Eset sysrescue live uefi. ESET® SysRescue Live 2019-02-18
How do I use ESET SysRescue Live to clean my computer?—ESET Knowledgebase
It should work in most cases, but you may experience some unreported issues with your system. Key Features: Script-Based Attack Protection Detects attacks by malicious scripts that try to exploit Windows PowerShell. Mozilla Firefox, Google Chrome, Microsoft Internet Explorer and Microsoft Edge browsers are all supported. However, please note that the drive will be formatted, so make sure you created a backup of your data. You can boot an infected computer from your rescue media to scan for malware and clean infected files. This app can be used to scan and clean your system so that reinstallation would be okay. This is done by accessing the file system as well as the hard disk allowing meticulous on-demand boot sector or existing partition scans.
ウイルススキャンLiveCD
The download was completed in around six minutes. Back up any existing data before you begin. If you still cannot update, try to update at a later time. The program delivers everything you get with its core antivirus package: malware and ransomware blocking, web browsing and antiphishing protection, and a social media module to keep you safe from malicious content. Quarantined items can be browsed, restored or deleted with just a click. For more information for licensing and pricing options. If the disk check returns errors, it is possible that the rescue image is damaged.
ESET® SysRescue Live

There are various scan profiles you can choose from and the application enables you to customize them by choosing the folders or files to include in the analysis. You can boot an infected computer from your rescue media to scan for malware and clean infected files. The function keys F1-F4 are useful if you want to specify special booting parameters. If infected files that cannot be cleaned are found, you will be prompted for the action to take with these files. Home Network Protection scans your local network for vulnerabilities, including weak passwords and out-of-date and firmware, and helps you track all your connected devices. The timeout can be interrupted by pressing any key. The scan results are logged to file and the application can display detailed statistical data and conclusive graphs regarding system protection.
ESET SysRescue Live 1.0.16.0 Crack With License Codes 2019

There are various scan profiles you can choose from and the application enables you to customize them by choosing the folders or files to include in the analysis. Mozilla Firefox, Google Chrome, Microsoft Internet Explorer and Microsoft Edge browsers are all supported. A new Webcam monitor tracks everything using your webcam, alerts you to any unexpected processes and allows you to block them. This makes it possible to remove threats that under normal operating conditions might be impossible to delete for example, when the operating system is running, etc. Please contact your system manufacturer for more detailed instructions. The download was completed in around six minutes.
Starting ESET SysRescue Live

This is done by accessing the file system as well as the hard disk allowing meticulous on-demand boot sector or existing partition scans. The scan results are logged to file and the application can display detailed statistical data and conclusive graphs regarding system protection. Its major advantage is that it runs outside the operating system, directly accessing the file system and the hard disk to run thorough on-demand scans of the boot sector or existing partitions. Vyberte si jednu z níže uvedených možností, a neunikne vám žádná důležitá technická informace. Also detects malicious JavaScripts that can attack via your browser. There are various scan profiles you can choose from and the application enables you to customize them by choosing the folders or files to include in the analysis.
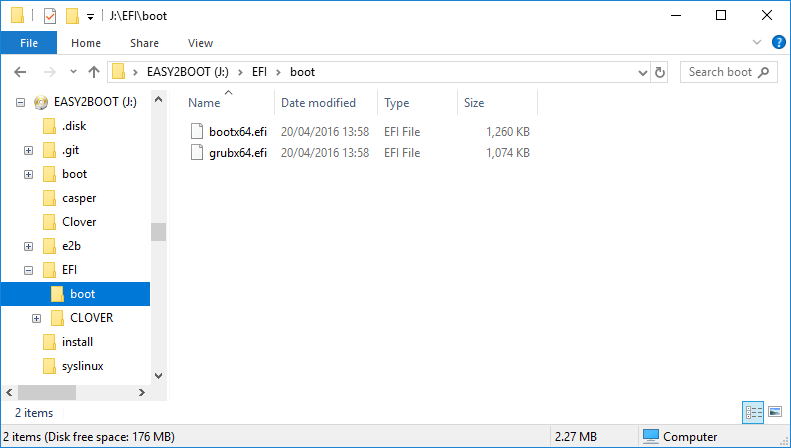
Rescue Disk and UEFI drives
In this case, you will need to recreate rescue media as described in the Installation steps. It can render your systems inoperable no matter how high end it is, it will still be attacked and there is nothing you can do about it until now. Helps scan results are logged to file and the application can display detailed statistical data and conclusive graphs regarding system protection. Quarantined items can be browsed, restored or deleted with just a click. Its major advantage is that it runs outside the operating system, directly accessing the file system and the hard disk to run thorough on-demand scans of the boot sector or existing partitions.
ESET SysRescue Live

Rising up to its developer's name, it helps you scan your system from the outside, performing a deep analysis of the file system and the storage unit so as to remove resolute threats. Mozilla Firefox, Google Chrome, Microsoft Internet Explorer and Microsoft Edge browsers are all supported. This makes it possible to remove threats that under normal operating conditions might be impossible to delete for example, when the operating system is running, etc. Chci dostávat novinky na e-mail Informace z centra technické podpory vám můžeme zasílat na e-mail. It can render your systems inoperable no matter how high end it is, it will still be attacked and there is nothing you can do about it until now.
اسطوانة الحماية ESET SysRescue Live 1.0.16.0

Also detects malicious JavaScripts that can attack via your browser. Use this tool if you experience system or computer malfunctions. There are various scan profiles you can choose from and the application enables you to customize them by choosing the folders or files to include in the analysis. Poznámka: Přihlášením budete dostávat informace ze všech kategorií. Quarantined items can be browsed, restored or deleted with just a click. Nemůžete si zvolit konkrétní oblast zájmu. Check out Full List of Cracked Version of Antivirus Software.
ESET Smart Security 11.0.159.9 Crack License Key Free Download { 2019}

Autor: Martin Buchta Vytvořeno: 11. Tato služba není využívána k marketingovým účelům. Also detects malicious JavaScripts that can attack via your browser. × Buďte o krok před škodlivým kódem Zůstaňte s námi v kontaktu, mějte přehled o produktových novinkách a dostávejte informace o lokálních spamových, phishingových a malwarových kampaních atp. The previous release extended the package with specialist script protection, blocking malicious PowerShell scripts, dangerous JavaScripts and more. Quarantined items can be browsed, restored or deleted with just a click. Check out Full List of Cracked Version of Antivirus Software.