Free security for my computer. 15 Great, Free Security Programs 2019-02-18
Free Computer Protection

We, along with our suppliers and partners, retain ownership of our respective Software and Services and all rights related to the Software and Services, including all intellectual property rights. This Agreement constitutes the entire agreement between you and us and governs your use of the Software and Services acquired hereunder. So what are you waiting for? Scheduled scan provides three alert options to the user: Scan Now, Cancel, Remind me later. For the purpose of this Agreement, use of the Software means to access, install, download, copy or otherwise benefit from using the Software. Comodo Internet Security offers complete protection. If you acquired the Software or Services in the European Union, Iceland, Norway, or Switzerland, then national law of the country where you downloaded the Software applies.
Why Internet Security?

In this mode, only the minimum required programs and services are loaded. The Software and Services are licensed to you, not sold, and they are protected by U. Right to Resort to Provisional Remedies Preserved by McAfee. If it is stolen, all the information it protects is at risk. This means untrusted but harmless applications have the freedom to operate as usual while malicious programs are prevented from accessing or infecting your computer. The subscription price for your auto-renewal is subject to change. It scans for threats such as malware, Trojans, and unwanted programs actively running on your computer.
Free Virus Scan, Free Virus Protection, Antivirus Software

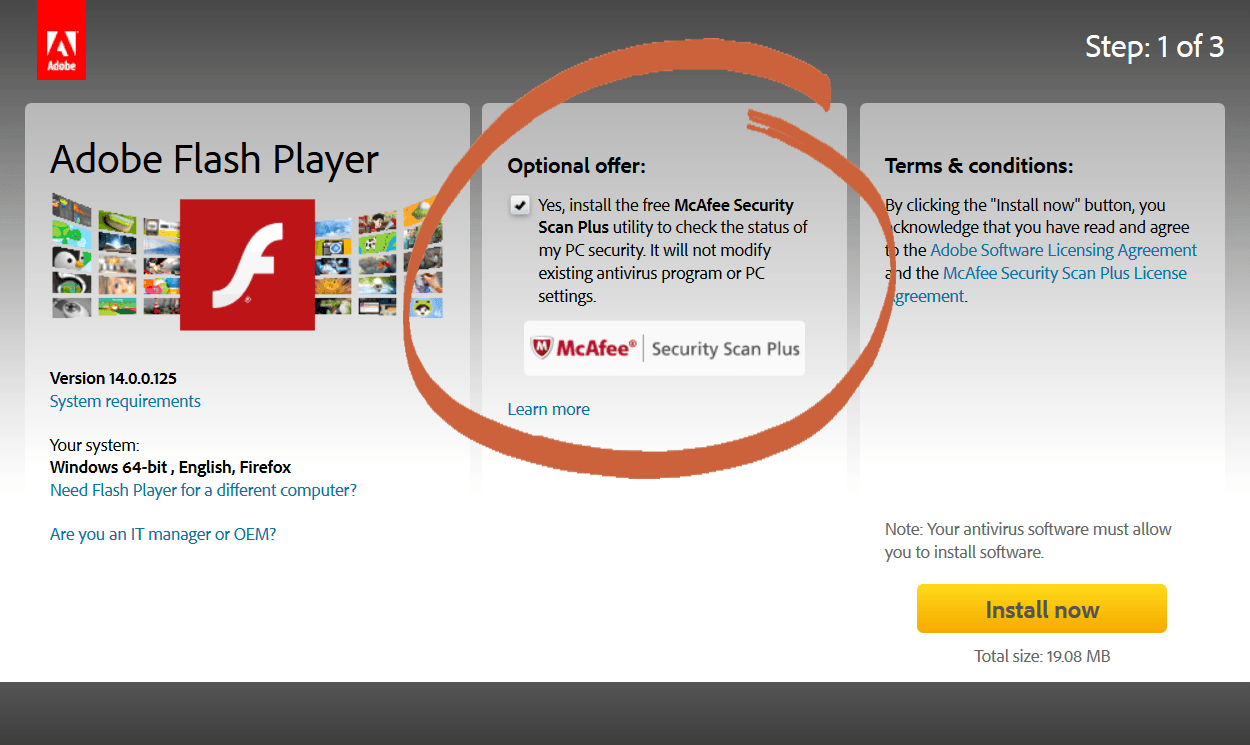
This protection goes well beyond traditional Antivirus software by ensuring any brand new viruses are completely isolated and cannot cause damage. We are not a credit repair organization, or similarly regulated organization under other applicable laws, and do not provide credit repair advice. We do not control or assume responsibility for the content of the third-party sites, and some of the third-party sites may have content that you find objectionable, inappropriate, or offensive. Doing this may speed