Google hacking pdf. Google Hacking for Penetration Testers 2019-02-06
Google hacking (dorking) tutorial #1
According to Google, all of them! A Problem-Solving guy and helping hand for fellow bloggers and friends. Another tool called social engineering toolkit can be used to carry out a phishing attack on all the emails. The following table provides a brief rundown of some queries that can locate various default pages. Adapun kelebihannya terkait efektivitas, efesiensi dan ketepatan hasil. Since its heyday, the concepts explored in Google Hacking have been extended to other search engines, such as and. Somewhat like a plain google search. Pemahaman yang cukup serta penguasaan teknik pencarian yang baik pada mesin pencari merupakan bagian dari keterampilan dalam berteknologi informasi.
Google hacking (dorking) tutorial #1

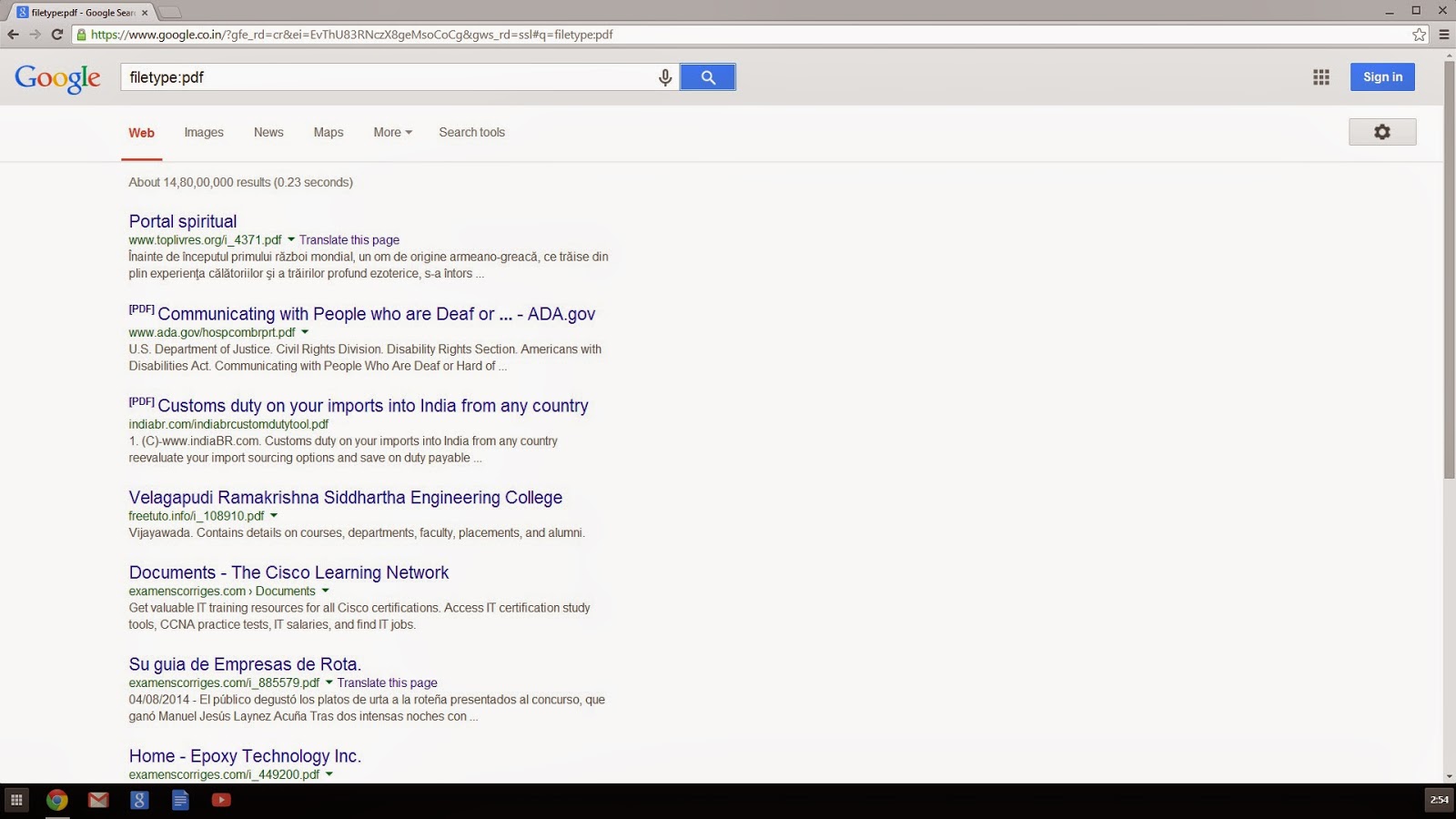
These Google hacking techniques were the focus of a book released by Johnny Long in 2005, called Google Hacking for Penetration Testers, Volume 1. Nigeria has begun to experience one of its difficult times when cybercrimes started to escalate day by day and causing loss of billions of dollars since then. Although it all started with google, the term google hacking now covers not only google search but any search engine in general. Note that actual exploitation of a found vulnerability crosses the ethical line, and is not considered mere web searching. The process can be a little time consuming, but the outcome will be worth it after learning on how to use dorks. Notice that the directory listing includes the name of the server software as well as the version. All you need is the right string to find them.
