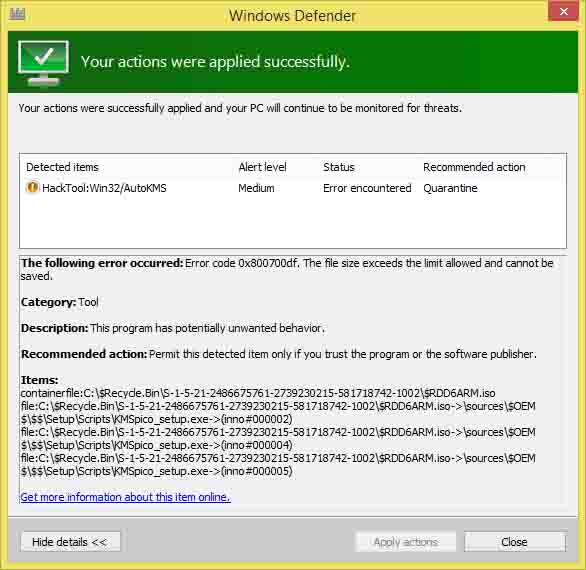
For some reason if you cannot remove this virus then most likely you need help from technicians who can perform analysis of your particular situation to remove this virus. When in doubt, quarantine it. Scheduled tasks startup - autokms. Gen AhnLab V3 Internet Security 2013. Then, the main window will appear. These troubleshooting steps get progressively more difficult and time consuming, so we strongly recommend attempting them in ascending order to avoid unnecessary time and effort. Though I'm not sure if it does any unwanted additional things.
orgmode.comS
To manually repair your Windows registry, first you need to create a backup by exporting a portion of the registry related to autokms. Manually editing the Windows registry to remove invalid autokms. If you're using Microsoft Office 2016, read this to verify activation. I also requested help on the techspot forums as they seemed to be more active at the time I was having an issue. Please reach out to us anytime on social media for more help:.
orgmode.comS Remove
There is no circumstance for users to leave the Trojan infection in the computer. Without executable files like autokms. I think the license they have allows staff to install on laptops that are not property of the school Also I checked out the quarantine entry again. If you are not currently backing up your data, you need to do so immediately to protect yourself from permanent data loss. Source of this trojan may vary due to the changing ways how it is deployed. However, it takes time for antivirus to figure out a suitable version to clean out this Trojan horse. The best part is that can also dramatically improve system speed and performance.
a real threat?

The above paths are the common paths where this file is located, but does not mean that it must be stored in the above paths. I have searched around on the internet and see that most places call it a Trojan. If so how can I get rid of them? I also see I think that its part of Microsoft??? So it wasn't an unofficial copy as I'm sure the district wouldn't do that heck its a huge district with at least 6 big high Schools and many many middle and elementary schools. I will certainly recommend Exterminate It to others. Make sure your computer is up to date with windows updates. It is recommended to remove as it is a virus named Trojan, I would also suggest you to remove threats which are encountered while running anti-virus program on your computer. If you want a Desktop Icon or Quick Launch icon then check appropriate boxes.
orgmode.comS
Include the contents of this report in your next reply. Then, registry entry is created to call the file on each Windows boot-up. Trojan do not usually spread by themselves. User Account Control will prompt if you want to run the program, click Yes to continue. Keep the active and current 6. Please be patient as this can take some time. It will take several minute before a Notepad file containing log information on what Rkill found will open.
a real threat?
I have moved it to quarantine once already but it popped up again. You can find it running in Task Manager as the process autokms. This step is your final option in trying to resolve your autokms. Or was it detected already on my laptop C drive? By most antiviruses this application will be marked as a possible threat Trojan, not-a-virus:Activator. Spyware frequently piggybacks on free software into your computer to damage it and steal valuable private information.