Does malwarebytes scan all drives. Malwarebytes Premium 2019-01-28
Will Malwarebytes scan all drives in system, or just #1?
I did that as well. You can download a manual updater from the link below. Follow the steps to extract the file and Malwarebytes Anti-Rootkit will be extracted to a folder called mbar-versionnumber on your desktop. Infact once the scan detects possible threats, the app also will prompt the user to launch the treat scan in order to properly identify and also address the possible threat. You can always download these programs again if files are lost. The icon for this program looks like: Once you double-click on the mbar. Then you are denied access to your files and unless you give out or pay the requested ransom, you cannot get your files.
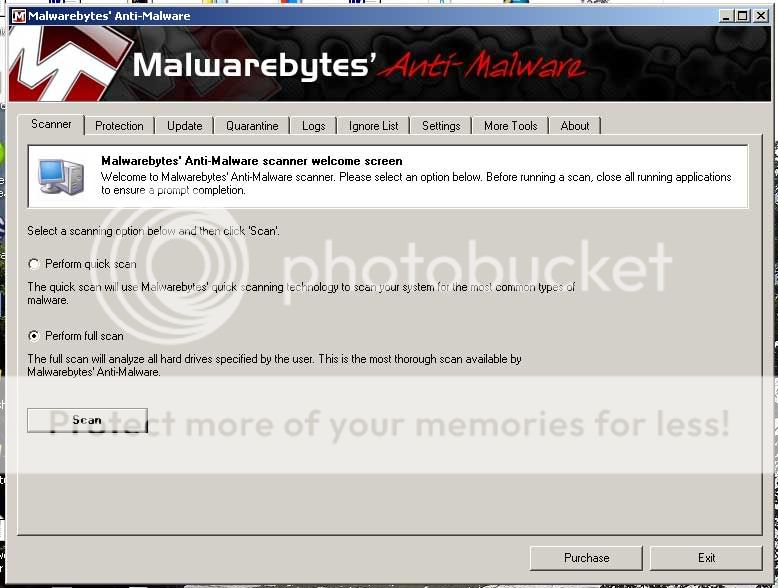
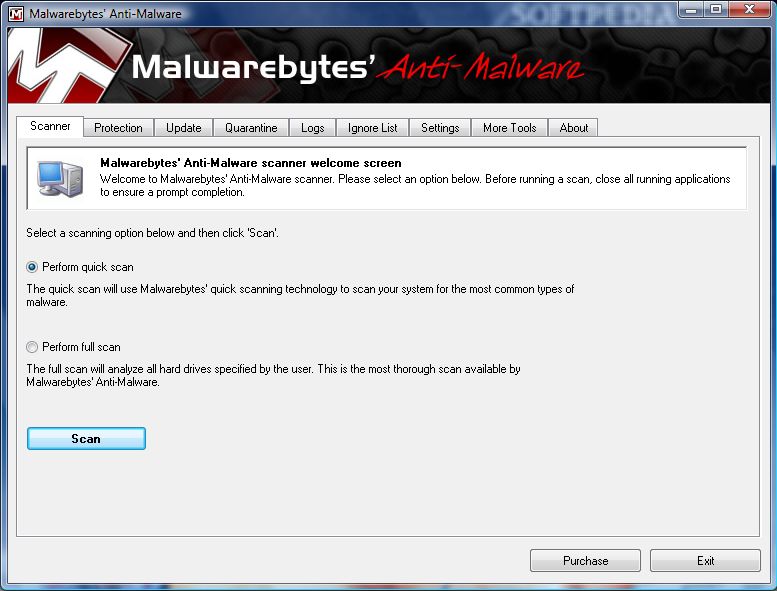
Running Malwarebytes
A custom scan time interval may vary widely each time, based on the areas scanned, the number of files involved, and the size and complexity of the files. Clicking the Ignore Once button temporarily ignores the threat, although it will be shown as a threat on subsequent scans. Sometimes the blocked web site is triggered by a banner ad that is being hosted on another site, separate from the website you attempted to access. Scans don't waste time, other than the 2 minutes it typically takes to start one. My initial search did not turn up anything So after a day or two. It would not be scanned in the future. When saving the file, please save it to your desktop.
