(tco 3) which of the following is a valid ip address. CCNA DO I KNOW THIS AREADY QUIZZES Flashcards 2019-03-01
IP address

The algorithm never allows collisions to occur. Assume no errors in the link. It is done the same way as all the others. What are the essential elements of change management? For example, the address 168. Available Formats Address es Description References Change Controller Date Registered Last Reviewed 224. All Class B networks have their first bit set to 1 and the second bit set to 0.
IP address

The host is in the 10. However, a Class B has 16 bits to play with. The host always sends packets to its default gateway. Points : 4 Question 3. If a network were to be split into four parts using classful address four different class C addresses would have to be used to serve those networks. The 1s designate that part of the address as being part of the network portion and the 0s designate that part as being part of the host address. Points : 15 Question 3.
What is a Valid IP Address?

Answers A and C are always correct. Points : 4 Question 5. Example 1: Answers for the 255. Points : 4 Question 20. The first numbers in the address specify the network, while the latter numbers specify the specific host. The remaining bits after the subnet are used for addressing hosts within the subnet. Pins 1 and 2 are reversed on the other end of the cable.
networking

They were first described in 1981 and have been in use since 1983. Wireless access point Ethernet port and switch Definition B. The subnet range is 0. Originally a test network, no one contemplated how many addresses might be needed in the future. Computers and devices that are part of internetworking network such as the Internet all have a logical address. However, if you turn the subnet bit off, the value is 0.
News, Tips, and Advice for Technology Professionals
Packets from these networks are not routed across the public internet. Learning routes for subnets directly connected to the router c. There are network classes D, E and F, but these are for special, experimental use and the public does not use them. This upgrade substantially increased the available address space and allowed for 2 128 addresses. If yes, is this a first, last, or middle fragment? What device would you use to connect the computers? What are the four common methods for connecting equipment at the Physical Layer? Class E networks are reserved. Class C network addresses only have eight bits to manipulate into subnets.
IP address

For example, what happens when you use this mask with a Class B network address: 255. The range of addresses between 224. R1 will connect to a physical Ethernet link, with the other end of the cable connected to R2. This will allow more subnets with more hosts per subnet than a Class C network ever could. .
CCNA DO I KNOW THIS AREADY QUIZZES Flashcards

At the time, the 2 32 addresses 4. Class A networks are identified by the first number, while Class B networks use the first two numbers and Class C the first three. Points : 4 Question 6. The private networks are 10. Points : 15 Question 8.
CCNA Certification/Addressing
Points : 5 5 8 32 64 Question 11. The host is in the 10. None of the other answers is correct. Definition Data encapsulation Term Which of the following terms is used specifically to identify the entity created when encapsulating data inside data link layer headers and trailers? It resides in the Ethernet trailer, not the Ethernet header. There are 16,384 possible Class B networks. The multicast addresses are in the range 224. A classful network is a network that has a subnet mask of 255.
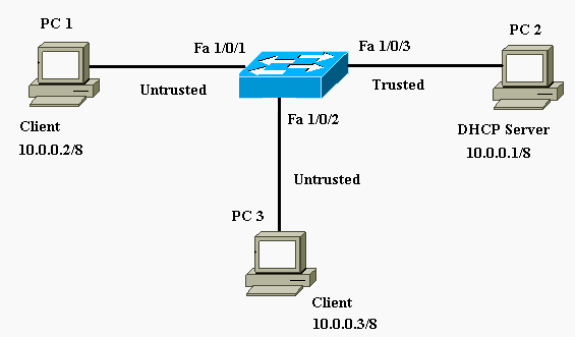
Dynamic Host Configuration Protocol (DHCP)
Points : 15 Question 5. However due to the inefficiencies introduced by this convention it is generally no longer used and is only relevant when dealing with some legacy equipment. Ignore transmission, waiting, and processing delays. Enable clocking for the serial interface - clock rate 64000. The various numbers define the class and identity of the network device. A Class C subnet mask would be 255. Points : 4 Question 15.