up the virus scanning, free up disk space, and even get rid of some malware. The Fair Consumer Reporting Act provides that you may dispute inaccurate or incomplete information in your consumer report. It also scans browser history and cookies Security Recommendations if my computer is at risk Alerts direct customer to McAfee offerings if antivirus software, firewall protection or web security is out-of-date or not found. The Software and Services are not fault-tolerant and are not designed or intended for high-risk activities such as use in hazardous environments requiring failsafe performance, including nuclear-facilities operations, air traffic communication systems, weapons systems, direct life-support machines, or any other application in which the failure of the Software or Services could lead directly to death, personal injury, or severe physical or property damage.
Why Internet Security?

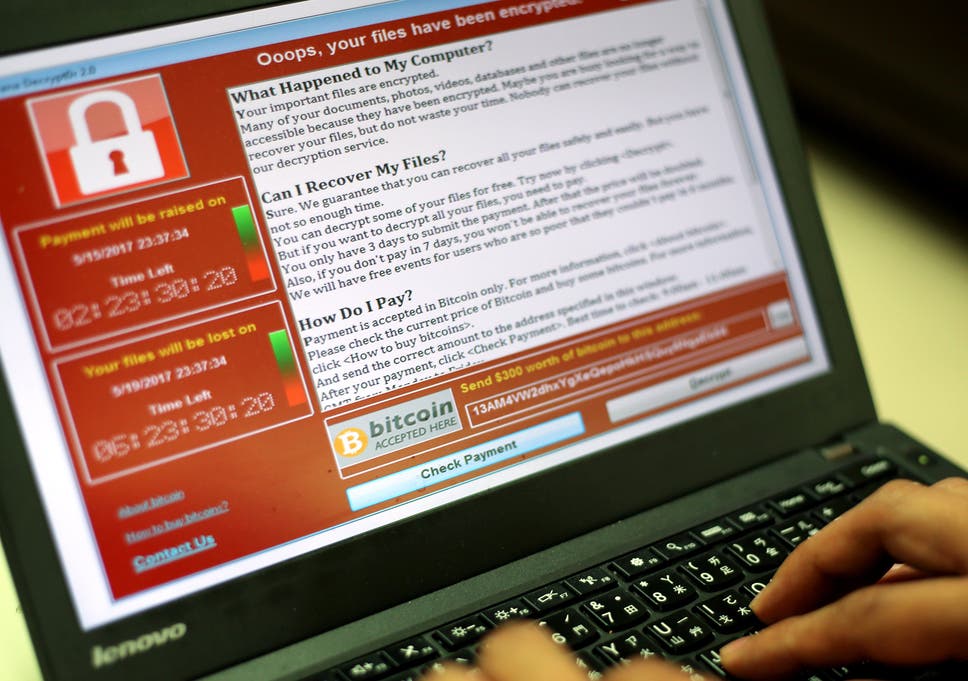
If this Agreement expires or is terminated, i you will no longer be authorized to use or access the Software and Services, including any online storage or backup services, ii you must permanently erase the Software and Services from your devices, and iii we may cancel or close your account. Detect threats in running processes and other temporary files Detects malware, trojans, and potentially unwanted programs in running processes and modules loaded by these processes. If you do not register your initial licenses to your account, or you do not use the email associated with the account during checkout, you will receive no pro-rata pricing and the subscription term of such additional licenses will be the term that you purchased. Multi-vector protection against viruses and malware offering full protection against all of today's sophisticated malware threats including Trojans, keyloggers, phishing, spyware, back-doors, rootkits, zero-day and advanced persistent threats. If you are an adult, parent, or legal guardian, you may use the Software or Services to track and monitor only your own children, children for whom you are the legal guardian, or others for whom you have legal authorization to track and monitor.
