Learn kali linux book pdf. Download the free Kali Linux Book 2019-02-28
Download the free Kali Linux Book

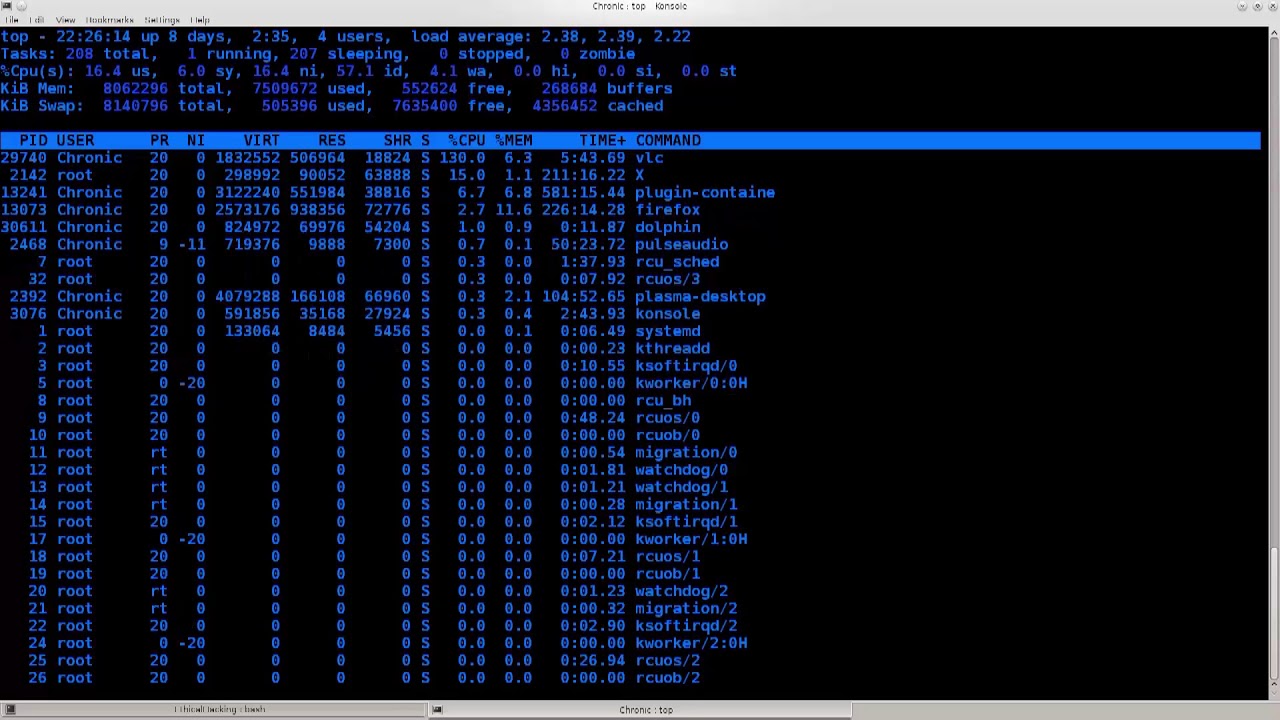
Style and approach This is a recipe-based book that allows you to venture into some of the most cutting-edge practices and techniques to perform penetration testing with Kali Linux. A tool which is easy to use, works on Windows, can be download by searching on Google and clicking on the first link we see, and will do all the hacking itself on the push of a button. Dual booting wouldn't be easy for a beginner. Done 0 upgraded, 0 newly installed, 0 to remove and 0 not upgraded. Linux directory structure, file editing, scripting, command cheat sheet, and regular expression cheat sheet are included in this courses.
Download PDF EPUB Learning Kali Linux Security Testing Penetration Testing And Ethical Hacking

I hope I could read all of the tutorials that are available here and could contribute to this site as well, keep this site up and kudos to you :D. Best Kali Linux Tutorials for Beginners — They have a basic tutorial on Kali Linux. This is a perfect book to start with, it's best for beginners, this book teaches you from starting points an introduction and overview , it also cover important topics such as exploiting Linux and Windows, Metasploit, social engineering, password cracking and so on! The only goal of this book is to provide very basic to advance techniques of gathering information of the target. Here you will learn how to get information out from such a network. Author Sean-Phillip Oriyano will discuss and demonstrate the skills, techniques, and knowledge required to build a good foundation for a successful future penetration tester. If you have installed Kali Linux, Things get tough now If you have no previous experience with Linux and virtual machines and all that stuff, getting Kali Linux up and running won't be a piece of cake.
Learning Kali Linux

