Kmspico.exe trojan. How to remove KMSPico Trojan and decrypt files 2019-03-09
What are the disadvantages of using KMSPICO for activating Windows 8.1 instead of a real activation?

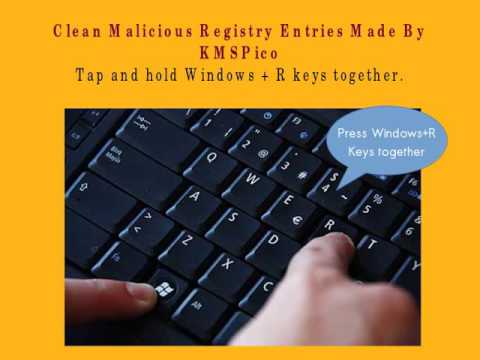
Make sure your programs are up to date - because older versions may contain Security Leaks. You can try removing those manually, but manual method may not help you out fully to remove all the threats as they can regenerate itself if a single program code remain inside. A deep system scan will help you see whether you have installed some malicious programs along with it or not. Press F8 key continuously until the Windows Advanced Options Menu launches. The Automatic Removal Tool offers you 2 way protection.
Remove KMSPico virus (Removal Guide)

In case you did not, then you will have the opportunity to pay for the license key. Now Reboot the computer and run the scanner to detect any threat or suspicious program remaining inside. The following video explains guide on how to delete browser hijacker infection, adware and other malware with MalwareBytes. You can't use an illegal license provided this tool if you uninstall it. Let me clear about this also. Several years ago, the malicious installer was used to spread Domino ransomware. .
orgmode.como
The complete removal means more than this. Delaying the start of this service is possible through the service manager. And What is the interesting part? I recommend you to bookmark this web page ast this is going to be a long post and We are sharing some tricks also so. This is a powerful In-Built Antivirus for Windows 10 Users. Removes all registry entries created by viruses. No matter, you should be okay if you follow the steps outlined below: delete all suspicious and unknown applications, get rid of malicious scheduled tasks, use free malicious software removal tools.
What is orgmode.com ? orgmode.com info
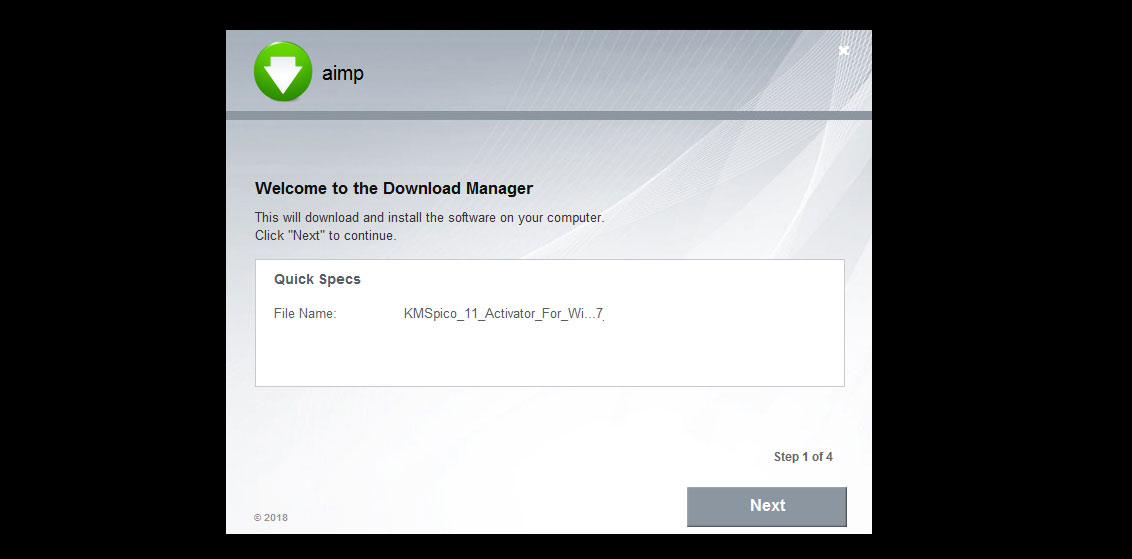
Necessary to look at the text which is written under Details. Examine the result when the scan will be finished. Cybercriminals take advantage of the fact that people are seeking to get useful computer software for free, so they infect most requested computer programs with harmful components, such as Trojans or worms, or less-harmful threats like adware. I tried installing and running a few anti-virus but it won't let me. If you have installed this illegal program, we strongly recommend you to check your computer with an anti-malware program. Upload files to TraDownload with single click: How to download kmspico exe files to my device? See more details in the video guidance below.
I installed KMSPico but it turned out to be malware
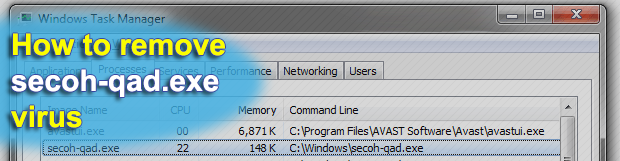
Just in single click, and everything done for you. Due to this, every time when you start your computer, it will launch itself automatically. For example, it collect your bank details, credit card info, login or password details, etc and perform illegal activities so as to fraudulent your money. It is a highly destructive program that seems like a genuine application for Windows computer. If you believe that your computer might be infected with any malicious programs infiltrated by this software, you must run a quick scan with. It offers you 24X7 tech-support for free so that whenever required you can take help of the computer experts.
Download KMSpico Activator : windows 10, 8.1, 7 and Office

Please post the log for my review. We need feedbacks from your side. Available only in Windows 7 and later versions. However, this is the only way to go back to the safe and error-free use of your computer. A scheduled task is added to Windows Task Scheduler in order to launch the program at various scheduled times the schedule varies depending on the version. First of all, you need to disable your Antivirus. No hidden charge or anything will be taken from you.
orgmode.com Removal: How to Get Rid of orgmode.com56934cf71c6be5e4067bc9e7dba4fa8
We have made this Activator only for you for the best solutions. Some of most common ways are discussed below. Also, please be attentive and do not get rid of essential system files by mistake. However, there are also special solutions, that can detect cryptoviral activity and stop it, preventing modification of your files. The main program executable is kmseldi. It adds a background controller service that is set to automatically run. Totally Free and User-Friendly: It is totally free and user-friendly.
What are the disadvantages of using KMSPICO for activating Windows 8.1 instead of a real activation?

Trouble-free tech support with over 10 years experience removing malware. Kaspersky Anti-Rootkit and malware checker says it's high risk and a fatal malware process. Illegal software might appear on your computer without your knowledge There are two ways how this hacking-tool may enter your system — you can directly download it from various shady websites which promote it, or the developers might distribute it together with a third-party application and help infiltrate your system without your permission. The tool promises to provide a genuine license and premium features without any money. The Trojan is still there.