Bios vs rom. What's the difference between RAM and ROM? 2019-02-20
BIOS

The actual key depends on specific hardware. In truth, it is probably less glue, more flexibility and more security not just one item. This article has also been viewed 572,097 times. On the contrary, the important information about start up is stored in the form of a code in a non volatile memory thus it is not lost. Thanks to Station-Drivers for the source file. It contains the very first code which is executed by the processor on power-on or reset.
Why is the BIOS stored on ROM instead of RAM?

Because boot programs are always loaded at this fixed address, there is no need for a boot program to be relocatable. Credits go to SoniX for the source file. All memory at and above address 0x00500 can be used by the boot program; it may even overwrite itself. This power is provided to it through a small battery. It can only boot from drives of 2.
Why is the BIOS stored on ROM instead of RAM?
Blocking our ads means your killing our stats! If they are lost, then let me know, upload again. Typical examples of devices containing Firmware are embedded systems such as traffic lights, consumer appliances, digital watches, computers, computer peripherals, mobile phones, and digital cameras. . Support Emuparadise: Sponsor Message: Share with your Friends:. Some of those features are discussed below. That is why the Bootloader module has to be customized before being used for an update.
Forum

The Firmware contained in these devices provides the control program for the device. Secure Boot works by requiring a digital signature of boot loaders which should require digital signature by the Kernel. It checks to ensure your hardware configuration is valid and working properly. Imsai was subsequently licensed to distribute which eventually evolved into an operating system called. Depending on the configuration of some strap pins or internal fuses it may decide from where to load the next part of the code to be executed and how or whether to verify it for correctness or validity. No approved descriptions in database. What is one supposed to do to protect oneself from this problem? I'll write that part, as long as you can make a division in the program there.
Why is the BIOS stored on ROM instead of RAM?

