Ms sdl tool. Microsoft Threat Modeling Tool 2019-03-17
Microsoft Security Development Lifecycle
Formal methods are based on mathematics and provide state of the art techniques for secure software development. To make a trustworthy smart band, we must derive the security requirements of the system first, and then design the system satisfying the security requirements. Ability to define specific security controls and automatically correlates them with specific threats. We hope that include yours. At runtime it is then important to support the DevTs with, possibly automated, techniques to test whether the identified threats are indeed exploitable.
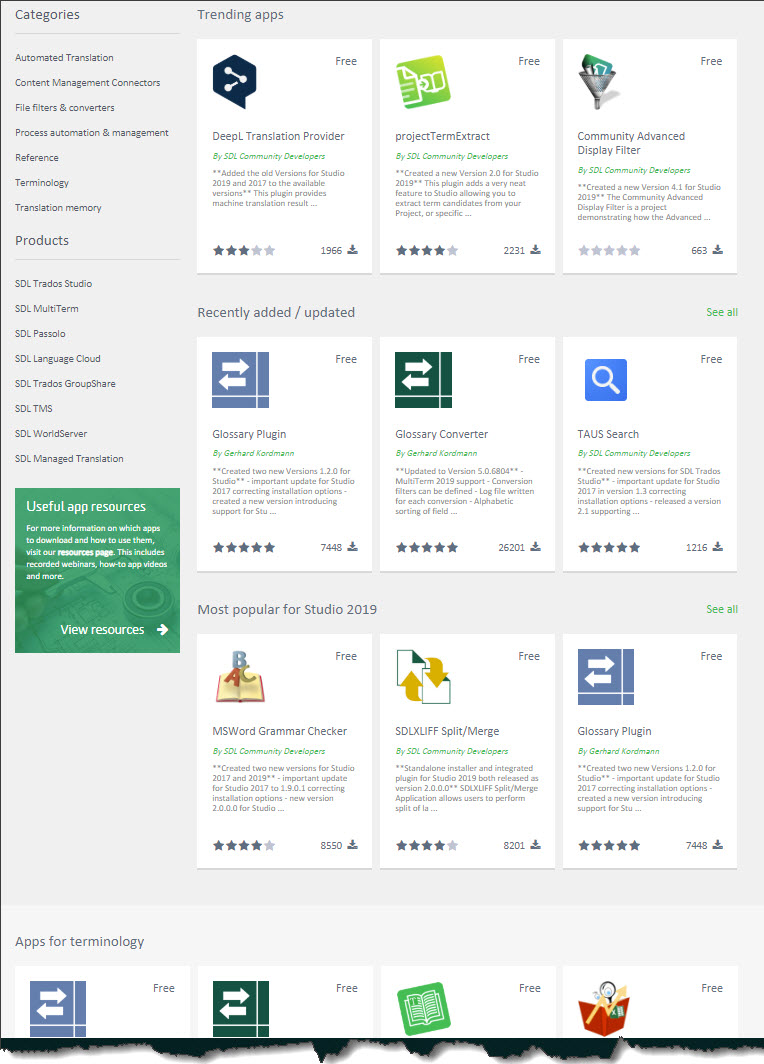
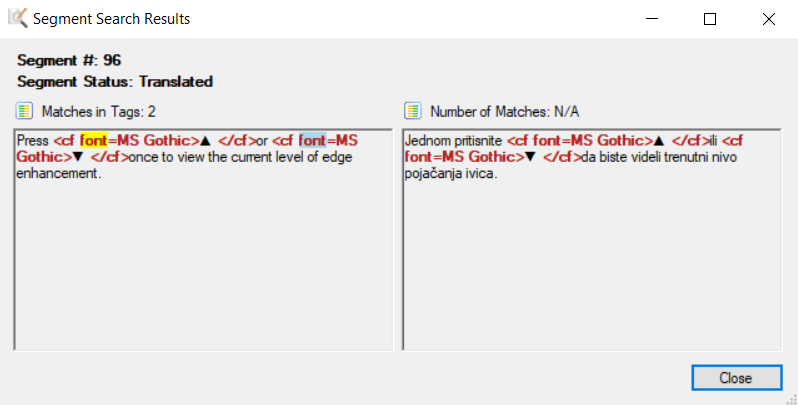
SDL Trados

