Havij sql injection post method. WELCOME TO HACKER DRAGONS WORLD: HAVIJ V1.15 PRO ADVANCED SQL INJECTION TOOL 2012 DOWNLOAD 2019-05-10
Havij Tool

Manual injection syntax support 11. Change the input value and it will yield different output based on the input given. Getting tables, columns and data 35. You have to use some function to protect you, for example or use. Provide details and share your research! Command executation mssql only 32. Enter target url and select http method then click Analyze. But We Have Received Password In The Shape Of Hash.
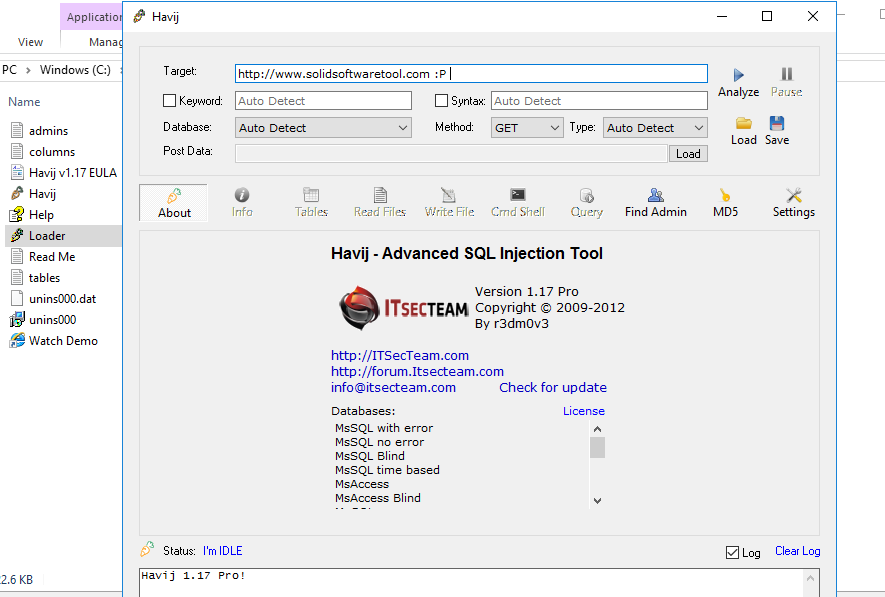
Analysis of the Havij SQL Injection tool

Find Admin Page We Have Got Everything. So there exists at least two columns. You will then see this- Cool! Full customizable http headers like referer,user agent and. Injecting url rewrite pages Pro version only 17. It can take advantage of a vulnerable web application.
Havij Download

Getting one row in one request all in one request Pro version only 26. Enter target url and select http method then click Analyze. It's very useful for penetration testing, and even if it doesn't actually do the work for you, well, you can do it manually, right? Custom keyword replacement in inejctions Pro version only 25. Havij Tool - Search In Google And Download Cracked Version. Havij download can make the most of a vulnerable web program.
WELCOME TO HACKER DRAGONS WORLD: HAVIJ V1.15 PRO ADVANCED SQL INJECTION TOOL 2012 DOWNLOAD
As a result of these integrated configurations, Havji Pro could be used by anybody. So check off the accounts table you can also check off the inventory table if you want to. Automatic type detection string or integer 6. Hmm, a table called Admin. Houston we are go for main hacking launch. Load cookie from site for authentication 15.
[Havij 1.17] Automated and Advanced SQL Injection

It can likewise make the most of a vulnerable web program with several security loopholes. Multi thread Admin page finder 32. You should be seeing something similar to the picture on the right. Getting one row in one request all in one request Pro version only 26. We Will Make Use Of HavijTool Again.
Analysis of the Havij SQL Injection tool
You will then get some output like this- Now, as you can see in the left list box, we have extracted two tables from the scanme database- inventory and accounts. In This Post We Are Going To Learn About A Tool Called Havij. For Finding Admin Page Of Target Site. The success rate of attack on vulnerable targets using Havij is above 95%. Manual queries with result Pro version only 12. Injecting url rewrite pages Pro version only 17. This may also mean that not all attacks will necessarily carry information disclosure or damage — they sometimes only serve to pass a boring afternoon for a high-school kid, playing with a cool tool they found online.
[Sqlmap] SQL Injection using POST method ~ Hacker4WAR

As long as you don't get any errors you should be able to get some information out of your site. We now have a full list of dangerously exploitable data. Reading system files mysql only 33. Dumping data into file Pro version only 27. Do you have all of that? The power of Havij that makes it different from similar tools is its injection methods.
Underground Hacking

Havij download latest version has the most user-friendly Graphical User Interface and automatic settings. There are many ways to do that. Getting tables, columns and data 35. We Have To This Code. Manual injection syntax support 11. Type Homepage Url Of Target Site. You do not need to toggle this database unless you want to, because more likely than not, all the important tables, columns, and rows of data are in the scanme database.
Havij Tool

You Need To Find The Admin Login Page Of Target Site. Now we have a lists of tables, one of them called admin. You can use Havij to check security of your own website. Note: Try to url be valid input that returns a normal page not a 404 or error page. Everyone Can Use Havij For Hacking Websites And For Testing Vulnerabilities.
Analysis of the Havij SQL Injection tool
Multi thread Admin page finder 32. You Need To Find The Admin Login Page Of Target Site. To learn more, see our. What matters is what you do with the input after you have it. Getting tables, columns and data 31. I don't care what they're selling, I just want privileges! If you think there is a need, you just haven't thought of a decent solution yet which usually involves breaking down the data in the query into parts that are standard which you keep server side and parts which are user entered data which you check when they get sent back to you to make sure they are safe.