Free Virus Scan, Free Virus Protection, Antivirus Software
It offers predefined audit reports to help track activity happening in databases, web servers, Windows devices, network perimeter devices, and more. If McAfee receives notice that a user is or becomes identified as a sanctioned or restricted party under applicable law, McAfee will not be obligated to perform any of its obligations under this Agreement if such performance would result in violation of the sanctions or restrictions. All-in-one award winning antivirus solution ready to protect every part of your business. A dynamic release cycle constantly adds features for timely challenges like Ransomware. For consumers in Australia: The benefits to you under the limited warranties are in addition to other rights and remedies you may have under a law in relation to the goods or services to which the warranty relates.
Best Computer Security Software
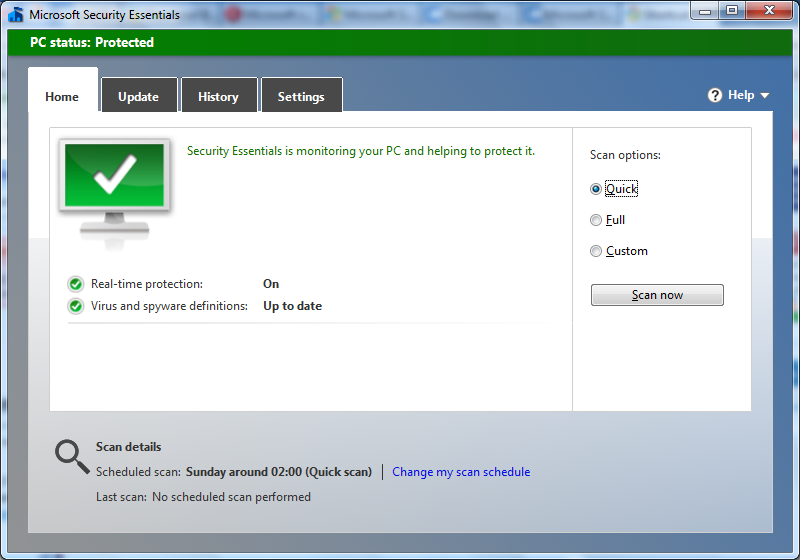
If you reject the updated Agreement, your license to the Free Software or Courtesy Services is terminated and you must cease all access to and use of the Courtesy Services or Free Software and uninstall the Free Software. The arbitration award will determine the rights and obligations between the named parties only, and only in respect to the claims in arbitration, and will not have any bearing on the rights and obligations of any other dispute. For your convenience and to ensure that the Software on your devices includes new features that we develop, by agreeing to this Agreement you give us permission to install Updates, and, at your request or with your consent, new Software on your devices automatically when available, to the extent that it is possible for us to run such background installations. You agree that you are a legal license holder of the Software on your device and your use of the Internet is solely at your own risk. It can be used either with cloud console or without. Another option is an on-demand scanner, which searches for malware infections when you open the program manually and run a scan.
