Free anti spyware. Download AVG Anti 2019-03-05
Spyware Removal Programs & Cleaners. Top 10 Best Spyware Removal

The term actually covers a wide variety of sinister software, programs that can do everything from capturing your passwords as you type to literally spying on you through a webcam or internet-aware device. Still, as a secondary layer of defense, the free version of Malwarebytes is a must. It looks like a game, or a utility, or useful program of some kind, and may even perform its promised function. Spyware can change your computer settings, and in almost every case slow down your computer. Easy to use, fast and unobtrusive.
AVG 2019

Cons None, really, but note there is no such thing as a flawless protection product. How Antivirus Providers are Ranked To help you find the perfect antivirus software, you have the option to sort and filter the antivirus providers we have showcased. As noted, a first-class utility should wipe out keyloggers, along with all other types of malware. To be safe, either you should Internet Explorer, but an or you should apply the. Also: interesting alternative commercial operating systems.
Free Antivirus Download for PC

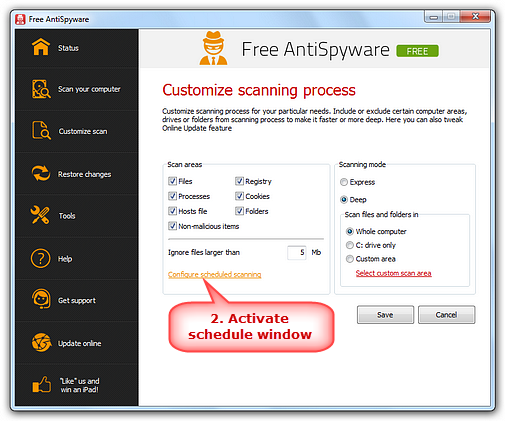
It's not so cool when it turns out that. The product is available as for personal use with limited functions, such as no automatic update and scheduling and limited repairing functions. Spyware is nasty business, threatening your security by collecting information about your online activity without your knowledge or consent. The program also has a selection of repairs that can be run to undo damage done by malware, and a scan log keeps a history of all the threats that have been deleted. Ransomware encrypts your files and demands an untraceable payment to restore them.
Products

The company gets out in front of potential malware attacks by initiating scans before an unknown file opens and preventing it from doing so should it throw up any red flags. Intuitive and versatile, including Website Generator, spellchecker, thesaurus, attachments, search engine, recycle bin, and much more! It's not about the best general-purpose security software. Discussion forum on security and privacy-related matters. Among the many antivirus apps and security suites we've reviewed, these top choices offer the best spyware protection. It is software that has been specifically designed to corrupt or damage a computer. It is generally distributed through malicious advertisements on less-than-reputable sites such as bit torrent or free video streaming sites. Spyware, as the name suggests, secretly spies on your every move.
The 11 Best Free Spyware Removal Tools (May 2019)
I used Iobit Uninstaller on it and there was one. When this sort of protection is active, the keylogger typically receives random characters, or nothing at all, in place of your typing, and attempts at screen capture come up blank. And some move your browsing to a secure desktop, entirely separate from the normal desktop. It's recommended that you have a free anti-spyware program installed on your computer at all times. Identifies all processes which are 'hooked' into the operating system kernel 'kernel hooks'. These products handle all kinds of malware, including threats much tougher than mere spyware.
Products
This Website is designed to facilitate discussion on computer security related topics, create computer security awareness, and to provide a comprehensive database of computer security knowledge and resources to the public. So, now that you've brought it inside your city walls, what can the Trojan horse do? That's something that happens in the movies. Radio buttons let users select a Quick Scan, Complete Scan, Critical Point Scan, or Custom Scan. We receive advertising revenue from some of the antivirus companies listed and this impacts how we sort by top affiliated antivirus. The possibilities are vast, but I'll focus on the ones designed to steal your personal data.
Spyware Removal Programs & Cleaners. Top 10 Best Spyware Removal

They need to be sued out of existance, but that won't be necessary since any company this desperate can't be long for this world anyway. We call them keyloggers, but in truth these nasty programs log a ton of information in addition to keystrokes. We do not include every plan the antivirus offers. Anti-exploit helps protect against any known vulnerabilities discovered in your system or apps, while malicious website protection keeps you away from fake or malicious sites. Authorized programs, like your video conferencing tool, get access without a problem. The perp can use these various threads of information to, for example, match up a username and password you typed with the website you were visiting at the time. What appears to be a favorite website could in fact be an imposter, foisting its own malware on unsuspecting visitors.
Free Spyware Removal Programs & Cleaners. Top 10 Best Spyware Removal

Cons None that I know of. But it also contains malicious code. This malware runs in the background, monitoring your activities and collecting information such as your passwords, banking credentials, or credit card details — which are then used by internet fraudsters to commit cybercrime. The way it works is that you can enable protection for your web browsers to protect against malicious scripts, exploits, and cookies that track your web behavior. For Android: Arabic, Chinese simplified , Chinese traditional , Czech, Danish, Dutch, English, Finnish, French, German, Greek, Hebrew, Hindi, Hungarian, Indonesian, Italian, Japanese, Korean, Malay, Norwegian, Polish, Portuguese Brazil , Portuguese Portugal , Russian, Serbian, Slovak, Spanish, Swedish, Thai, Turkish, Ukrainian, and Vietnamese. This virus scanner does not run in the background, it only performs its duty when you tell it to do so - which is a thing we like. Light on system resources and won't slow down your computer.
Download SUPERAntiSpyware Professional & Free Editions

The injected ads are worked into your browser and sometimes other software on your computer in a very contriving and natural manner, to seem as if there were no shady ongoings whatsoever. This is why a good Adware Cleaner is so important. Read on to learn about the varieties of spyware, and the technology that shuts down the spies. Malwarebytes also has which offers much of the same web-protections as the premium client. If your virus scanner is set up and working properly it should intercept the downloading of these files.
SuperAntiSpyware Free Edition
:max_bytes(150000):strip_icc()/shutterstock_562982815_remove-spyware-59dbc4130d327a0011d9132b.png)
Papers, research and other resources related to computer security. Prevent potentially harmful software from installing or re-installing. Features Personal Editions Business Editions Feature excl. There are varieties of malware that can turn on the webcam and watch you without causing the light to reveal their activities. Articles related to: online crime investigations, the latest threats, security updates, data breaches and cyber justice. Securing these devices requires network hardware like the or any of the many competitors that are springing up. Lowest Price is in price order and is based on the plan we link too.