Google hacking (dorking) tutorial #1
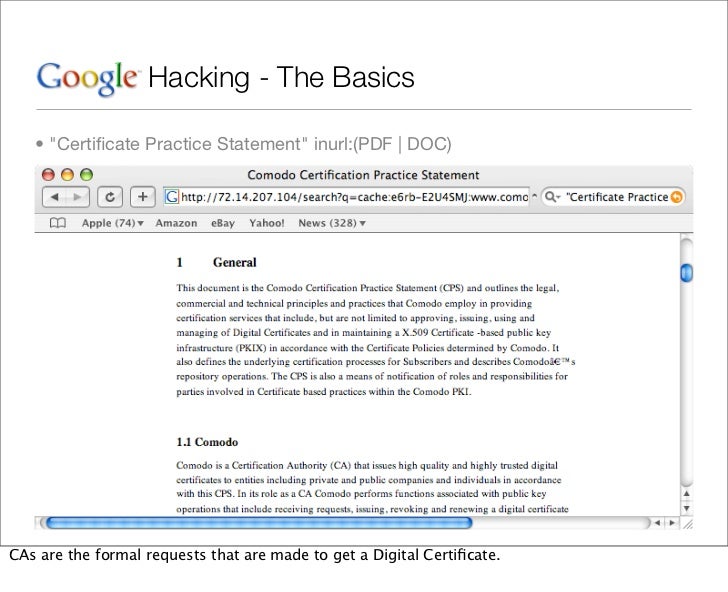
In the end it will look something like this. It has most powerful web crawlers in the world, it provides lots of smart search operators and options to filter out only needed information. All in all, Google Calendar is very useful addition to our day-to-day work. By providing a simple page to test, the administrator can simply connect to his own web server with a browser to validate that the web server was installed correctly. Check out my previous post on. But do you know tips, tricks and operators which can be used for google hacking? Google search terms used by hackers to discover such exploitable material through search engines are called google dorks.
(PDF) Google Hacking for Penetration Testers, Third Edition 3rd Edition
If yes then great or terrible things follow. Anyway now I am going to explain you how to use some for finding vulnerability in websites. But there is a Note of all the People who are Going to Download these E-Books that These are only Used for Educational Purpose. Some of the more popular examples are finding specific versions of vulnerable Web applications. Google hacking, also named Google dorking, is a computer hacking technique that uses Google Search and other Google applications to find security holes in the configuration and computer code that websites use. The operator can be used with or without the colon. Several alternate queries provide more accurate results: intitle:index.
60+ Best Hacking EBooks Download in PDF Free ( 2019 )

Google hacking involves using special search terms in the google search engine to narrow down the search results to something very specific. Now there is another search engine called shodan, that can be used to find devices more efficiently. Conlusion In the second part of our tutorial, we will show you more complicated formulas, how to find vulnerable online cameras, web servers and many many another practical tips and tricks. Hacking with the operators Now these operators are used to craft very powerful search terms that reveal lots free hackable stuff over the internet. There are some exceptions to this rule. How many pages on the Microsoft web server contain the word microsoft? This type of query can also be pointed at a particular web server: intitle:index. Completed the command might look something like this.
