Network spoofer github. Network Spoofer download 2019-02-26
Hacking with Android Part 2: Network Spoofer (HD)

I naively assumed if the card had that feature the terminal could force it to be used. It is a generally used mechanism to hide the plain text info from the others even thought there is only one way to hash the password you can even retrieve the password using different techniques. This easy to use tool allows user to connect to any database and browse or modify data,run sql scripts, export and print data. With this trick you can easily Prank your Friends, Family and Coworkers. It has two modes: defensive and offensive. The tool supports both session- and basic-authentication.
NTP spoofer to change the date of any victim to the year 2035 · GitHub

It also allows any data to be added to the packet. Once Further Cleared the 23 Assessment , You Will Eligible for Take Online Fundamental Exam. Unicornscan is a new information gathering and correlation engine built for and by members of the security research and testing communities. WifiScanner is a tool that has been designed to discover wireless node i. But I had a way to create a key without ever possessing the original.
Prevent Your Network from Being ARP
Yes everyone is going to run around and scream 'security!! Meals were also kept track of by card. I picked these things, because they are things I personally strive to keep learning. Unfortunately a disproportionate amount of theft occurs by bypassing the chip-and-pin system. There are over 600 tools in BlackArch's package repository. This tool is intended to demonstrate the importance of choosing strong passwords. Its developers have spent hours stuffing it with broken, ill-configured, outdated, and exploitable software that makes it vulnerable to attacks.
MagSpoof

Ncrack is a high-speed network authentication cracking tool. For your particular definition, or something close to it, who would you say it gets close? Edit: Also, that is considered fraud and your best not testing it, unless you like the prison environment. Its also a great tool for experienced pentesters to use for manual security testing. I mean, it's one thing to break stuff to get in, or conspicuously pick a lock, it's another to casually slide a card like everyone else and leave no trail other than maybe video surveillance or access logs showing the same card being used at two ends of campus faster than possible which nobody will check until something bad happens and they go looking at that data. While wardriving is its main use, the application also facilitates the verifying of network configurations. The Web Application Vulnerability Scanner Evaluation Project, is a vulnerable web application designed to help assessing the features, quality and accuracy of web application vulnerability scanners.
Nice DNS Spoofer · GitHub
The configuration of a Firewall is done by combining more than one rule. It currently features three different tools db2disco, db2fakesrv and db2getprofile. This can be useful for searching for data on the website offline such as email addresses, information useful for social engineering, hidden password files believe me, I have found a few , intellectual property, or maybe replicating a login page for a Evil Twin site to capture login credentials. Oscanner is an Oracle assessment framework developed in Java. The tool works by collecting and analyzing cookies issued by a web application for multiple users.
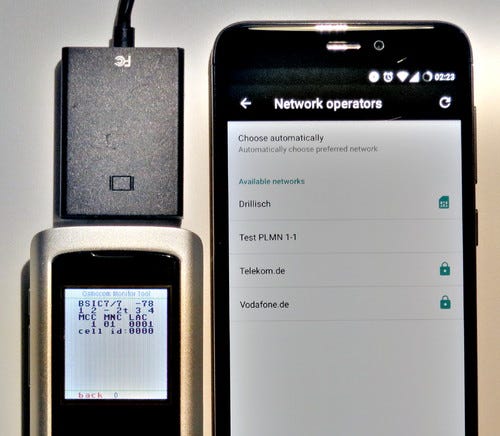
Sniffer, Spoofer & Portscanner

Take the final exam to earn your certificate. On Friday, March 6, 2015, mnbvcxzl90 wrote: Seems to be, I have not payed attention to the ip addresses but my network follows 10. Toggle this mode on and off using the keyboard shortcuts F2 or… Short Bytes: Do you know about Mozilla Thimble code editor? The main goal is to print the list of connected equipments in your network. The term applied to the person who uses his computer and laptop to access the unauthorized data. I knew from people losing their cards which continued working some places but not others there was a relationship in the issuing. The terminal will send the magstripe data online when authorizing the transaction, and the backend systems will identify the corruption in magstripe data and identify it as fraud.
MagSpoof

. The tools are still in development but tend to be quite stable. It was built to help companies secure their networks by proactively testing all their hosts and networking devices for poor passwords. A mirror of deliberately insecure applications and old softwares with known vulnerabilities. It integrates with Rapid7's Metasploit for vulnerability exploitation VulnDetector is a project aimed to scan a website and detect various web based security vulnerabilities in the website.
Sniffer, Spoofer & Portscanner

I would recommend using this option when there is constant packet flow between your device and the gateway. But, the whole card system is not built on absolute security but on risk-management and fraud detection, that is somehow balanced with customer convenience. A tool for automated security scanning of web applications. The terminal has no method to determine if the card is Chip and Pin enabled aside from the magstripe. If anything, merchants seemed more able to deal with them than 10 years ago, where I occasionally had a clerk who couldn't figure out whether to swipe extremely slowly, or quickly enough to set fire to the equipment.