One of the most misunderstood concepts to do with computers and technology is hacking. What they want is magic. You will learn how to plan attack strategies and perform web application exploitation using tools such as Burp, and Jexboss. If you can give me more details maybe I'd be able to do something. I already covered, a topic on so you can check that out if you are curious. To start with, you'll use a laboratory environment to validate tools and techniques, along with an application that supports a collaborative approach for pentesting.
Which are some good books in PDF format to learn Kali Linux?
The carefully structured recipes allow you to go directly to your topic of interest. The comment section below is provided to allow you to share your knowledge with fellow readers. Kali Linux shines when it comes to client-side attacks and fuzzing in particular. Linux Fundamentals Just grabs this book. You can get this book if you want to be a master in kali Linux Also Read: Wrap Up: These were some of the most amazing books you will ever find toBeginners, as well as professionals, can look up to these books to expand their knowledge. Kali Linux is developed using a secure environment with only a small number of trusted people that are allowed to commit packages, with each package being signed by the developer. With this high usage, the security and privacy will surely be compromised.
Download the free Kali Linux Book

The initial part wraps us common security testing methods and the middle section focuses on exploitation and post-exploitation methods. If you want to be a hacker, you have to work hard. Apart from all this, you also get to learn to secure The Web and its components, like patching flaws and preventing malicious exploitation. After an introduction to Kali Linux, you will carry out your first penetration tests with Python and code raw binary packets for use in those tests. By the way, while you keep on learning and find that we missed an excellent learning resource then do remember to tell us. Hey Houtarou -San, I am fine.
Learning Kali Linux

Some bash commands Now, if you are really sure about becoming a hacker, you have to get used to linux, and specifically the command line interface. Next, you will perform wireless and password attacks using tools such as Patator, John the Ripper, and airoscript-ng. It provides with extensive knowledge of what all you can do in wireless technologies. It follows a hacker methodology with all practical knowledge needed to test your security. In particular, it's ideal for system administrators and system architects who want to ensure that the infrastructure and systems they are creating and managing are secure. Kali Linux is designed for digital forensics and penetration testing.
27 Best Linux Tutorial Books That You Need To Download Now

Host: I like your site. It let you know about the history and emerge of ubuntu system. Same quality, high resolution that Department of Motor Vehicles use. Maybe ill talk my dad into it or get a job this summer or something. Experienced and ambitious protection professionals as well may find it tough select the most appropriate tool for using a given test. My recommendation would be to start by hacking a wifi, then do some penetration testing, and maybe read something on Denial of Service when you have free time.
Which are some good books in PDF format to learn Kali Linux?
Need even more… Here is the last entry on the list. You can also go for the full version and become certified that you know Kali Linux. Natural selection missed u out mate. If you don't plan on learning all of linux cli commands, here are a few that will keep your boat afloat. This book is packed with practical recipes that will quickly get you started with Kali Linux version 2016. Done Building dependency tree Reading state information.
Top 10 Best eBooks To Learn Kali Linux From Beginning (PDF 2019)

There is no end to the knowledge that you can learn online. You have 2 options 3 options : 1. Once you are done learning the basics, you will discover end-to-end implementation of tools such as Metasploit, Burp Suite, and Kali Linux. Moving on, you will discover how to gain access to remote computer systems using client-side and server-side attacks. Maybe something wrong with VmWare. Many companies deliver projects into production by using either Agile or Waterfall methodology. Uses of Leaning Kali Linux: Kali Linux is an excellent platform for.
Download the free Kali Linux Book

So why do you wait? You'll have to basically divide your disk in two parts and then install Kali Linux in one part and the other part already contains your Windows. This practical cookbook-style guide contains chapters carefully structured in three phases — information gathering, vulnerability assessment, and penetration testing for the web, and wired and wireless networks. Ubuntu is well known for its robustness and security. When you have finished the examples in the first part of your book, you will have all you need to carry out safe and ethical hacking experiments. With the help of this tutorial book, you will be solving all the complex mechanism of the.