Flash vulnerability scanner. CySA+ Chapter 6: Vulnerability Scanning Flashcards 2019-02-24
HP unveils Flash vulnerability scanner

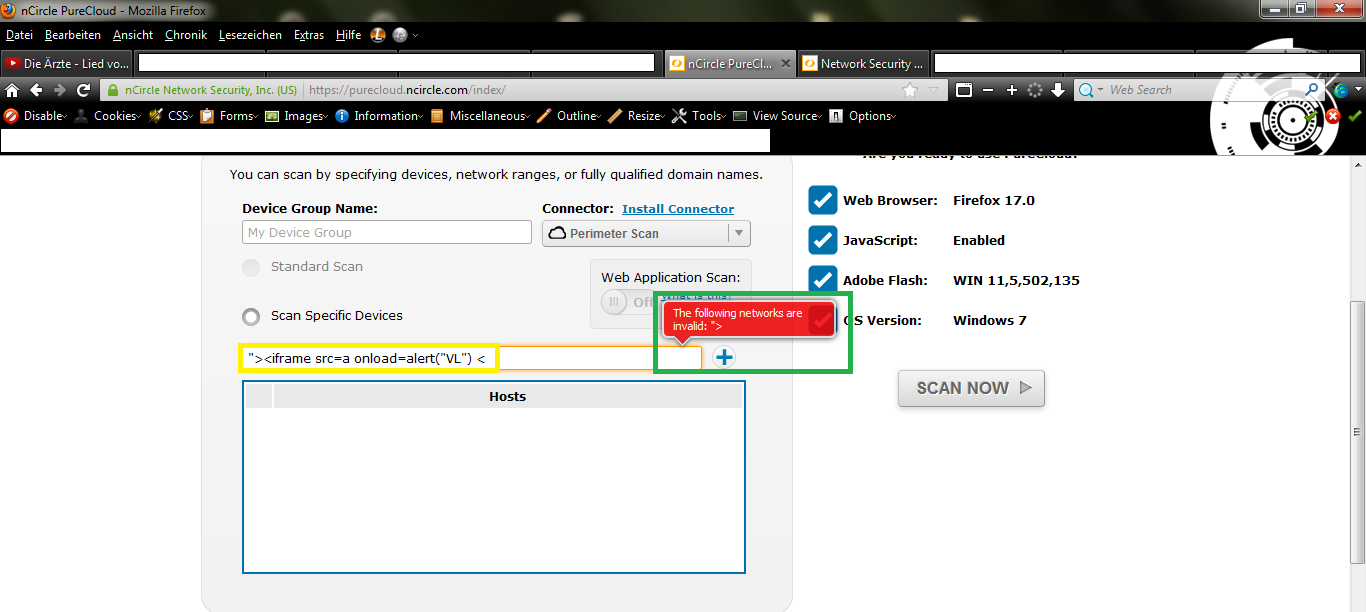
There is no way for the authors of a vulnerability test to know the details of your network, so they must create rules that are sometimes less granular, which may lead to false positives. Installing Nessus To install Nessus we must run the following command: apt-get install nessus Afterwards we need to add an administrator that will be in charge of the Nessus configuration. Dejan Lukan is a security researcher for InfoSec Institute and penetration tester from Slovenia. To learn how to update your flash player, go. When I goto the control panel:Programs and Features is shows the version on both installs as v 11. Promising increased scalability and speed across networks of various sizes, these companies provide several related services based on subscription tier.
CySA+ Chapter 6: Vulnerability Scanning Flashcards
We can specify the type of database being used, its username and password, how the report should be generated, what user agent the requests should impersonate, the client certificate to use against the target website and much more. System admins can be overwhelmed by the sheer volume of results. Remediation of network vulnerabilities should be done as quickly as possible after discovery, but not so haphazardly as to make the situation worse. When reviewing the report, you should also review event logs and network data. You should be able to see changes in the network based on the patches or changes you've made because of compensating controls.
A Guide to Installing & Using the Nessus Vulnerability Scanner
We can also export the report in various formats to be viewed by other people. Using Nessus After Nessus has been started, we can choose between two ways to connect to the Nessus server. We access the Nessus web interface by connecting to an address in a web browser. Trending improves context and allows your security response team to tailor its threat mitigation strategies to its efforts more efficiently. When the scan is started, it will be added to a list of all scans already done or currently pending still in the Scans tab. This content creates an opportunity for a sponsor to provide insight and commentary from their point-of-view directly to the Threatpost audience.
A Guide to Installing & Using the Nessus Vulnerability Scanner

