Microsoft siem. Urgent 2019-02-08
Security Information and Event Management Tool: SIEM Software
Is that a risk if a security team can see the subject of a user email to another? The company purchased more than ten companies a year between 2005 and 2008, and it acquired 18 firms in 2006, the most in a single year, including , , , , Software, and. Continuously monitor the security of IoT devices, machines, networks, and Azure services, including your Azure IoT solution from edge devices to applications, using hundreds of built-in security assessments or create your own in a central dashboard. Since the question is about a third party software, I'd like to suggest you to contact the LogRhythm support. Microsoft Azure Sentinel: Cloud Plus Cross-Platform Developing Azure Sentinel is a dramatic move for a range of reasons. Can this be used to data or info leakage? Azure Sentinel also taps into machine learning algorithms that are based on the experiences of Microsoft's security team over the years of providing security in the cloud. Here are some others to consider.
Microsoft SIEM
Although advancements in machine learning are helping systems to flag anomalies more accurately, analysts must still provide feedback, continuously educating the system about the environment. You can try it out here: If you do try it out, then: 1. Software — 168 November 6, 2014 Video games 2. Security Center gives you defense in depth with its ability to both detect and help protect against threats. The acquisition, scheduled to close in early 2014 pending regulatory approval, will not include the mapping service or the infrastructure division , which will be retained by Nokia.
Security Information and Event Management Tool: SIEM Software

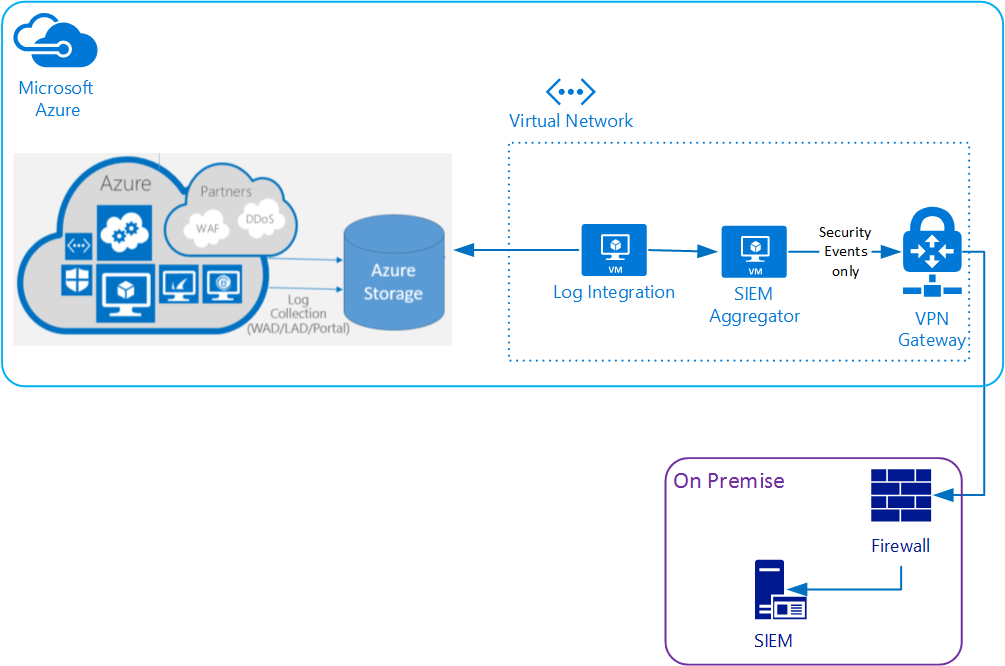
In this way, the volume of information being communicated and stored can be reduced. Note Any token you create is bound to the admin who created it. This means that if the admin user is removed from Cloud App security, the token will no longer be valid. You can use Microsoft Graph to build apps that connect to a wealth of resources, relationships, and intelligence, all through a single endpoint. The Microsoft Cloud whether is Office365, Azure and others holding trillions of data about each action that made in the systems and allow us to analyze the information that belongs to each tenant.
List of mergers and acquisitions by Microsoft
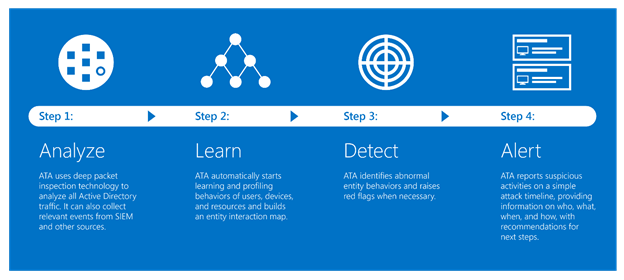
By using artificial intelligence, Azure Sentinel serves as a unified location for tracking security issues across an enterprise. One downside is a lack of threat intelligence feeds out of the box, forcing users to buy or incorporate additional threat intelligence tools. A paid launch date has not been disclosed. You can type -h at any time to get help. As a leader in security event collection and management, ArcSight is able to deliver best-in-class solutions to its clients. If your customer is happy to consider a cloud solution then Microsoft Operations Management suite is the long term direction.
Office 365 Logs integration with SIEM Solutions
Azure Sentinel is available immediately, you can automatically scale to meet your organizational needs, and only pay for the resources you need. In upcoming releases, we will enrich the data set with security recommendations. A major trend is the growing use of behavioral analytics and automation to filter out less urgent alerts so security teams can focus on the biggest threats. If you're just looking for Windows audit event collection, it may work. Hi Syed Fahad Ali, I'll try to answer some of your questions. You must ensure that the product is compatible with all of your required logging needs and that they can be parsed and normalized. ArcSight's open, scalable, and highly effective platform allows Obrela to provide top-level SecOps to its customers for critical cybersecurity needs.
What is Microsoft Azure Sentinel?
On the Pre-Installation Summary page, select Install. Your patience and understanding will be highly appreciated. Thanks in advance Rgds, Nick. Review the summary on the next page and select Next. The general platforms to work with is: Microsoft Graph — platform that connects multiple services and devices and interact with the data of trilithons of users in the Microsoft cloud.
What is security information and event management (SIEM)?

Review the summary on the next Connector Setup summary page and select Next. Repeat Attack-Network Intrusion Prevention System Early warning for scans, worm propagation, etc. Please provide a Corporate E-mail Address. Our subscribers rely on FierceTelecom as their must-read source for the latest news, analysis and data on the intersection of telecom and media. Ideally, an incident response process should also be in place, with corresponding policies and resources to respond to security incidents. Please or discuss this issue on the. Experts advises will be highly appreciated, please.
Security Incident and Event Mangement (SIEM) and ForeFront

. Ill start with two answers: 6. It not only monitors security in Azure cloud environments, but also in rival cloud environments such Amazon Web Services. Mobile lock screen software — 185 September 28, 2015 Adxstudio Inc. Alert on 3 or more failed logins in 1 minute from a single host. Standard tier helps you protect your applications running on Azure App Service by flagging behavior that could pass through web application firewall instruments.
Microsoft announces Azure Sentinel, a cloud

You should now see the Install Complete page. Turn on Standard tier to mitigate this threat. The Intelligent Security Graph process includes: Machine Learning, big-data analytics, advanced security analytics and others. For instance, Sentinel beta testers can import Office 365 data for free. Get a unified view of security across all of your on-premises and cloud workloads, including your Azure IoT solution.