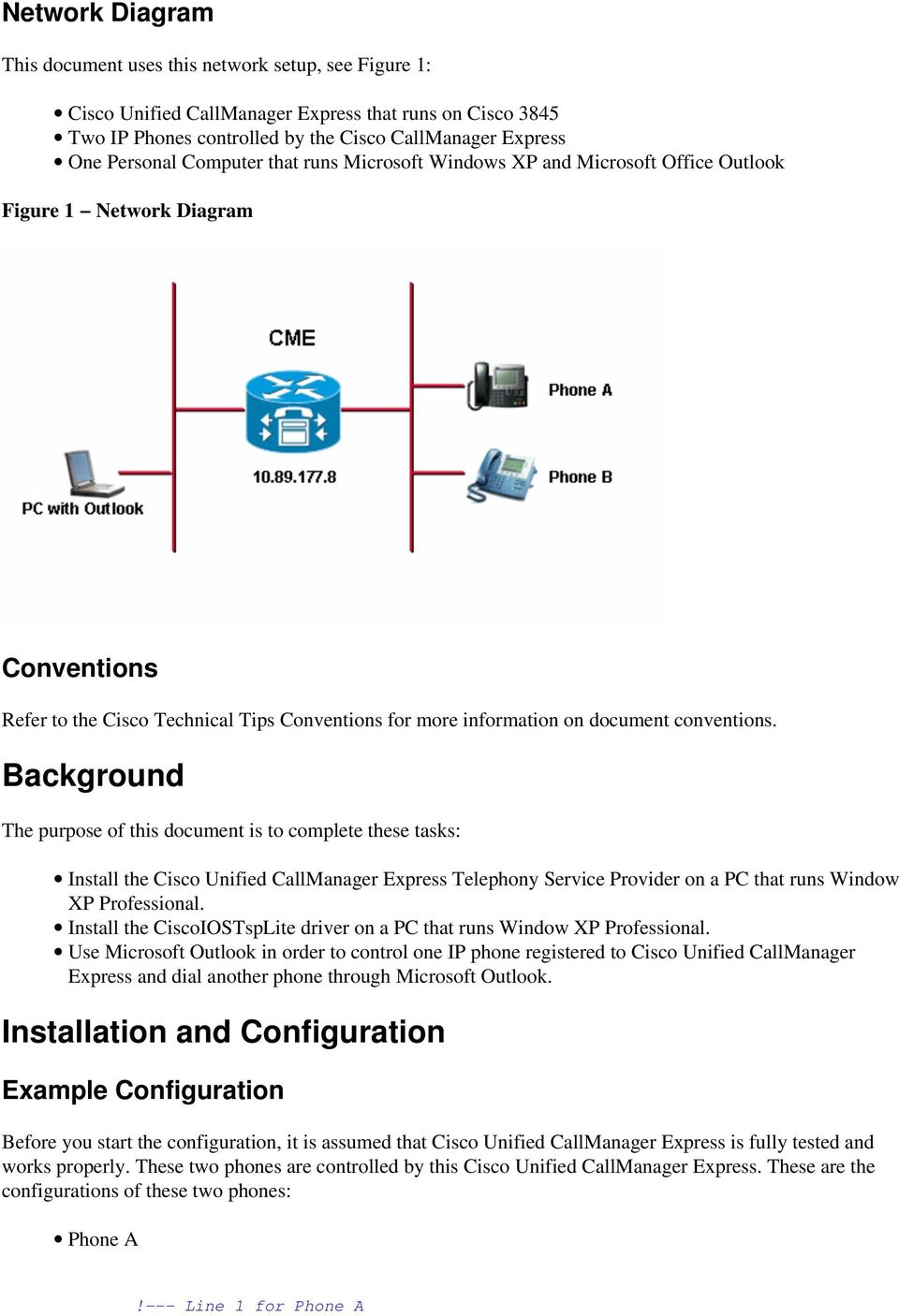
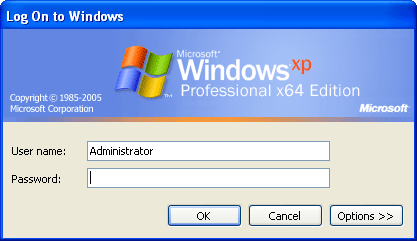
Microsoft outlook for windows xp professional. Download Windows XP Professional and Office 2003 Professional: Better Together from Official Microsoft Download Center 2019-01-14
Microsoft Security Bulletin MS08

This sets the security level for all Web sites you visit to High. This is especially true if you don't have any installation disks because you either purchased Office pre-installed on your computer, or your computer came with a Trial version of Office. Are you wanting to modify the default path or are you just curious? An such as the can improve how quickly results are returned after a search is performed. Security updates are available from , , and. Archived from on December 18, 2001. Lastly, if you purchase from a third-party vendor, make sure you can return the product if necessary and know your return window often 15 or 30 days. Archived from on March 30, 2001.
How to Download Outlook Express for Free