Threat modelling is performed at the early stages of software development process with the purpose to identify all possible threats that may cause harm to the software applications. This way, other stakeholders are able to verify the trustworthiness properties in a later stages, e. The authors believe that the current software development and operations approaches need some improvement in order to successfully address the complex issue of delivering trustworthy services. We implement and verify our approach by building a tool for automated threat analysis of software architecture diagrams. Ability for multiple stakeholders to access the tool and make changes at the same time, and in real time. The security of software systems can be broadly divided into two categories namely external security and internal security.
SDL Trados

Ricardo begins by selecting the first item on the list. It allows software architects to identify and mitigate potential security issues early, when they are relatively easy and cost-effective to resolve. Threat modelling is one of the approaches to identify security requirements and helps to add them into the design of the software systems. Построение модели угроз с помощью Microsoft Threat Modeling Tool. They checked the document into source control and continued with development.
Two free security tools from Microsoft SDL team
Any of these three approaches work. Want to create your own template or submit a new one for all users? To support this process over the entire vehicle's lifetime, a generic framework is needed. Threat modeling is a core element of the. This is typically done by creating a threat model of a system, enumerating the potential threats, and then devising mitigation options based on the discovered threats. The change in delivery mechanism allows us to push the latest improvements and bug fixes to customers each time they open the tool, making it easier to maintain and use.
Microsoft Security Development Lifecycle Resources
To identify security requirements of software systems, many techniques have been developed. New comfort features, safety functions, and a number of new vehicle-specific services will be integrated in future smart vehicles. Ability for users to access the tool. Seemed like Ricardo and Cristina missed quite a few important corner cases, which could be easily compromised. This is validated in the context of a large-scale industrial software development context providing some initial empirical analysis. Sometimes, it refers to a complex blend of the two.
Microsoft Security Development Lifecycle Resources

Role Based Access Control for Different Stakeholders. His skepticism is a complement to threat models. Ability to build and maintain 1. Threat modeling meetings When Ricardo sent his threat model to his colleague using OneDrive, Ashish, the tester, was underwhelmed. As Ricardo went into the threats under Information Disclosure, he realized the access control plan required some read-only accounts for audit and report generation.
Microsoft Security Development Lifecycle Resources
It shows how HazOp can be employed on a diverse range of technologies to correctly identify deviations from use cases that may represent a violation to the security objectives of the product. The reader will also learn how to apply and, potentially, adapt HazOp to accelerate the discovery of system threats as well as the derivation of test scenarios for purposes of security evaluation. Once he does that, he can copy the document link and share it with his colleagues. Gone are the days when software systems can be built without regard for security. These are analogous to thinking about assets, attackers, or software design.
Microsoft SDL Threat Modelling Tool
Threat Comparison and Trend Analysis. Ricardo: Let me show you. MiniFuzz is a simple file fuzzer that is designed to ease your introduction into fuzz testing even if your team has limited security experience. This paper takes one such technique, HazOp, and applies it to Intel hardware and software shedding some light on the mechanization of use-case-based threat analysis. Roslyn analyzers can also provide design-time analysis of code files that aren't open in the editor if you enable full solution analysis. Even though use cases may be properly documented and routinely used during the development cycle for elicitation of functional requirements, non-functional requirements, such as security, are often neglected due to the priority new functionality receives over other aspects of the product, as well as the complexity of analyzing and planning for the unexpected. The current software development method- ologies and best practices need some improvement in order to successfully address the complex issue of delivering trustworthy systems.