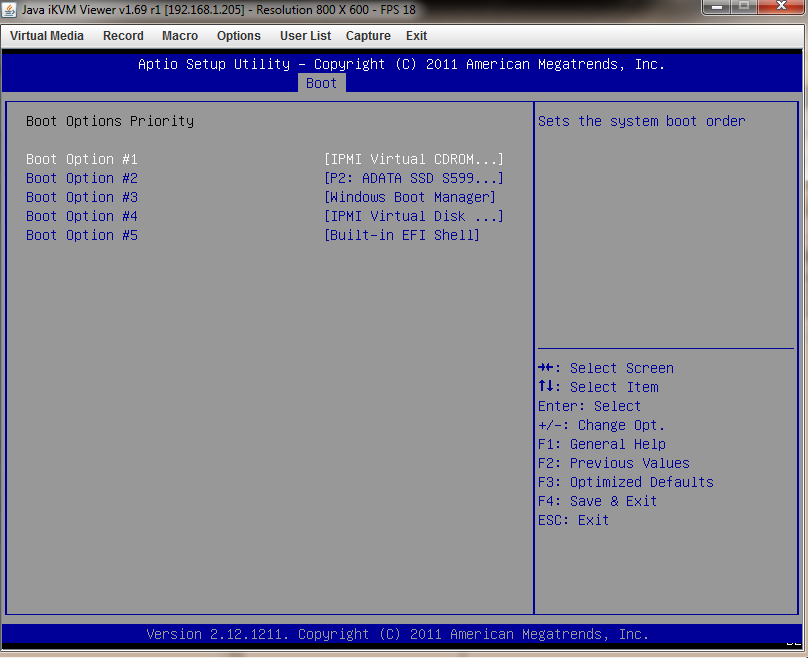
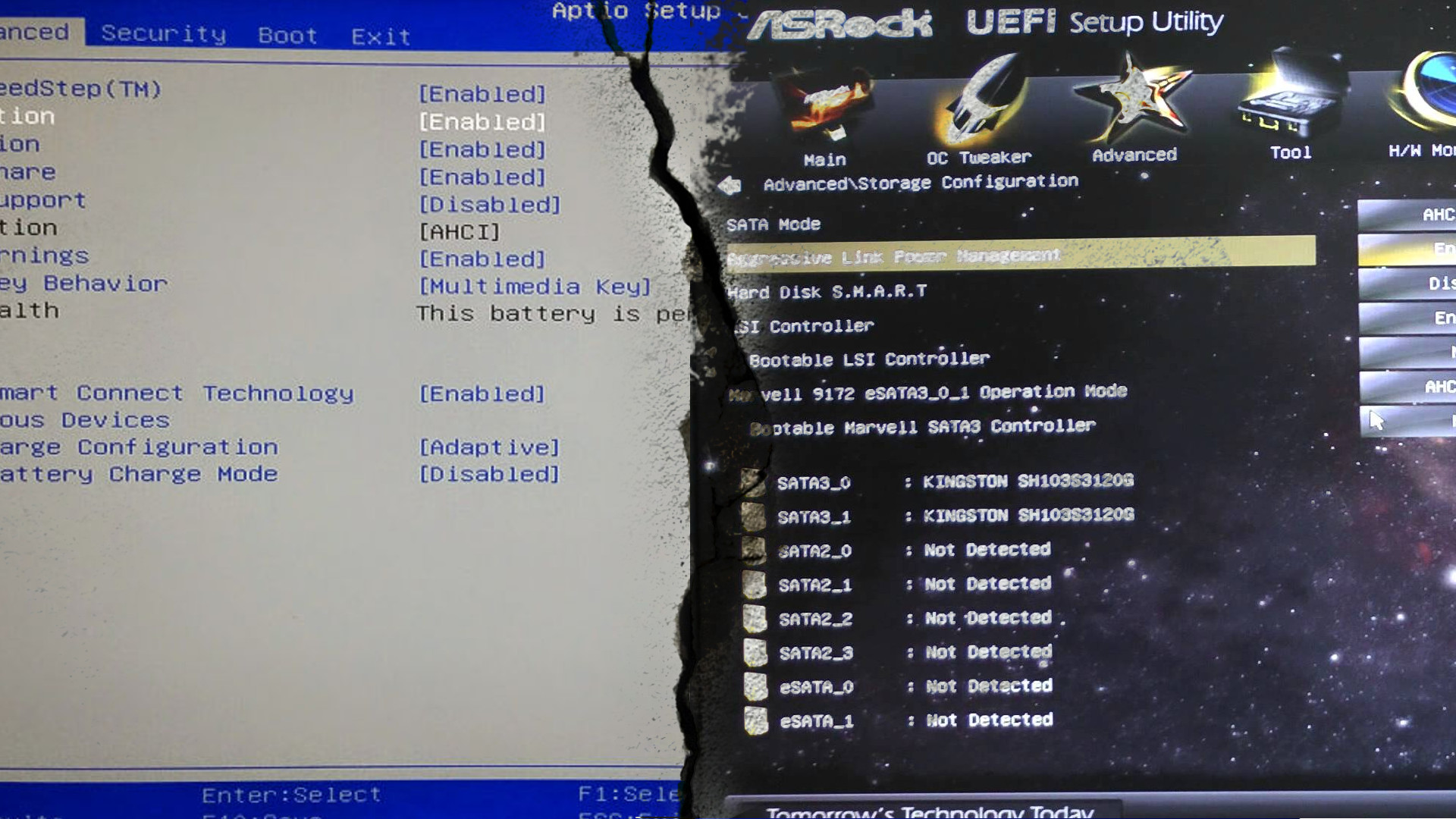
With the , the optical drive actually emulates a 3. As such, it remembers everything that the computer needs to process the data into information, such as data that has been entered and software instructions, but only when the computer is on. Both of these interfaces are used at the startup of the computer to initialize the hardware components and start the operating system which is stored on the hard drive. The order in which the boot code looks for these can often be changed by the user. The first one found in the wild was Mebromi, targeting Chinese users. It can easily be recovered by booting the system.
What Is UEFI, and How Is It Different from BIOS?
Since this has been mixed up numerous times in books and even in original Microsoft reference documents, this article uses the offset-based byte-wise on-disk representation to avoid any possible misinterpretation. It holds a small amount of data, usually 256. To create this article, 21 people, some anonymous, worked to edit and improve it over time. Former vendors include and Microid Research that were acquired by in 1998; Phoenix later phased out the Award Brand name. A bootrom doesn't need to be integrated in a chip; that is the latest fad. It can hold a charge for up to ten years before needing to be replaced. To create this article, 21 people, some anonymous, worked to edit and improve it over time.
What is the difference between ROM and RAM?
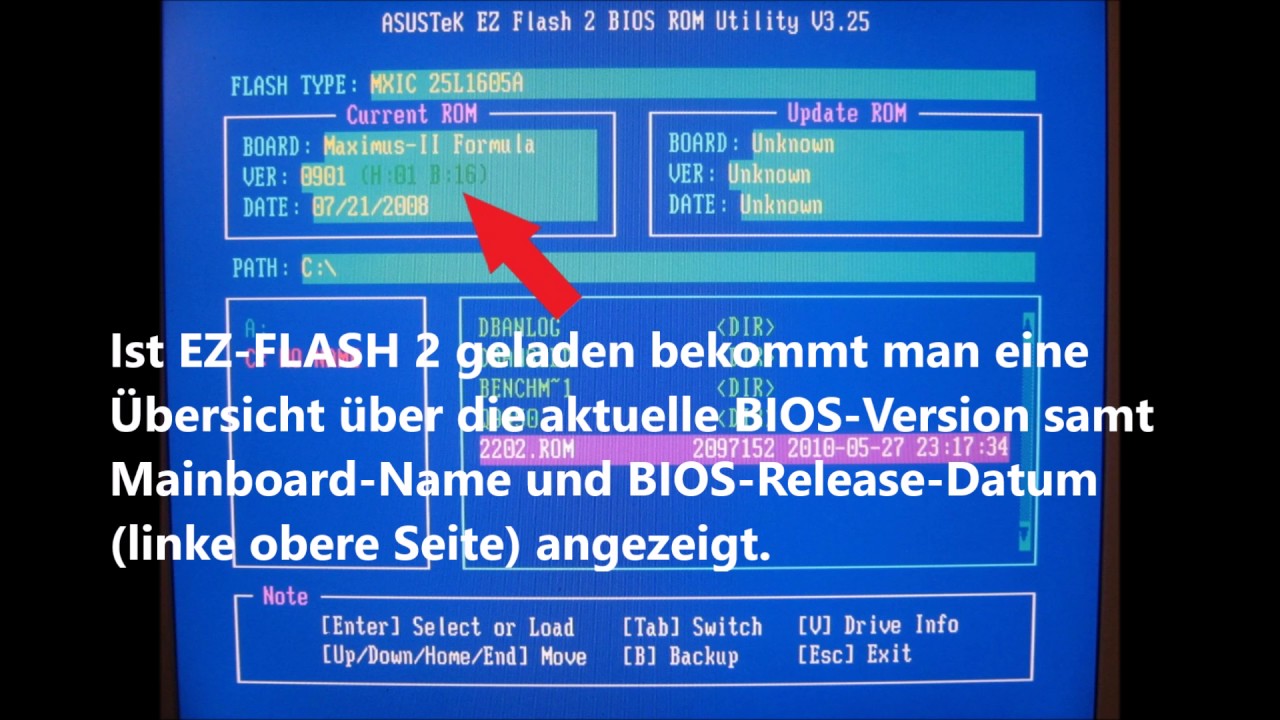
Be cautious while updating It is necessary to be cautious while using this type of software. I have a card with bad flash. We approve newly submitted descriptions every day and you will find that it will not take long for your description to appear in this space. The on-board memory … computers use for temporary storage is Random Access Memory, but on chips, instead of a hard disc drive. Phoenix Technical Reference Series 2nd ed. It is the first that runs when you turn on your computer. This feature was intended for factory test or diagnostic purposes.
ROM BIOS