Does MalwareBytes scan External HDDs too?

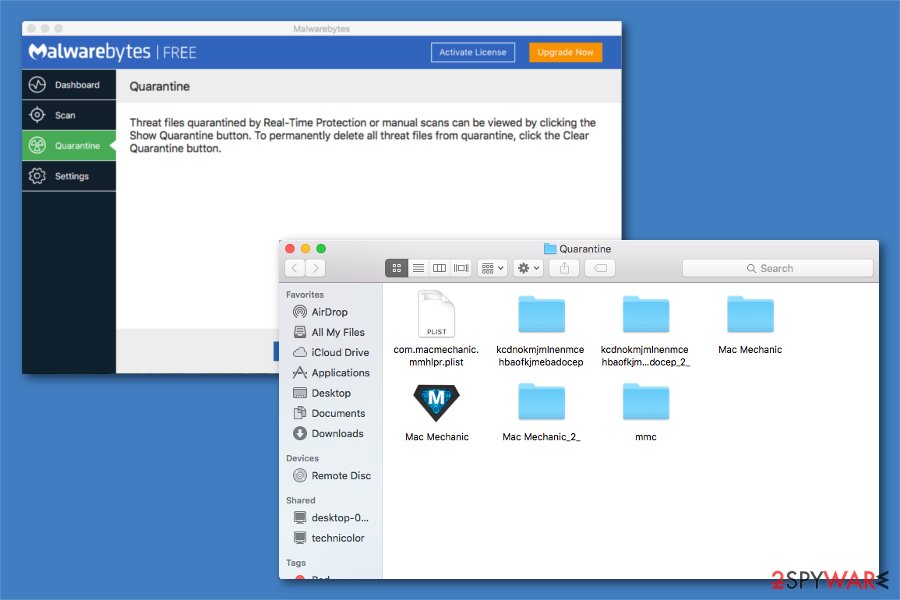
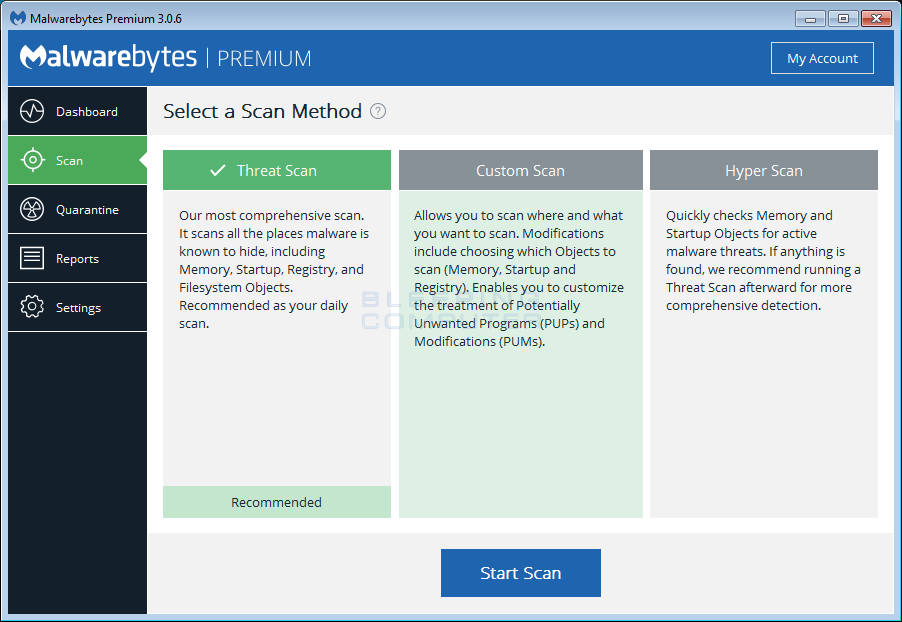
You may also click Cancel at any time to terminate the scan. Once your data has been backed up, you should then download Malwarebytes Anti-Rootkit from the following download location: Once Malwarebytes Anti-Malware has been started, click on the Quarantine tab. In this mode, users are able to scan their whole system for threats, including attached flash drives and external hard drives if there are any. It is a basic necessity for everyday work and users are also recommended to do this scan daily. There are three scan types which can be executed — Threat Scan, Custom Scan, and Hyper Scan. Although most of the other components are in their initial stages, it is worth investing in, because of the solid malware protection.