Google Hacking Database: Download HUGE List of 4500+ Google Dorks

We have decided to start a new tutorial where we are trying to collect all techniques and commands which can be used for google hacking. Finding Directory Listings Directory listings provide a list of files and directories in a browser window instead of the typical text-and graphics mix generally associated with web pages. When in doubt, search by last name only. These searches are often generated from various security advisory posts, and in many cases are product or version-specific. Automated attack tools use custom search dictionaries to find vulnerable systems and sensitive information disclosures in public systems that have been indexed by search engines. The list is growing, New Google Dorks are being find and added to the list.
Google Hacking Database: Download HUGE List of 4500+ Google Dorks
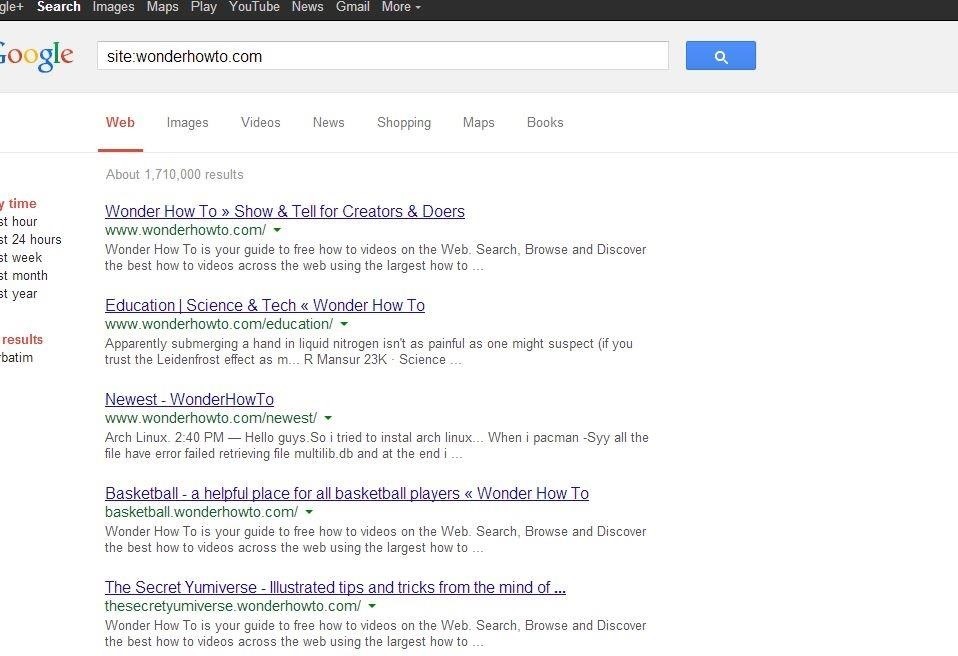
Consider the following query: site: microsoft This query searches for the word microsoft, restricting the search to the web site. This type of casual behavior on the part of an Internet user will lead an attacker to rightly assume that the web server is not well maintained, and by extension is insecure. One method involves using the information provided in a directory listing. Each line can be broken down and used in either an index. To keep yourself updated with latest Google Dorks, we recommend you to stay tuned with where new Google Dorks are being added with proper detail, examples and timestamp.
Google hacking (dorking) tutorial #1

Site Mapping To find every web page Google has crawled for a specific site, use the site: operator. An adept web administrator can fake this information, but often it's legitimate, allowing an attacker to determine what attacks may work against the server. If you want to find interesting books use this dork. Even credit card information is sometimes leaked through vulnerable applications. Somewhat like a plain google search. Vulnerabilities in website security can be discovered through Google hacking, techniques applied to the search engine by computer criminals, identity thieves, and even terrorists to uncover secure information.
Google Hacking Database: Download HUGE List of 4500+ Google Dorks
Conclusion Google hacking has been used extensively for both intrusions and information mining. Google can be used to even find websites vulnerable to sql injection. Furthermore, recommendations on how to identify these threats are enumerated as well as the countermeasures or approaches to mitigating them. But in 2012 Google held an open challenge for anyone to infiltrate their resisting servers. Operators Lets take a look at the special google search operators that are used to construct those high powered google hack search terms. Penulis mengangkat pembahasan seputar GoogleDork yang merupakan teknik lanjutan advanced yang dapat diterapkan pada mesin pencari yang paling terkenal Google Search dan paling banyak digunakan saat ini.