Microsoft windows xp professionnel exploit. MS03 2019-01-11
Metasploit modules related to Microsoft Windows Xp

That didn't surprise another security expert. Reverse bind shell is very effective to evade default firewall settings, this is because the default firewall setting is usually allow everything from the trusted zone to the untrusted zone and block unsolicited traffic from untrusted zone to the trusted zone. Code execution may be possible however this module is only a DoS. Maybe you can send compressed file with a bunch of picture with your malicious file inside it. We shall check them out in some other post.
Metasploit modules related to Microsoft Windows Xp

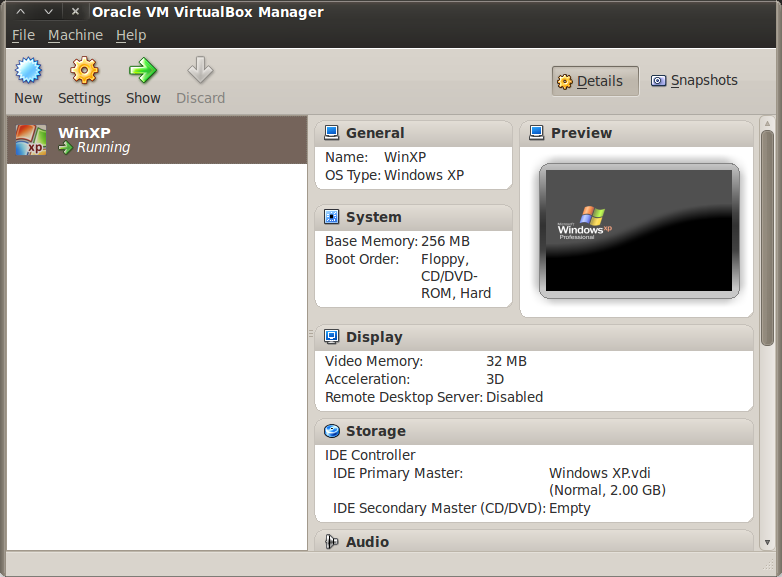
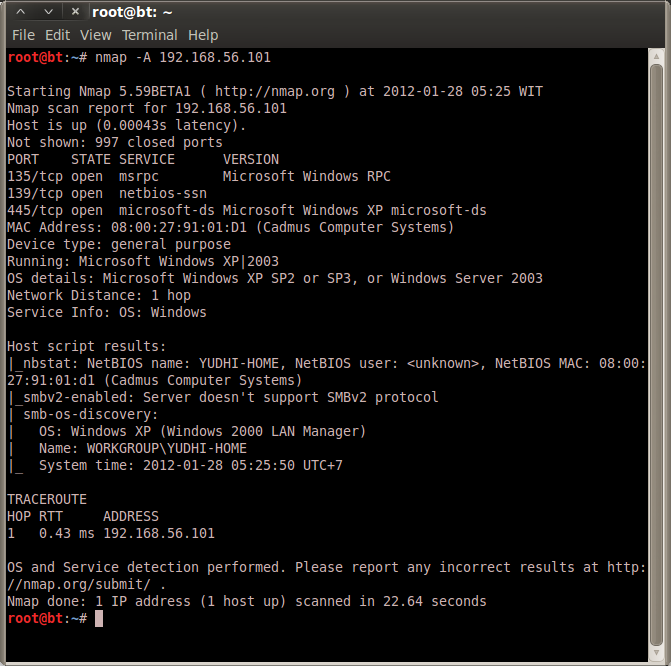
Using notepad to track pentests? So keep hacking till then. This vulnerability uses the 'Escape' metafile function to execute arbitrary code through the SetAbortProc procedure. To view the available switch for this exploit and payload, type show options command. It will come back to the meterpreter session. Scan for open ports Before exploiting the xp machine with metasploit it is a good idea to scan for open ports using nmap to confirm that ports are accessible and accepting connections. This means that for any given system, you only get one chance to exploit this flaw. Check options once again Now that we have selected out payload, its time to check the options once again.
Microsoft Windows Xp Professional
Exploit is like a backdoor found within a program bug usually this bug is a buffer overflow bug which caused the register to be overwritten, the overwritten register is loaded with the payload you select. Understand the target root bt:~ nmap -sS -Pn -vvv -O 192. This service is used to share printers and files across the network. Leveraging the Metasploit Framework when automating any task keeps us from having to re-create the wheel as we can use the existing libraries and focus our efforts where it matters. Exploiting this flaw involves two distinct steps - creating the registry key and then triggering an overwrite based on a read of this key. Since the service is hosted inside svchost.
Microsoft Windows Xp : List of security vulnerabilities

