Networking protocol numbers. List of Well 2019-01-15
TCP/IP Ports and Protocols
:max_bytes(150000):strip_icc()/free-ftp-56a3239f5f9b58b7d0d08fc4.png)
It was 20 years old. See also ports 80 and 8008. The downside of these services is that they are not available at all locations, they are difficult to set up and troubleshoot, and the equipment is expensive when compared to equipment used for dedicated circuits. Computer scientists and engineers that design networks and technology equipment observe these protocols strictly. If you have 1000 devices, you need to create 1000 static entries in the address translation table, which is a lot of work.
Protocol Numbers
The web server itself listens by default on port 8080. Wireless and wired devices can coexist on the same network. Port though often changed during installation Unofficial 16250 Yes Oracle WebCenter Content: Inbound Refinery formerly known as Oracle. This is an 8 bit field. If we prioritized every packet highly, we'd get dropped calls all the time.
List of TCP and UDP port numbers

Unite automatically hooks into your router using uPnP to dynamically open port 8840, but it can also use a Unite proxy server when you're behind a more restrictive firewall. Summary While it may seem obvious that there are large number of ports that are missing from this list, the purpose here was to just cover the most commonly seen and used protocols. This feature makes them better suited for data services, but they can nonetheless provide some of the QoS features that cell-switched services provide. Whereas cell-switched services switch fixed-length packets called cells, packet-switched services switch variable-length packets. WiFi WiFi Provides wireless internet access. They are assigned by for specific service upon application by a requesting entity.
40 Network Protocols with Port NOs. Transport Protocols and Meanings
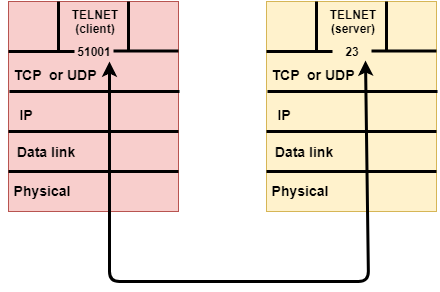
Telnet is very basic; it offers solely character-based access to another computer. Because of the encryption, confidential user information cannot be compromised. The port the server will listen on. This would be similar to driving on a turnpike or express lane with tolls. The port registration is in Section 3. They don't have to worry about acquiring permission or paying royalties to use them. Only the Private Ports 49152-65535 may be used in this manner without registration.
List of IP protocol numbers
Prerequisites: you have to know. Basically, it can track where traffic is coming from, where it is going and how much traffic is being generated at any time. Usually the default port 6136 should be specified. A directory is a set of information with similar attributes organized in a logical and hierarchical manner. Acknowledgements to Scott Bradner, Ken Cates, and Tony Speakman. On most systems, registered ports can be used without superuser privileges.
Networking Port Number And Protocol Abbreviation Practice Set Flashcards by ProProfs

You can help by with entries. Modern operating systems contain built-in software services that implement support for some. This assignment is not permanent and expires at a configurable interval; if an address renewal is not requested and the lease expires the address will be put back into the poll for assignment. If a packet is unacknowledged, the packet is retransmitted a total of 8 times. . Routing protocols are special-purpose protocols designed specifically for use by on the internet.
What are Network Protocols?
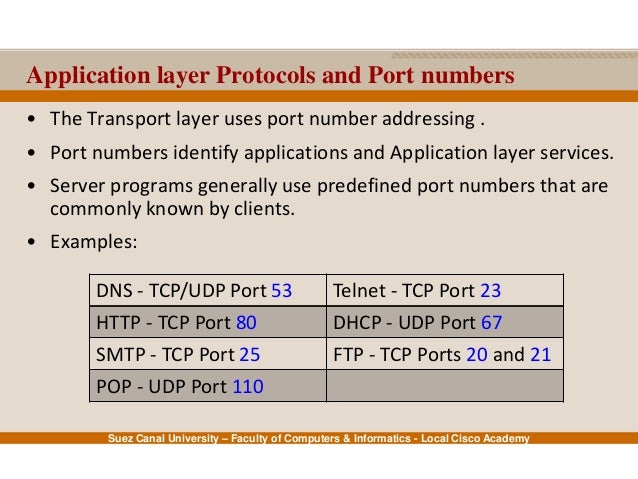
Try Amazon Prime 30-Day Free Trial Online Money Create Amazon Business Account and get more specific offer Visit my Blog for Full theory of Networking Chapter Wise In this video you will learn about Application Layer Protocols and their port number in Hindi. You can help by with entries. This is called name resolution. Which cookies and scripts are used and how they impact your visit is specified on the left. Below, we take a look at these protocols, provides a basic description of their function, and lists the port numbers that they are commonly associated with. Retrieved 2016-10-25 — via Read the Docs.
List of Common Network Port Numbers

Please improve this by adding. Represented in hex, it is 12 characters in length, where each character is 4 bits. In reality however, this is probably not true. Loyola Hans-Werner Braun Harry Forsdick Howard Hart Internet Assigned Numbers Authority 1995-06 J. Computers, and virtually any device that communicates on the internet, are law-abiding citizens as well! Please keep in mind that comments are moderated according to our comment policy. Ultra Fractal enables you to distribute calculations over multiple computers connected with a network. This article takes a look at these protocols, provides a basic description of their function and lists the port numbers that they are commonly associated with.
40 Network Protocols with Port NOs. Transport Protocols and Meanings
This can be a source address or a destination address. Network Protocols So you need to get to your aunt Gretchen's house for a Sunday dinner. Network Protocols also aren't seen by the average person online, but the framework they define are the reason we have such a stable and reliable internet. The ColdFusion server configuration is built on top of Tomcat, also called the built-in web server. Hopefully the contents of this article will help in determining the correct port number to use when implementing these services.
List of TCP and UDP port numbers
The port number identifies what type of port it is. A T3 line is typically installed as a major networking artery for large corporations, universities with high-volume network traffic and for the backbones of the major Internet service providers. Because AppleTalk is routable, clients can access servers from any network number. Zones allow servers, printers, and clients to be grouped logically for the purpose of resource access. You can test out of the first two years of college and save thousands off your degree. Network protocols include mechanisms for devices to identify and make connections with each other, as well as formatting rules that specify how data is packaged into sent and received messages.