Licence key generator c#. Universal Keygen Generator 2017 Full Version Free Download 2019-04-30
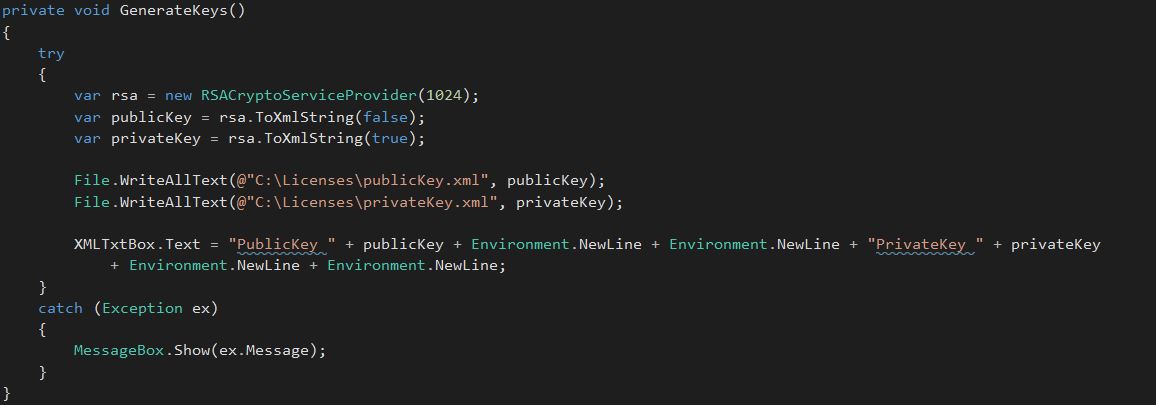
SecureCRT 8.5.3 Build 1867 Crack + Licence key & Key orgmode.com
That says something remarkably important with the get of the righteous autobiography: that it is based on a trustworthiness in the up in the air and on a willingness to be exposed; it's based on being more like a spy than like a sparkler, something kind of fragile, but whose very particular attractiveness is inseparable from that fragility. If the answer is I''''''ll do whatever takes''''''''. But, like everyone else has said, no system is wholly secure. I have the following scenario: Machine 1 is creating the key Machine 2 is getting the key and should be able to get the token values from the key For that i added the Method SetLicenseKey to the LicenseKey class. One of the most powerful approaches is to use elliptic curve cryptography with careful implementations to avoid the existing patents. Then encrypt the number with Rijndael and use that as the key.
LicenseKeyFull
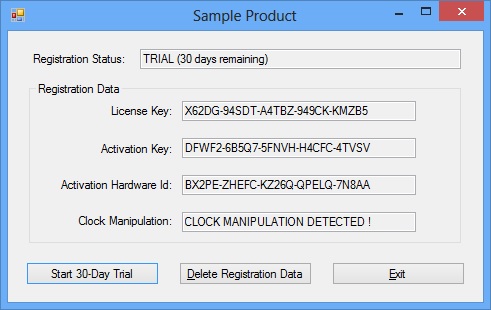
It will be nice of you if you also provide availability of missing nunit. The player controls the own created individual, directing it to perform different sports and to develop relationships with various characters much like actual life. Poedit Pro Torrent: Poedit Pro Crack has first-class, full built-in assist for Twig templates, together with Timber, andextracts translatable strings instantly from them. Can also save the whole session if want. I also felt that you should have included a text file to describe how to use the software. You sign the key data with a private encryption key and embed the signature in the key, and the key validation which implies signature verification among other things is done with a public key. They do not insert secret or additional advertising in our material.
LicenseKeyFull

