Malwarebytes user account control. How User Account Control works (Windows 10) 2019-01-20
User Account Control (Windows 10)

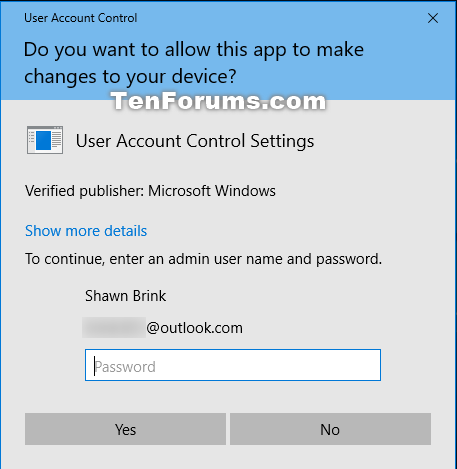
Administrators can also be required to provide their credentials by setting the User Account Control: Behavior of the elevation prompt for administrators in Admin Approval Mode policy setting value to Prompt for credentials. Waiting to see if the second solution did the trick. Because those protections are never perfect. I'm looking into this question myself, I posted a question about the difference between javascript and executables here recently. Rather than fix the hole, the owner puts fly traps inside.
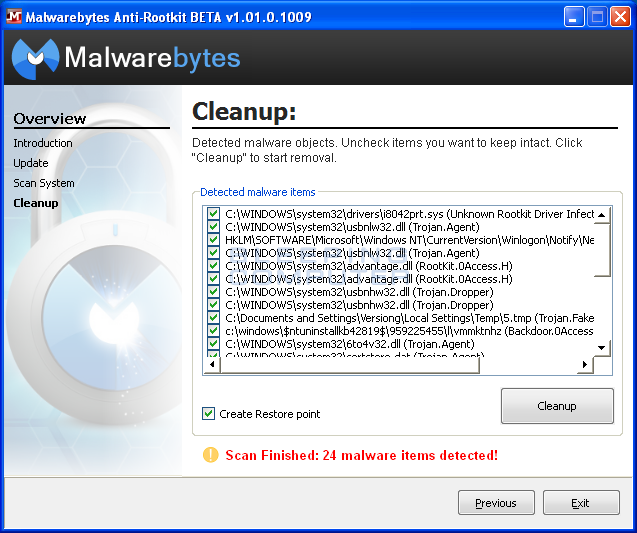
Scan for Malware

The same Trojans are known to drop fake malware files on the infected computer and make configurations to launch User AccountControl upon each system start. Basically using task-manager to get around it but its still there and it wont close as I said but using the task-manager staying open will allow you to do things to do a system restore. Processes launched using a standard user token may perform tasks using access rights granted to a standard user. By default, standard users and administrators access resources and run apps in the security context of standard users. Do you run it and if so why? This prompt ensures that no malicious software can be silently installed.
User Account Control Box Keeps Coming Up

In other words, limiting your own abilities also limits what malware can do. Instructions are provided below to guide you through the installation process. He apparently got rid of a file named roqni. Click on the blocked notification icon in your task tray near your clock and select Run blocked program and select Malwarebytes' Anti-Malware. This strategy creates a separate copy of the virtualized file for each user that runs the non-compliant app. As Windows Vista becomes widely deployed, we expect that attackers will adapt to its new environment.
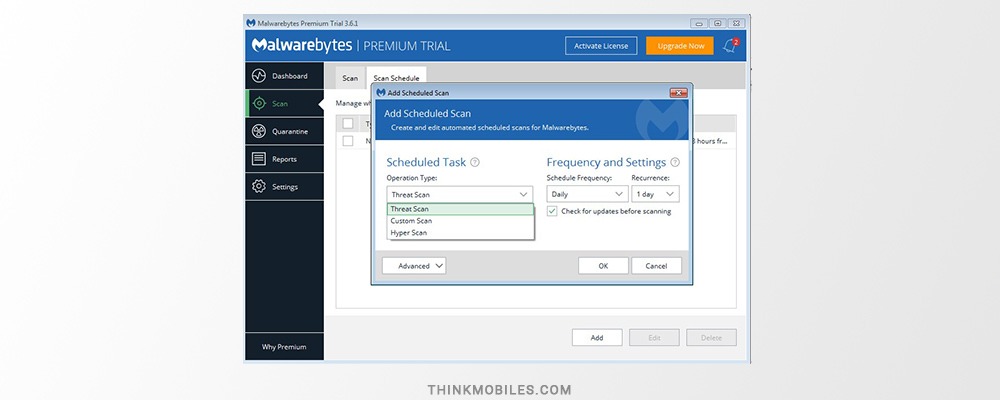
Download and install Malwarebytes for Windows

