Crack pdf password without software. PDF Password Crack 2019-04-22
Winrar Password Remover 2019 Crack Full Version Free Download [Latest]
From there, an attacker could try a handful of targeted passwords that would have a higher success rate than just random guesses. The new file will now open directly without prompting you to enter the password. Hack Number 8 Tools: , Target: content restrictions Install and. A hash is also a way of scrambling a password--so if you know the trick, you can easily unscramble it. The remaining pages appear blank until they are unlocked.
How to Crack a Password like a Hacker

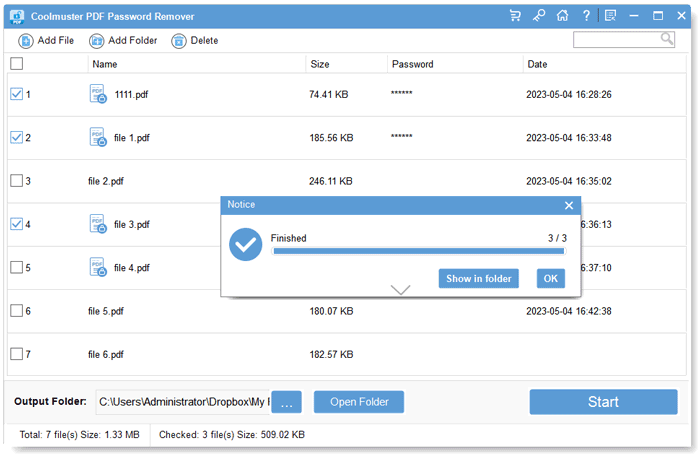
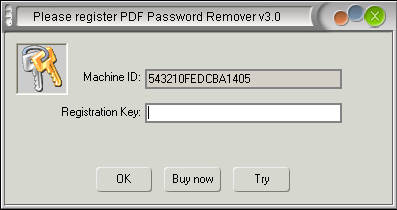
Using them for inappropriate means may put you in trouble. With its advanced features, you can recover your passwords, and it gives you the access to your important files without any interruption. At least with open source there are many eyes presumably reviewing the code. Read the below lines and follow the steps one by one. This makes finding a password pretty darn difficult. Many companies and schools have policies against using their computers for resource-intensive tasks such as cracking passwords. If you face any kind of problem, then feel free to comment it below.
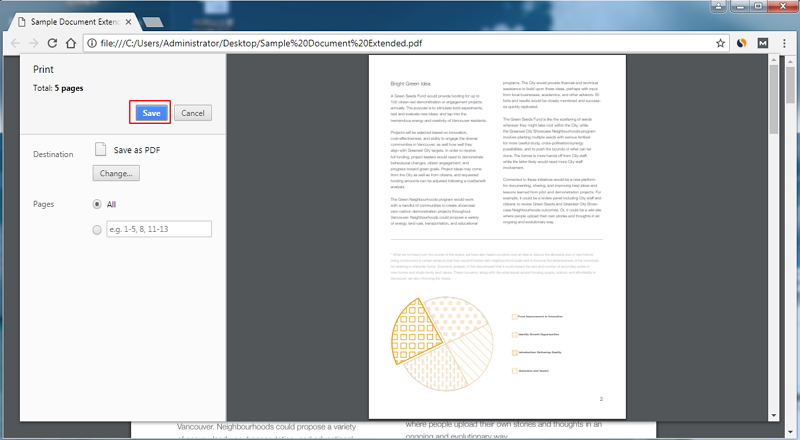
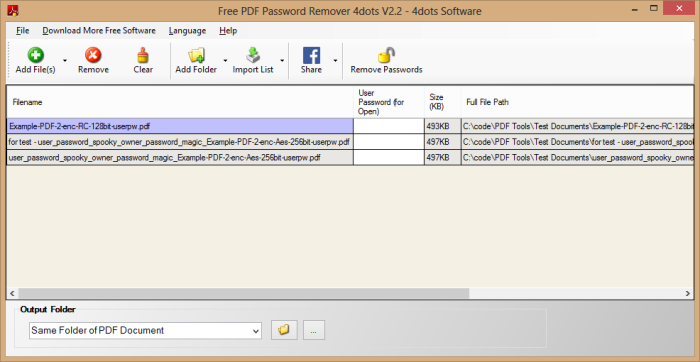
Unlock PDF
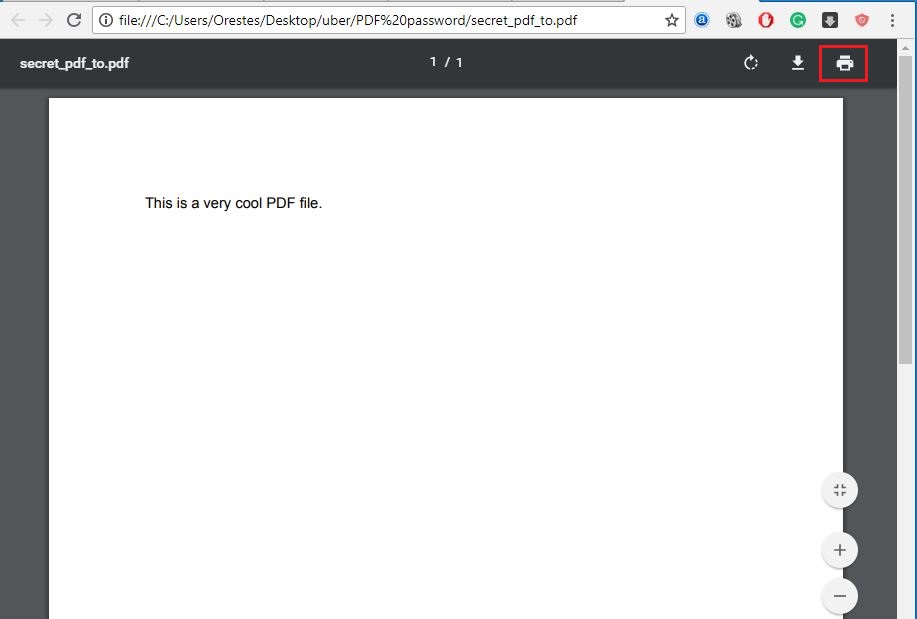
Winrar has the capability to compress files into two different formats such as Zip or Rar. Hack Number 6 Tools: , Target: 3rd party , content restrictions Drawbacks: Proprietary software. They would have to hack the server to do that. Lost your windows password or want to hack your friends computer or want to hack your school computer? The result might be great, or not so pretty depending on the desktop resolution, page dimensions, and other factors. How to Install this Software? Find an unencrypted copy of the ebook viewable or downloadable online. Conclusion:I hope the post was helpful. Password remover 2019 with crack: One of the most popular archive manager in computer software industry which is Winrar.
How to Remove Password Protection from PDF File on Android?
Owner passwords can be found with the -o switch. The mere presence of source code does not guarantee absolute safety. This password cracker automatically saves your pin retrieval state. Password cracking of longer passwords can take days or weeks to crack, so we limit the password length to 9 characters. The document can not be text searched because it is composed out of images, but there are programs that can.
What is a Password Cracker Program?

