Folder lock.torrent. Folder Lock 7.7.9 Crack Full Serial Keygen For Mac & Win [2019] 2019-03-30
Folder Lock 7.7.9 Crack With Key Free Download Full Version

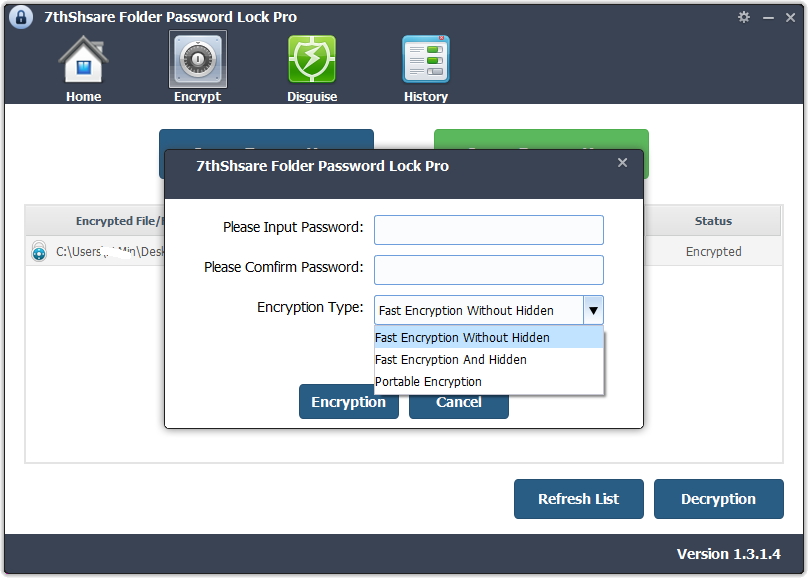
The Protected files are hidden, cannot be deleted and are also inaccessible and highly secure. It does all and more than I need. However, You can use it to encrypt your personal and important data. Lock folder has a very simple, elegant, compact, as well as easy to use. Once the files and folders are encrypted they also get secure from malware, Trojans. One-line summary: 10 characters minimum Count: 0 of 55 characters 3. The best part is that you can usually open the tool directly without even installing it your workstation.
Folder Lock

When you lock a folder, these are un-deletable. You can access your data even without the application. You can easily protect your files using wallets. The program allows you to create a backup to online storage. Additionally, Advanced Folder Encryption also allows you to shred files and even permanently delete any junk files from your computer that cannot be recovered.
Folder Lock 7.7.9 Crack Full Free Serial Key 2019 Here [Activated]
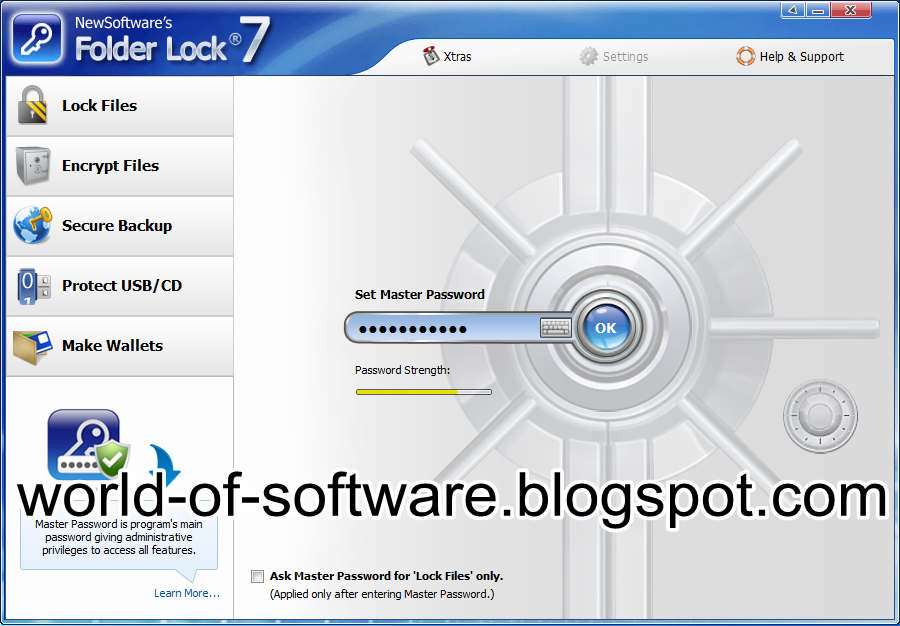
Furthermore, you can get access to the hidden files only if you enter the correct password. Moreover, it also allows you to defrag and ScanDisk effortlessly, however, remember to unlock all folders and backup your locked folders before you carry out the action. You can recover the locker from online backup. Also, the protected files are hidden, inaccessible and protected from deletion. In addition, this encryption, the encrypted files are hidden from the folders. Therefore you will have the ability of protecting folders, files and drives and portable devices with Folder Lock Portable.
Folder Lock

Not only that you can protect data with the application with the password but you can also so do by permanently deleting data. You can hide a unlimited number of files with Free Hide Folder which is completely free of any viruses, ads, or spywares. The application gives your ability to lock files in a secure locker. Hence, you will only have to remember only one password to access all this data and information. You can access your data even without the application. This will help you to lock folder automatically. You can also backup your secure lockers online with Folder Lock Torrent.
Folder Lock 7.7.9 Crack With Key Free Download Full Version
Additionally, Folder Lock comes with additional security settings unheard before. This step does not allow any outsider to have access to the files except the owner. You can simply put all your secret files into the folder and install the Folder Lock software and lock your folder. But Folder Lock 7 edition gives you access to make a backup of all data and save it in your hand. It prevents your data to be accessed by even the smartest of hackers and the spies with the hotkey-activated secret mode.
Folder Lock 7.7.9 Crack With Serial Key Free Download Here!

But this may likewise be put to use like a means of keeping predators. Someone who needs all of the security types in a one packet Folder Lock 7. Cons One license, one machine - I wonder if some day the encrypted folder can be cloned to my cloud account for even deeper backups? With this function, the user can automatically update the backup of the system and restore it to the last backup in case of system failure. This file will be no longer to appear and there is no chance to get these files without using Folder Lock Serial Key since your important data is invisible. This is a fast and efficient file protection software that attracts viewers from all aspect. It offers portability, locking files, encryption, hack attempt alert, shredding, history cleaning and much more.
Folder Lock 7.7.9 Crack Plus Serial Keygen Free Get [Fully]

With this, no one can track your browsing or other activities. They contacted me very quickly and help me to transfer lincence to new machine. So with this application, you can save your data in an easy way. This is a fast and efficient file protection software that attracts viewers from all aspect. In stays on your computer and no one can find if you have installed Folder Lock key on your computer. One you lock out something with folder lock, then it will be hidden from its old location. This is a fast and efficient file protection software that attracts viewers from all aspect.
[Download +Portable] Folder Lock 7.7.9 (Crack)! + Keygen For {PC & Android} 2019

What we do not understand is that this lets others get access to your privacy which can be either accidentally deleted by friends or family, or even manipulated by someone else. With which all user data can be protected in a few seconds. Hence, it is the user-friendly interface. It keeps your files private. Pros: 10 characters minimum Count: 0 of 1,000 characters 4.