[SOLVED] MalwareBytes

But if you have lots of disposable income, then sure, go for premium. How to use Malwarebytes Anti-Rootkit to remove Rootkits Malwarebytes Anti-Rootkit is currently in Beta and could contain bugs or not operate as expected. Through all these upgrades my ext. Update your operating system, browser, and applications. By default, all are selected for removal.
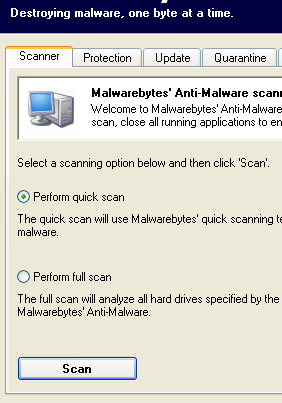
Running Malwarebytes

For example, Malwarebytes Anti-Rootkit version 1. Next, select Custom Scan from the menu. Please refer to that section for more detail. To restore a file, simply select the entries you wish to restore and click on the Restore button. If Malwarebytes found a particularly large number of malware related objects, you may want to rescan your computer. After the computer reboots and you login, you will be back at your normal desktop. I see with Windows Vista that I can log into all 3 profiles and then Switch User and do that for Profile 2 + 3 and then go into the main profile 1 and do a scan.
Malwarebytes Premium 3.7.1.2839 Crack with Keygen is Here
So I would have taken the results with a grain of salt. We therefore encourage you to run this scan as the last thing you do on your computer for the day, leave it running over night, and check the results in the morning. If the item should pose a threat to system processes, it will be marked as a threat and will be terminated immediately. The length of time for performing a Full scan will also vary but because it is so comprehensive, this type of scan can take several hours. You will now be at the Scan System screen where you can select some basic scanning options. Before you flip out, try these simple steps to clean up your infected computer.
Malwarebytes Anti
Step Three: Updating If the date of your last update is not within the past week, you should click the Update Now link, highlighted in red above and allow Malwarebytes to update. Make sure everything is selected and that there is a check mark in the Create Restore point option. I did that and it did scan each individual username folder. I scan, find 362 infections, clean all 362, but still have to wonder if some were in memory, unrecognizable, or just couldn't be found at all due to it being a network scan, requiring me to scan it locally. The mbar-log file will always start with mbar-log, but the rest will be named using a timestamp indicating the time it was run. If the item should pose a threat to system processes, it will be marked as a threat and will be terminated immediately.
Does MalwareBytes scan External HDDs too?
But sometimes over the past year or two they changed the free package. Microsoft Security Essentials is pre-configured to do a once-a-week Quick Scan. I certainly hope so because no one knows for sure. Some threats may require a computer restart to completely eliminate the threat, but we feel it's best to notify you at the time, so you may save your work before restarting your computer. Users can scan individual files, folders or drives by utilizing the the right-click context scan option. Frequency and Settings was discussed in the previous section Advanced Mode. Blocking Malware This feature is what Malwarebytes is known and loved for.
Will Malwarebytes scan all drives in system, or just #1?
As for the Custom Scan, it is highly recommended to run it at least once a week. No it is not, but do know of something that might interest you. Custom Scanning Options These settings provide capability to determine the functional areas that will be scanned. It is important to note that if you restore infected files and configuration information, these infections will become active again the next time you reboot your computer. Most anti-virus programs will allow you to do this.
10 easy steps to clean your infected computer

The length of time for performing a Quick scan will vary but it generally takes about 15-30 minutes so they can be performed daily. Common weaknesses are outdated software installed in the system. This is the recommended scanning mode. A box will pop up and it will notify you when it is finished. Only the bare minimum programs and services are used in this mode. This process can take some time, so please be patient. Fake Anti-viruses, keyloggers, adware and rootkits are all forms of malware.