The companies involved have released newer software, so we can read these documents on our devices without resorting to hacks. This requires purchase and activation of Bookshelf app on up to two machines. This software supports all type of Rar files. We assert our basic human rights, including the right to customize material that we created, bargained for, or purchased. Password crackers and other kinds of password recovery and finder tools are legitimate programs to help discover or reset lost passwords.
What is a Password Cracker Program?

When you start your computer press f8 and select Safe mode as shown in the picture and press Enter 7. Those earlier PostScript drivers have been deprecated, but older versions of still provide them. Winrar helps you to compress or decompress files it also reduces the file size by compressing it and if you want to view the file then you have to extract the file first. Comment below if you wish to have any assistance from my side. They do not actually work against 3rd party server passwords. It might be a good idea to empty out the screenshots folder first! Online attacks require the attacker trying to login to your to go to the specific website they are targeting.
How to Hack Windows Password Without Any Software
Download it to have a free try now! Usually a document that uses 3rd party is also restricted using one or more of the following security signatures as well. This may take hours to few days. The conversion process runs very slowly because of PostScript errors introduced from the hack, but it is good for small chapters when technique 1 does not work, or when can not be installed on the system. This amazing software has built-in algorithms which are implemented on the file to unlock or break the password online. This tip is for information purpose only. With so many file sharing sites, ebook readers, and search engines out there, one can find earlier versions, or unencrypted copies of just about anything free or cheap.
How to Remove Password Protection from PDF File on Android?
New viruses, bugs, and backdoors are made all the time. So, you need to know the password so as to make the file secure free. Dig through Google Books, Amazon, Pastebin, Bearshare, Pirate Bay, The Dark Web. It gives you three different effective attacks to break your password according to their strength, for example, Brute-Force Attack Try almost all kind of combination when you have no idea , Brute-Force Attack with Mask Take less time to recover the password by identifying the password length or characters etc and then last but not least Dictionary Attack Retrieve lost password by searching the combination in Built-in dictionary which is available in many languages. It would have to hack into the 3rd party server to do that! Some demos available online even spend a minute conducting a fake test that pretends to open the file.