Expires in oauth2. Access Token Response 2019-04-16
OAuth2
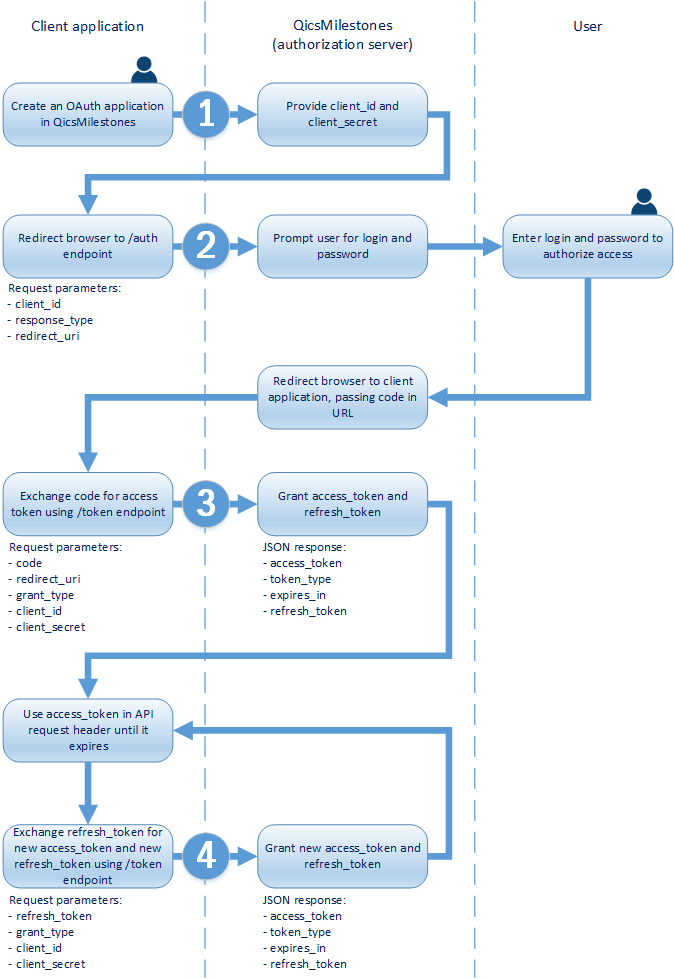
In this request, the client indicates the permissions it needs to acquire from the user. Refresh tokens do not have specified lifetimes. Unlike the Authorization Code Grant Flow, the refresh tokens are not issued with the Implicit Grant Flow. . EnableAuthorizationServer enables an Authorization Server i.
C# HMRC OAuth2 Access Token

Send a new interactive authorization request for this user and resource. Applications can pre-select a token lifetime option, but the user ultimately decides. The app can cache the values and display them, but it should not rely on them for any authorization or security boundaries. By not issuing refresh tokens, this makes it impossible to applications to use the access token on an ongoing basis without the user in front of the screen. Will this access token expiry time reduced in future for better security? The user should be prompted to consent. For example, an additional authentication step is required.
Is it possible to know when an OAuth2 token expires?

I am doing all the things on my server side. Defining New Authorization Endpoint Response Types. When the token is revoked, all tokens are revoked for that user. Read about to learn how to register your certificate and the format of the assertion. The interaction between the authorization server and resource server is beyond the scope of this specification. Goland, Dick Hardt, and Allen Tom. The available transformations are S256 and plain.
Create expires_in method for access tokens by kaborso · Pull Request #210 · oauth

Further information on Internet Standards is available in. By continuing to use the site, you agree to the use of cookies. To ensure fewer authentication prompts place it in the authorization request to ensure consent is received from the user. For web applications, do not use an iframe. The Authorization header is not used. If the response contains the scope parameter, use the scope value in the request to the resource. Authorization Header The Authorization header must be set to Basic followed by a space, then the Base64 encoded string of your application's client id and secret concatenated with a colon.
orgmode.com HMRC OAuth2 Access Token
This may also be returned if the request includes an unsupported parameter or repeats a parameter. More than nine years I'm writing commercial projects. We do not store any user details. Sign up for a free GitHub account to open an issue and contact its maintainers and the community. The Security Considerations section was drafted by Torsten Lodderstedt, Mark McGloin, Phil Hunt, Anthony Nadalin, and John Bradley. Access tokens and refresh tokens may be up to 1,024 bytes in size.
Understand the OAuth 2.0 authorization code flow in Azure AD
Is there any recommended time? Then, you can continue with our article on using a Zuul proxy. A single authorization server may issue access tokens accepted by multiple resource servers. Before the authentication request is sent, we will set a cookie named remember based on the parameter: function obtainAccessToken params { if params. Making an access token never expire is a high risk; one that I would never take, myself. Can be one of plain or S256.
Azure AD Service to Service Auth using OAuth2.0

To ensure fewer authentication prompts place it in the authorization request to ensure consent is received from the user. May be fewer than the application requested. However, this behavior could be used in a phishing attack. Hi , Thanks for your reply. Elements are presented in the order first defined.
Access Token Response

Error codes for authorization endpoint errors The following table describes the various error codes that can be returned in the error parameter of the error response. The token store is used to store the token. Client 2: RestTemplate based java application Method sendTokenRequest is used to actually get the tokens. Yikes, I wanted to blog about refreshing an access token first, but instead I went on writing about the implicit flow today. For example, it might be missing a parameter or using the same parameter twice. The implicit grant type is also a redirection-based flow but the access token is given to the user-agent to forward to the application, so it may be exposed to the user and other applications on the user's device.