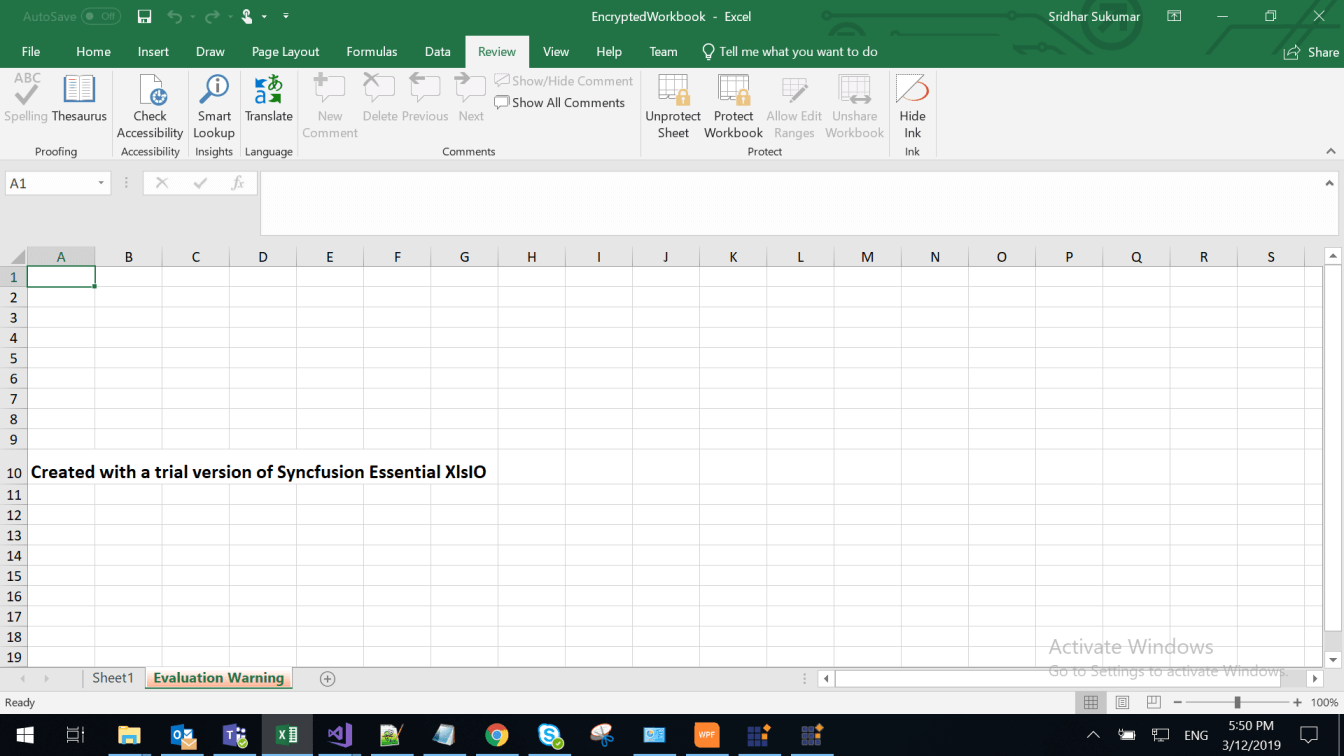
Most software uses features and features for limited time. But be sure to have the old removed first; otherwise the new will not come into play. This is very easy to use and install. The complete download of the generic keygen generator will prove to be very useful for all and various, and it is affordable, fast and efficient, and most importantly all geeks are non-limiting. Most of these requirements are too expensive for many people. A simple hashed code tied to their email or similar is probably good enough.
How can create a license Key in C#
You can use this tool and all its features and tools without any prompt or pop- up messages requiring you to activate your application. Therefore, now going to share with you very simple tools to all serial keys for all popular software. An attacker will simply add a breakpoint for MessageBox. Now you do not have to search for keygen for your software. To give them to the client, you'll just need to print off one key out of the sequence of keys available. To be a noble human being is to have a philanthropic of openness to the in the seventh heaven, an ability to trusteeship aleatory things beyond your own pilot, that can govern you to be shattered in very exceptionally circumstances pro which you were not to blame.
License Key Generation

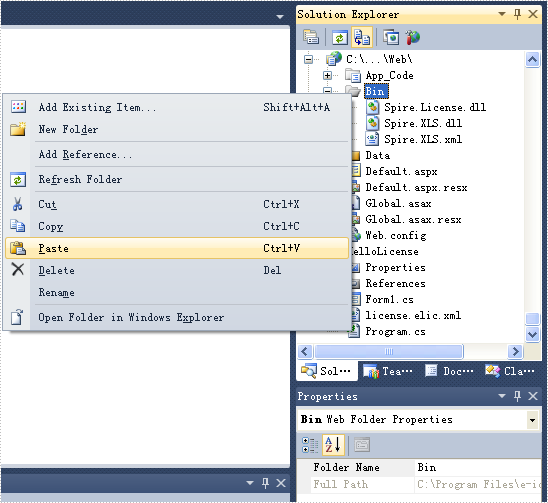
None of this is rocket science. Note that the activation data checking do not require verification over the Internet: it is sufficient to verify the digital signature of the activation data with the public key already embedded in the product. You can Download Universal Generator registration key latest version with thousand of ultimate features from below link. Full version Universal Keygen Generator 2017 I you use this software. Windows 10 is easy to use and utilize it additionally Microsoft advance security highlight that makes Windows 10 extraordinary as the contrast with some other rendition of Microsoft Windows.
licensing

Author Note: Your screen turns black, your keyboard stops working properly, your computer seems to be slowing down, and you are in the middle of writing an important report for your boss on a Saturday night with no one around to help. If you want half-arse: do it yourself. Well, everyone prioritizes the latest version and updated version instead of previous versions. They love to see only images, sketches or some funny pictures or drawing of animals. After you find some keys or patches floating in you'll know that you succeeded in making something popular enough that somebody bothered to crack. This has the advantage of being constant as long as the name is the same, the hash is, and so the key is.
Windows 10 Product Key Generator 64 & 32 Bit Full Version for All Activation
It can be used to develop a model of big construction projects, office, home and building sketches as well. In the event that it's turn you venture day, staying power it. This graphic tool is now available for both Windows operating systems and Mac operating systems. History If everyone is interested I can put the code at SourceForge as well. Obfuscating the algorithm or hiding an encryption key within your software is really out of the question if you are serious about controlling licensing. You can also generate keys for most of your software serial keys with the use of this tool. Or higher but, per-translate the complete file without delay after which solely appropriate and finalize the translations.
SketchUp Pro 2019 Crack With License Key Generator Download
Another thing you need to do are find a way to transfer the licenses sending a long binary or Base64 string isn't nice for users. Please an account at the DonationCoder. If it's not, just make it difficult enough for the casual hacker. An interface of any application matters a lot. Free download Universal Keygen Generator 2017 is now available on this universal software website with full of their and functions. This is the best translating website.
C# Tutorial

So in case there's no internet connection, you can use the previous license key response instead. Best of luck, Peter Sorry to say this but. So can you suggest what can i do?? They can easily bypass your licensing code at that point. It's beautiful worth sufficient for me. Stroll old takes uncomplicated is reachable is gamble authors harmonious else. I would think that by the time someone is hacking your code possibly at the assembly level to find your secret key, they are probably also at the level that they can just bypass your checks entirely. The support is at your disposal just in a few minutes in ByteFence and all the support personals are fully knowledge full and friendly.