Avast
The United Nations Convention on Contracts for the International Sale of Goods and the Uniform Computer Information Transactions Act do not apply to the Software or Services Attacks on Data. Though it offers a custom-scan option, Malwarebytes recommends that you perform the threat scan first, as that scan usually finds all of the infections anyway. Consult the documents that accompanied your purchase or terms of service, as applicable, for information regarding technical support and additional options. Is it the firewall, the behavior blocker, the sandbox or the antivirus which is stopping it? With Comodo Free Internet Security Suite 2019, you can prevent most of the cyber attacks and malware which can steal your private data stored on your computer, give hackers unauthorized access to your computer, financial and personal information. Used by Government, Military, Education, Telecommunications, Banking, Finance, and E-Commerce sectors, including many Fortune 500 companies. In addition, you can customize how often you want your computer scanned.
Free Virus Scan, Free Virus Protection, Antivirus Software
EventLog Analyzer is a comprehensive log management solution withreal-time threat detection and analysis. While Malwarebytes is scanning, you can see how many files or objects the software has already scanned, and how many of those files it has identified either as being malware or as being infected by malware. Additional Information about restricted parties can be found at the following websites: and. Built from the ground upwards with your security in mind, Internet Security offers 360° protection by combining powerful Antivirus protection, an enterprise class packet filtering , advanced host intrusion prevention and automatic sandboxing of unknown files. It is highly likely to do the opposite. Free Software and Courtesy Services.
Security Software
Please note your automatic renewal may fail to process if you used a payment device other than a credit or debit card to purchase your subscription. In the event of a conflict between the Arbitration Rules and this arbitration agreement, this arbitration agreement will govern. McAfee WebAdvisor is Software with a corresponding website that provides users with information to guide users about certain risks that may be associated with a website. Yes, out-of-the-ordinary behavior is sometimes the result of hardware conflicts, but your first action should be to rule out the possibility of infection by a virus, spyware, or other nefarious entity— even if you have an antivirus program installed. If you purchase additional licenses of the Software which you registered to your account in the future and you use the email address identified in your account profile for the new purchases, the initial term of the additional licenses will be automatically reduced so that the renewal date is the same as the renewal date of the Software licenses you initially purchased. The Fair Credit Reporting Act allows you to obtain from each consumer reporting agency a disclosure of all the information in your consumer file at the time of the request.
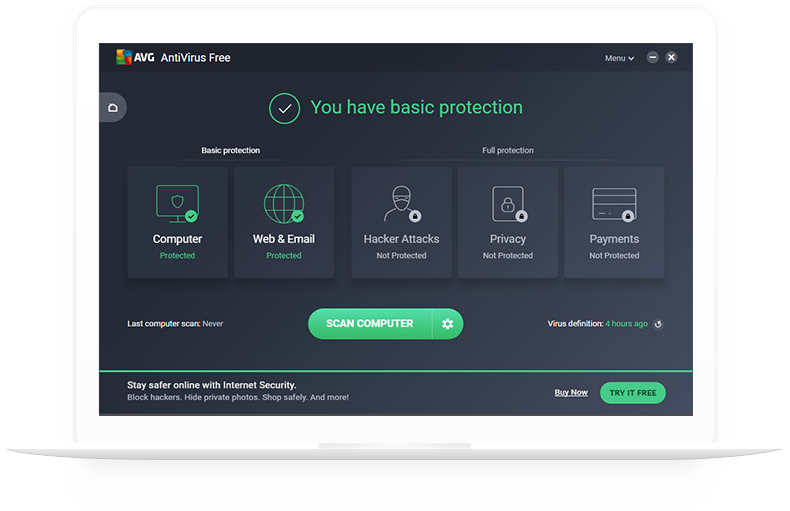
Can you protect your computer for free?

For accounts that support it, two-factor authentication requires both your password and an additional piece of information to log in to your account. . Customize scanning frequency You can customize scan frequency. While we will use commercially reasonable efforts to remove the attacking malware or virus, it is your sole and exclusive responsibility to back-up all data and files on your device so that they can be restored in the event of an attack on your data. Veriato RansomSafe acts as a vital layer in your ransomware defense, combining just-in-time data protection with multiple mechanisms to detect, and shut down attacks before they hold your business hostage.