Cluley declined to identify the site, saying only that it was dedicated to open-source software. Play around it and when done, type 'exit' and press enter. Although Microsoft did not share details of the attack, other researchers filled in the blanks. The functionality includes common post exploitation tasks like scanning the target's network, hardware, accessing devices etc. Now you can use your mouse to interact with the victim desktop as if it were your own.
'Microsoft Windows XP Task Scheduler Universal Exploit (MS04
The payload I will use here is reverse tcp binding also known as reverse bind shell. It is running the microsoft-ds samba service. Once the key is created, it cannot be recreated. The tactic was one of two that Microsoft said last week were the likely attack avenues. The fact that an exploit based on Ormandy's code was published June 10 for the open-source Metasploit hacking toolkit probably was also a factor, said Storms in an instant message exchange. A reboot is required to restore proper functioning of an exploited system.
Hackers Exploit Windows XP Zero

Module type : exploit Rank : good Platforms : Windows This module exploits a stack buffer overflow in the Windows Plug and Play service. Meterpreter has lots of inbuilt scripts that can do lots of other things on the victim machine. This exploit works on windows xp upto version xp sp3. Module type : auxiliary Rank : normal This module exploits a stack buffer overflow in the svchost service when the netware client service is running. Meterpreter can also start a vnc session.
concerned about
Select the payload Next comes the payload. Microsoft has yet to develop a security patch for this exploit, but it recommended that users enable their firewalls and download security updates,. Reverse bind shell — Is the opposite, the victim machine establishes a legitimate connection to the malicious remote location and creates a shell of the victim machine. When processing a thumbnail bitmap containing a negative 'biClrUsed' value, a stack-based buffer overflow occurs. Level : Medium Victim O. Enter 'exploit' and hit enter. This is the ip address of the victim machine that is running the vulnerable windows xp.
Exploit code puts Windows XP and 2000 at risk

Microsoft's group manager of response communications. In this example the ip address is 192. Here is a quick example root kali:~ nmap -n -sV 192. In this example the ip address is 192. Upon login for each session, Windows will create a new instance of winlogon. Since the service is hosted inside svchost. There's a lot of people who's uncomfortable when they are migrating into new Operating System, so that's why they still stand in their old O.
Hacking Windows XP SP3 via MS11
Ormandy, who also posted proof-of-concept attack code, defended his decision to reveal the flaw only five days after reporting it to Microsoft -- a move that Microsoft and other researchers questioned. Launch the exploit Now metasploit is all configured to launch the exploit. If you were to scan a range of ip addresses to discover online windows xp machines, then most of them would likely be patched through automatic updates. It is this service that is vulnerable to the above mentioned exploit and would be hacked next using metasploit. Meterpreter have lots of commands you can see all of them by typing help and hit enter. In the picture below I'm just write the needed switch to configured to generate the malicious doc file. That didn't surprise another security expert.
Microsoft Windows Xp : List of security vulnerabilities
Ormandy, who also posted proof-of-concept attack code, defended his decision to reveal the flaw only five days after reporting it to Microsoft -- a move that Microsoft and other researchers questioned. The exploit is quite easy to launch. The fact that an exploit based on Ormandy's code was published June 10 for the open-source Metasploit hacking toolkit probably was also a factor, said Storms in an instant message exchange. You are only allowed one attempt with this vulnerability. The exploit is quite easy to launch. Gregg Keizer covers Microsoft, security issues, Apple, Web browsers and general technology breaking news for Computerworld. Yep everything was set up so nice until this step, the next step you need to send your malicious file and make sure the victim open it in thumbnail view mode.