In Windows 10, User Account Control has. Normally it is the browser, but in this case, we are misled. Other apps, especially those that were not specifically designed with security settings in mind, often require additional permissions to run successfully. You can also right click on the Malwarebytes Anti Malware icon in the taskbar and make sure Start with Windows is checked. In order to post comments, please make sure JavaScript and Cookies are enabled, and reload the page. If Reimage fails to detect parasite, ask a question in comments and provide as much detail as possible or try scaning with.
User Account Control (Windows 10)
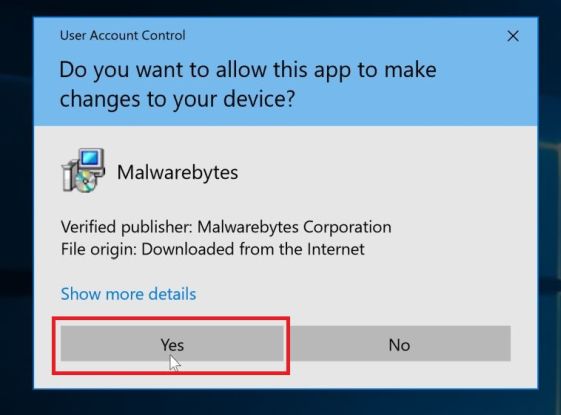
However, I have a question, this might be absolutely nothing but I need to know; when I click on the malwarebytes icon, the User Account Control prompt comes up asking if I want to allow the program to make changes to my computer, will this effect the programs ability to provide me with real time protection? General Discussion hey guys, everytime i try to open a application called steam this appears. Not sure on what type of virus it is for him? Such infections can be hard to trace as they hide under seemingly innocent executables that are in no way malicious. The file is then inspected to determine its requested execution level, which is stored in the application manifest for the file. Anyway, suppose this InfoStealer doesn't make changes to the system, as MrBrian suggests. The consent and credential prompts are displayed on the secure desktop by default in Windows 10. These types of apps are referred to as legacy apps. If you start to get random crashes, system hangs etc you can guarantee that this is the problem and you have 2 alternatives.
Remove User Account Control (Fake AV)
Click Classic View off to the top left 4. After that download Kaspersky 2015 Internet Security 30 day full anti-virus or I recommend the Internet Security software. Finally, I found one that did -- I had downloaded Firefox to test to discover what was going on. To deny access or stop any process is not irreversible a matter of minutes ; to get infected you might need the time to restore your system if you have an image 30 minutes , personal data theft is a one way road. Vista decides which processes applications or settings are subject to User Interface Privilege Isolation by using something called the Process Integrity Level.
User Account Control (Windows 10)
Anyway; I turned on my pc a couple hours ago to get any new emails. Or are my worries unfounded? Windows 10 also heuristically detects updates and programs that uninstall applications. Fusion The Fusion database stores information from application manifests that describe the applications. I want malwarebytes to have complete control to keep my computer safe, is there anything I need to do? Today's browsers offer site preferences where you can keep scripting disabled globally, yet enabled on your trusted sites. If an app you had in an exception list should get infected or spoofed by malware or a virus, it would be able to easily run elevated without you ever knowing. All Windows is saying is that Windows has notice that something is trying to get into Malwarebytes Anti Malware and asking for your permission to allow it.
User Account Control (Fake)

Because just right now, I've experienced 3-4 quick screen blackouts for the first time this evening. You can use security policies to configure how User Account Control works in your organization. File system and registry The per-user file and registry virtualization redirects per-computer registry and file write requests to equivalent per-user locations. Additionally, any apps that are started using Windows Explorer for example, by double-clicking a shortcut also run with the standard set of user permissions. I recall that a Malwarebytes pop-up box had come up, indicating that it had found a Trojan and had quarantined it. I have malwarebytes checked to start with windows and in my task manager it shows that malwarebytes is always an active process. Wouldn't those blackouts have stopped happening right then? The virtualized copy is maintained in the user's profile.
User Account Control Settings
I don't know what else to tell you. Now that you know about the awful goal of this fake program, you must not fall into its trick. The secure desktop dims the user desktop and displays an elevation prompt that must be responded to before continuing. In order to better understand how this process happens, let's look at the Windows logon process. When the user clicks Yes or No, the desktop switches back to the user desktop. When finished, you can delete the downloaded. Sometimes it takes some digging to get the information, but it's the only way to know for sure what is going on.