If purchasing from a third party, read all the comments and install as soon as possible so you can get a refund if the product won't work on your computer. You can streamline testing and validating Windows updates against installed applications with the components included with. Archived from on December 15, 2002. Microsoft cannot guarantee that you can solve problems that result from using Registry Editor incorrectly. After you set Internet Explorer to require a prompt before it runs ActiveX controls and Active Scripting in the Internet zone and in the Local intranet zone, you can add sites that you trust to the Internet Explorer Trusted sites zone. Customers without an Alliance, Premier, or Authorized Contract can contact their local Microsoft sales office.
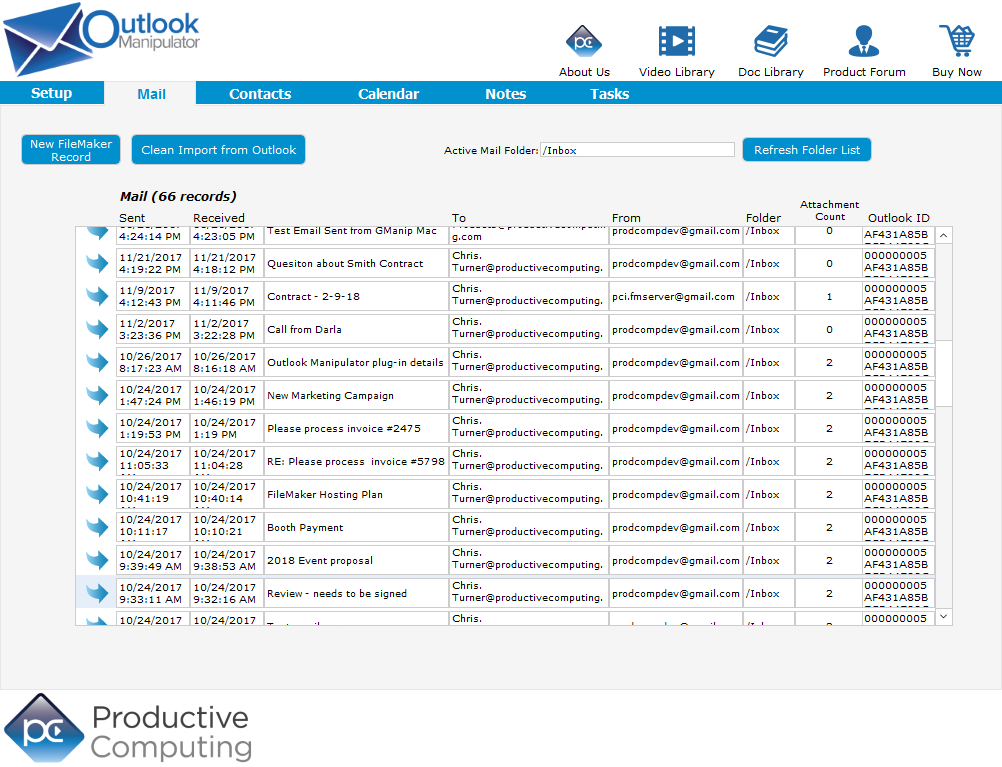
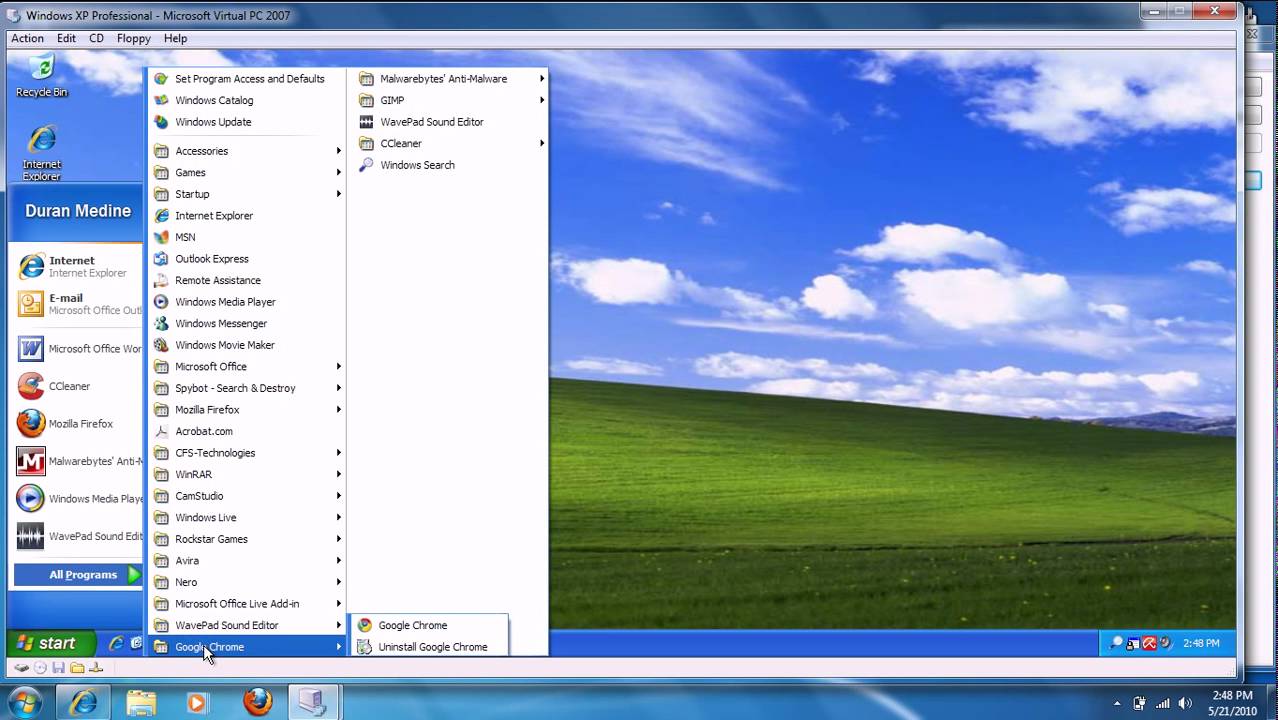
Outlook Express on Windows XP
What does the update do? Product activation does not require. All service packs were made available as separate Client and Full File updates. If the file or version information is not present, use one of the other available methods to verify update installation. In August, Microsoft released Office 10 Beta 1 for product evaluation purposes. Archived from on January 3, 2018. See Office 365 Not Compatible - is always the latest Office version.
Update for Outlook Express 6.0 on Microsoft Windows XP (KB918766)
Note Setting the level to High may cause some Web sites to work incorrectly. When this security bulletin was issued, had Microsoft received any reports that this vulnerability was being exploited? Warning If you use Registry Editor incorrectly, you may cause serious problems that may require you to reinstall your operating system. You can find additional information in the subsection, Deployment Information, in this section. If the user viewed the Web page using Internet Explorer, the vulnerability could potentially allow information disclosure. No user interaction is required, but installation status is displayed. If they are, see your product documentation to complete these steps.
How to disable/remove outlook on windows xp professional?
Microsoft calls this offering Office 365. This log details the files that are copied. Archived from on December 16, 2002. See Office 2013 Support ends 11-Apr-2023 Compatible. During this period Office 10 was characterized as an interim release between its predecessor, Office 2000 and a future version, and was planned to include new formatting options; integrated speech recognition; improved collaboration capabilities and enhanced support for web services; and a complete with. Some online stores sell an Office suite and show the retail box, but don't mention that the box contains only a product key for activating the software after establishing a Microsoft account and downloading the actual software.
Where is the default location for PST files in Office 2010 in Windows XP? What about Windows 7?