For instance, you may want him to be able to scan his own host only. This enables the Nessus scanner to perform the scans more accurately and quickly. Nessus Users This tab is where all users applicable to login to the Nessus web interface are kept. Alternatively we can choose between two already defined options: default and all. Including key stakeholders in the discussion, or at the very least making them aware of your methodology, will ensure buy-in for future policy changes. Nessus Reports When the scan is finished, it will be added to the Reports tab where we can view the results of the scan.
A Guide to Installing & Using the Nessus Vulnerability Scanner
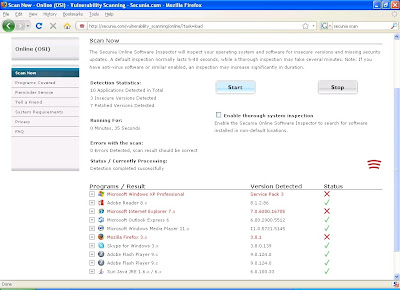
Nessus does have some basic port scanning; however, it's real power comes from its multitude of features for vulnerability identification, misconfiguration detection, default password usage, and compliance determination. Highly efficient business and industrial processes such as just-in-time manufacturing have allowed businesses to reduce process time and increase overall efficiency. Web browser technology can accommodate additional functionality through third party plugins and extensions. Nikto is a web server vulnerability scanner. This can be seen here: nessus-update-plugins Fetching the newest updates from nessus. The plug-ins tab, you can see all of the plug-ins available for scanning.
Adobe Flash zero
You may encounter challenges in remediation. He is very interested in finding new bugs in real world software products with source code analysis, fuzzing and reverse engineering. The simplest mechanism for verifying remediation is to compare consecutive vulnerability scans to determine that vulnerabilities were addressed via software patch or upgrade. The Add Policy tabs are listed below. It is possible the scanner is picking up these files. This iframe contains the logic required to handle Ajax powered Gravity Forms. You can compare running services, listening ports, open connects against a list of authorized services to identify any abnormal behavior.
Adobe Flash zero
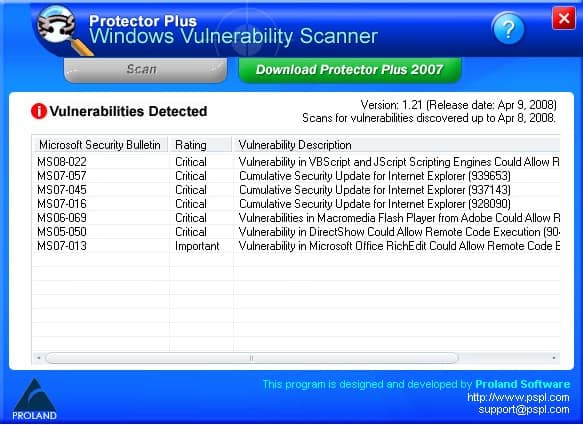
Note that the output includes the type of vulnerabilities, a short description, and any reference information about the vulnerability. This highlights the importance of communicating your actions with corporate leadership so that they can factor the effects of remedial action in with other issues to make a decision. In some cases, governance may interrupt the application of remedial steps because those actions might negatively affect other business areas. Identity exceptions to policies: There are always exceptions, even on networks. Prior to its disclosure, Symantec products were already blocking versions of the Angler exploit kit known to be attempting to exploit this vulnerability.
CySA+ Chapter 6: Vulnerability Scanning Flashcards

Content strives to be of the highest quality, objective and non-commercial. It play no role in the prioritization of remediation. Sponsored Sponsored Post Sponsored Content is paid for by an advertiser. Please note that this is a developing story. When you scan your computer using it, the updates which are very important for your computer will be displayed there. Not only would you have dramatically increased the attack surface of your organization, but also the downtime because you would have to patch multiple times. We will continue to update this story as our Norton security research teams learn more.
McAfee Support Community

You should pay extra attention to critical vulnerabilities and aim to remediate them within 48 hours. All vulnerability scanners perform reporting functions of some kind, but they don't all come with customization options. This illustrates the importance of testing patches in a safe environment before deploying across the whole enterprise. We need to enter the right information as shown in the picture below: When we input the required information into the web form, we need to click on Register to register ourselves. Although not practical for detailed analysis, this is useful to quickly confirm the status of the host.
HP unveils Flash vulnerability scanner

In addition, you will find them in the message confirming the subscription to the newsletter. Another reason for a false positive could be that you've already determined the appropriate compensating control for an issue, but not have yet correctly disposed of the alert. Just as troubling, working exploits used to take advantage of this vulnerability were discovered in the , which is one of many tools sold on the underground market that help criminals commit cybercrime. So install the updates manually so that you will not be having any issues. Because of this, zero-days are prized by cybercriminals who have knowledge of them and are used for as long and as quietly as possible. Although Nikto lacks a graphical interface as a command-line executed utility, it's able to perform thousands of tests very quickly and provide details on the nature of the weaknesses.