Ftp protocol example. An Overview of the File Transfer Protocol 2019-01-15
FTP (File Transfer Protocol) Command Examples
:max_bytes(150000):strip_icc()/curlcommand-57cf18075f9b5829f44e4ad5.png)
There is a lot of information contained in a packet as you can see. Server can use this information to return different document depending on the type of browsers. It offers you a limited, but very useful, set of commands with which you can navigate the remote file system and send and receive files. The rest of the file commands target only the remote filesystem: ln rm rmdir These commands replicate the basic behavior of the shell versions. However, they are required for public key authentication.
SFTP Command Line Examples
In this case localhost will refer to a different machine on each of the machines and the user will get many warnings about changed host keys. We have a team of individuals that understand the broad range of technologies being used in today's environments. In other words, the current request does not know what has been done in the previous requests. For example, the base specification doesn't even provide for clients to query a file's size or modification date. This is what we are looking for.
SFTP File Transfer Protocol. Get SFTP client & server
Because video is collection of frames. Our customers include small businesses using Internet technologies to corporations using very large mainframe systems. Then another connection is opened called the data connection. These sessions will try to reuse the master instance's network connection rather than initiating new ones, but will fall back to connecting normally if the control socket does not exist, or is not listening. This option is also passed to ssh. This link requires an Internet Connection. The default is the name given on the command line.
Linux sftp command help and examples

One reason you might be able to afford to lose them is because you can re-send them if they get lost. This value is used only when the target is down or really unreachable, not when it refuses the connection. The protocol does not mandate a particular port number or a direction that a data connection uses. After resetting the password to simple values I am able to login and also transfer the files. For the session to be initiated, the server and local client must be configured so that no keyboard input is required to log in; see above for more information. You can also specify a location for the file to be downloaded.
10 sFTP Command Examples to Transfer Files on Remote Servers in Linux

Because all sftp connections are encrypted, they require a username and password or public key authentication. Using this, you can check that you have enough space to complete the transfers you are interested in: df -h Size Used Avail root %Capacity 19. Since the protocol also does not provide a way to transfer an entire directory of items at once, the consequence is that there is no 100% accurate way to download an entire directory tree. This option applies to protocol version 2 only. You can use the mput option to transfer more than one file from local system to the remote system. If user is given, then they are copied to that account on the host. Options Here is a description of each of the options listed in the command syntaxes listed above.
FTP (File Transfer Protocol) Command Examples
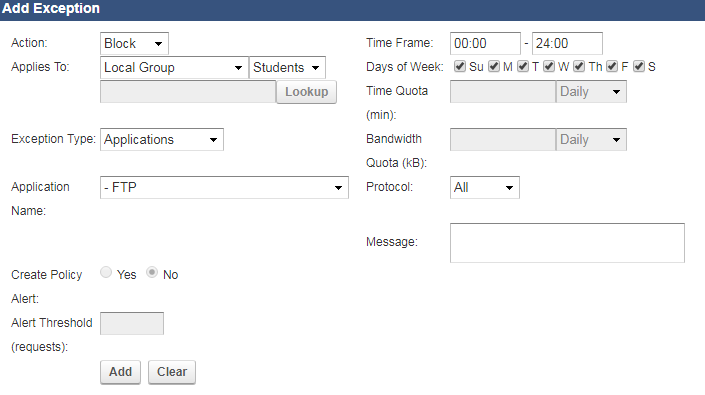
If the -s flag is specified the created link is a symbolic link, otherwise it is a. If no user is supplied, then the same user name as on the client side is assumed. You can use to create an empty file. The standard way to do this, and the most secure, is to use public key authentication. That is, a client can make several requests without waiting for each response, so as to use the network more efficiently. The protocol does not have any advanced support for character sets for pathnames nor file contents. The default sort order is.
SFTP File Transfer Protocol. Get SFTP client & server

A lot of people do this so that they automatically have local copies of their e-mail. The directive LanguagePriority can be used to specify the language preference in case of a tie during content negotiation or if the client does not express a preference. The default is 0, indicating that these messages will not be sent to the server, or 300 if the BatchMode option is set. Control Connection -- the conversation channel The protocol can be thought of as interactive, because clients and servers actually have a conversation where they authenticate themselves and negotiate file transfers. This ensures that shared connections are uniquely identified. If no path is given, the files are copied to the user's home directory.
10 sFTP Command Examples to Transfer Files on Remote Servers in Linux

This numbering scheme supports up to 4G addresses on the network. This option is directly passed to ssh. However, this means that connections will die if the route is down temporarily, and some people find it annoying. Once you have connected to the remote host, to run the commands on local machine you need to exit from the ftp connection. It was never widely accepted on the , and is now assigned Historic status by the. This is problematic for both and firewalls, which do not allow connections from the Internet towards internal hosts.
What is the difference between HTTP and FTP?

Drop into a local shell. The server now connects out from its port 20 on 172. This header will be described in later chapter on authentication. SimoTime Technologies makes no warranty or representations about the suitability of the software, documentation or learning material for any purpose. This is much more secure and can save you time in the long run.
SFTP (SSH File Transfer Protocol) :: WinSCP

For example: LanguagePriority en da nl et fr de el it ja kr no pl pt pt-br Character Set Negotiation A client can use the request header Accept-Charset to negotiate with the server for the character set it prefers. The default value is the following really long string: aes128-ctr,aes192-ctr,aes256-ctr,arcfour256,arcfour128,aes128-cbc,3des-cbc,blowfish-cbc,cast128-cbc,aes192-cbc,aes256-cbc,arcfour Compression Specifies whether to use compression. UserKnownHostsFile Specifies one or more files to use for the user host key database, separated by whitespace. For example, the following will be displayed. A path is useful for using sftp over protocol version 1, or when the remote sshd does not have an sftp subsystem configured.