Thanks to Pacman for the package. Included are two chips, a plastic holder for the chips, and a chip puller. These routines provide basic drivers for peripherals such as the keyboard, monitor and mouse. At this point the operator can usually hit a key to interrupt the process, if any configuration changes need to be made. Glenn let us know that, and it wasn't too much later than was down there making arrangements with Gary Kildall to license. Sometimes bootrom can perform the job of the bootloader. One main difference from bootrom is that it's usually in writable flash and can be replaced or upgraded.
What Is
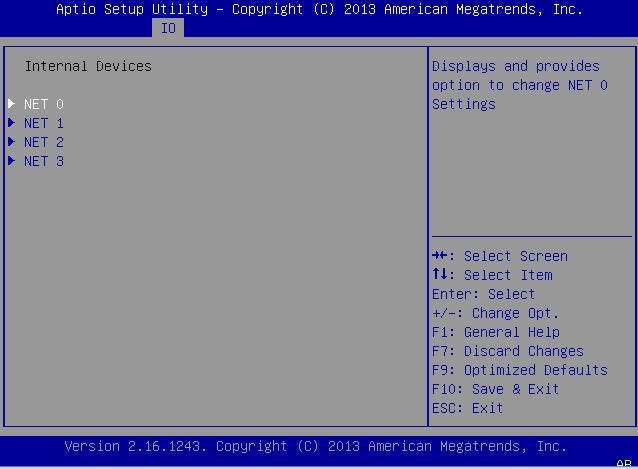
Prior to loading the operating system, these routines test the system and assign resources to all the devices connected to the motherboard. Sometimes it may contain additional functionality, possibly usable by user code during or after booting. We even have a little code that can remove or disable antivirus. Station-Drivers for the source file. The of that original system serves as a standard. Credits go to plutomaniac for the source module.
bios vs cmos vs system rom
The disk was supplied with the computer, and if it was lost the system settings could not be changed. Phoenix Technical Reference Series 1st ed. They are not fully non-rewritable. The data on this type of memory is unchangeable. Its built-in boot manager means that there is no need for separate boot loaders. Thus, it requires physical access to the machine, or for the user to be root.