Cons: 10 characters minimum Count: 0 of 1,000 characters 5. Microsoft recommends that customers apply the update at the earliest opportunity. Archived from on December 14, 2002. To determine the support life cycle for your software release, visit. Microsoft disclaims all warranties, either express or implied, including the warranties of merchantability and fitness for a particular purpose. For more information, see the. For more detailed information, see : Summary list of monthly detection and deployment guidance articles.
How to disable/remove outlook on windows xp professional?

Note Attributes other than the file version may change during installation. The objective of Office 365 is for the end user to always install the automatic upgrade to the newest version when notified. For more information about the supported installation switches, see. Updated: September 1, 2018 We've consolidated this information from Microsoft's websites and provided links where possible, but please see our Disclaimer below. Other releases are past their support life cycle. To help reduce the chance that a restart will be required, stop all affected services and close all applications that may use the affected files prior to installing the security update. For more information about this behavior, see.
Office XP on Windows 10

You'll notice we refer to the Windows Compatibility Center in our charts when providing Microsoft's official position on compatibility. While the attack vector is through a Web browser, the actual vulnerability is within a component of Outlook Express. Let's discuss the changing landscape of software buying. In no case, however, would an attacker have a way to force users to visit these Web sites. For more information about the Microsoft Update Catalog, see the.
Microsoft Office & Windows Version Compatibility Chart
Click on email and select Outlook Express from the list of available email apps. Archived from on June 23, 2001. Users can configure speech recognition settings, including pronunciation sensitivity in voice command mode, accuracy and recognition response time in dictation mode, and microphone settings through the Speech applet. Internet Explorer are part of a system that divides online content into categories or zones, based on the trustworthiness of the content. The vulnerability could allow information disclosure if a user visits a specially crafted Web page using Internet Explorer.
Microsoft Office XP Professional
For more information about the extended security update support period for these software versions or editions, visit. Note Depending on the version of the operating system or programs installed, some of the files that are listed in the file information table may not be installed. To see all available suites, go to the Microsoft website and click on Office under Products. However, if a user clicks a link in an e-mail message, the user could still be vulnerable to this issue through the Web-based attack scenario. Removal Information To remove this security update, use the Add or Remove Programs tool in Control Panel. You can do this by setting your browser security to High.