Expressvpn android hotspot. ExpressVPN 2019-02-03
ExpressVPN

Reading the company's terms of service is a great way to figure out the logging and data retention policies. Breaking them can sometimes mean being banned without a refund. Free version does not require registration. One example of a classic is to use a bogus network to intercept victims' web traffic and replace legitimate sites with fake ones. If you have a slot available, you can add a shortcut to the list by tapping the green add + icon. Cons: Relatively few servers and locations.
Download the Best VPN App for Android

You'll want to make sure you have enough licenses to cover all your mobile devices and computers, too. To remove a location from your list of favorites, swipe it to the right. I keep my connection dropped when going all over over the air. Make sure you have first. Nevertheless, Hotspot Shield competes with a powerful app for Windows that features malware protection and an automatic kill switch. Everything you send, from emails to passwords, would be open to them. To add a location to your list of favorite locations, swipe to the right.
Express VPN for Android

In fact it makes use of the standard tethering application and then fixes up the routing information to make it work. Nevertheless, Hotspot Shield competes with a powerful app for Windows that features malware protection and an automatic kill switch. There's also the possibility that nefarious parties have set up an innocent-looking wireless network specifically to trick you into connecting. Cons: Server locations are not geographically diverse. You can expand and collapse the lists by tapping the triangular arrowheads. Some settings may be confusing to newcomers.
Can I share my Android's VPN connection over a Hotspot?
Cons: Poor performance in testing. Lots of servers in lots of places means that you'll have an easier time finding a nearby server while traveling. I can show receipts for my purchases, I wonder how many of these 5-star reviews can do the same. Ben holds a degree in New Media and Digital Design from Fordham University at Lincoln Center, where he served as the Editor-in-Chief of The Obse. With just a few taps, you can browse the internet securely and anonymously. What's more, many mobile apps still transmit data without encryption, letting various three-letter organizations keep an eye on you. This application does not require you to root your phone but you do need to run software on the computer that you wish to connect to your phone.
How to Set Up a VPN on Android Pie and All Android OS

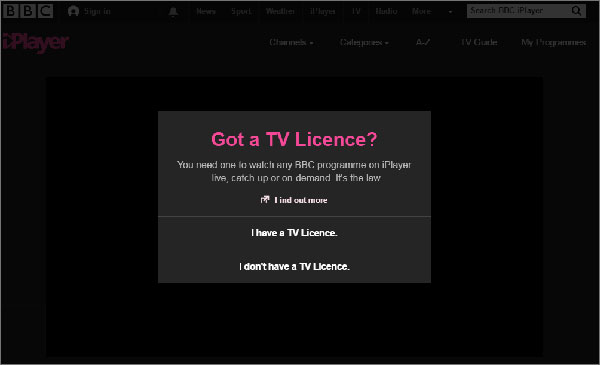
Jump to section Sign in to your account To begin, open a web browser on your device and. Speaking of advertisers, they use advanced trackers that correlate your movements between websites. This is still true when you browse the web on your Android. Depending on where the company has its corporate headquarters, local laws may require the company to retain user data. When you're in a foreign country and you're desperate to get information directions or translation, perhaps , you probably won't be worried about whether or not the Wi-Fi connection you've found is secure.
How to Set Up a VPN on Android Pie and All Android OS
Once you see the Connected message on the app screen, you can begin surfing with freedom and security! To change locations, tap the location flag on the left side of the widget. There are Tor client in Google Play, so you'll have no trouble connecting, no matter where you are. Well-designed and functional Android app. All other apps will be permanently blocked unless you add them to this list. That's not a good thing, especially if maintaining your privacy is your primary concern.
Download the Best VPN App for Android

If your browser or app doesn't secure your information, then it will be entirely readable to someone with the will and the means to try. Journalists and activists have used this to get around restrictive internet controls imposed by various governments. That said, are starting to get wise. The issue of net neutrality is perhaps one that should be decided on by Congress and not left up to individuals to solve, ad hoc. Just don't expect a lot of hand-holding. Slow download and upload speeds in our tests.
The Best Android VPNs for 2019

There are also apps, like , that send encrypted text messages, keeping each message secure even if part of the journey to its intended recipient is unsecured. You can list all the interfaces typing netcfg the root terminal As for terminal emulator, I use : ConnectBot allows a terminal emulator on your device for connections ssh, telnet and localhost. You might not think anyone would be interested in your data, but it's not always individuals who are targeted for surveillance or attack. If you try to use more than three devices simultaneously on one subscription, you will see this screen: Need help? A surfeit of servers also means that you'll have many options when spoofing your location, should you desire it. Our list of the is a good place to start.
Download the Best VPN App for Android

Hotspot Shield also offers a robust Android app that includes malware protection and an automatic kill switch. Purchased this service with a router from flashedrouters. That's a lot of private information you'd probably rather keep private. Underwhelming performance in our tests. Hope it could help I found some information that consists of adding iptables rules using command-line in your rooted device.