Eset nod antivirus license key 2019. ESET NOD32 Antivirus 12.1.34.0 Crack With License Key 2019 [Latest] 2019-01-18
ESET NOD32 Antivirus 12 License Key 2019 Free Download

This, coupled with other tools such as the Exploit Blocker? It protects against hackers, ransomware and phishing. Security features detect security of the network attack, firewall wall, and tractor. Play, work and browse the internet without slowdowns. If your pc got infected with malicious threats then this software is the best option for you. Specify guidelines for the unit registry, operating methods, and programs, and fine-tune your safe practices. To Be Able to steal Your Company valuable information or disrupt your Company actions, cybercriminals are constantly altering their malicious code or strategies to evade safety defense. Inside the checking period, you can perform anything at all on your computer.
License Key Eset Nod32 Username And Password 2018
The protection that is anti-Phishing inhibits fake websites from obtaining your private data, such as usernames, passwords, and deposit particulars. Anti-Phishing module protects you from faux websites seeking to gather your private records. One of the amazing feature it offers both online and offline protection to your computer. Well done Its heuristics is powerful in discovering the viruses whose signatures Not yet being present. Security features include network attack security, a firewall, and tracking that is a botnet. Is there a way I can transfer all my wordpress content into it? It ought to be noted that research can reach up compressed or protected files.
ESET NOD32 Antivirus 2019 Crack With License Key

Malware authors are driven by profit motives and show no indication of slowing. Because it saves your valuable time. To Be Able to steal Your Company valuable information or disrupt your Company actions, cybercriminals are constantly altering their malicious code or strategies to evade safety defense. Detects attacks by malicious scripts that try to exploit Windows PowerShell. You from new assaults, even all through the central first hrs at the point when other merchants. This summary includes information about detected threats, blocked web pages, intercepted spam emails, blocked webcam accesses and more.
ESET NOD32 Antivirus 2019 V12.0.31.0 License Key Crack (X86X64)

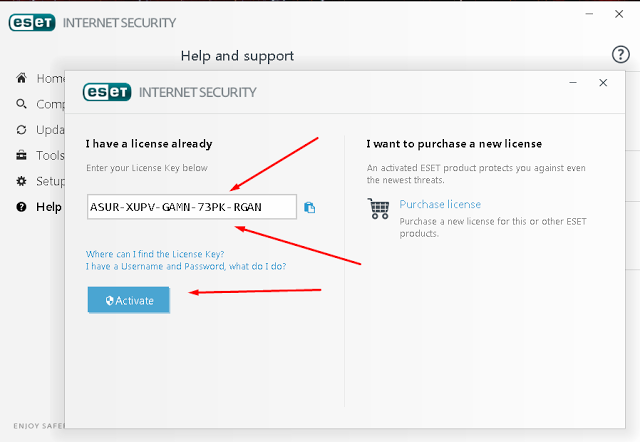
It a cost no ifs and or buts, however with the probability to endeavor it to no end out of pocket for 30 days. Use the below cite merchandise keys that are official and activate your software. Just if any problems arise just like you install and run the technology, it begins scanning and removing threats and will advise you. One Click Solution: Lets you view your protection status and access the most frequently used tools. Enjoy the full power of your computer. Helps to proactively stop unknown malware based on its behavior, by comparing it with our cloud-based reputation system. With spreading out perils on the web, with components contrasting from the lessening of checking.
License Key Eset Nod32 Username And Password 2018

Also, the program detects and disables both recognized and unknown viruses, trojans, worms, spyware, adware, rootkits, and different Internet threats. This, coupled withother tools such as the Exploit Blocker? There are several steps ahead, while the opponents need to be back behind some steps. They increase their ability to customize according to their needs, use alarms and have a user interface. Then, unpack also launch the software setup to install. Anti-Phishing module protects you from faux websites seeking to gather your private records. Several steps have proceeded ahead while The opponents do things to drop a couple of steps back. Another downside: the lack of additional features will frustrate more advanced users.
ESET NOD32 AntiVirus 12.1.31 License Key 2019 Free Download

The modern-day Social networking Scanning device stretches protection. It goes from inside the background, reading your device and attacks being stopping slowing down your pc. Additionally, complete the installation and restart your Pc. All your passwords in one place: Safely stored and generated where you want. Because it is capable to do the tasks you want your antivirus to perform.
ESET NOD32 Antivirus 2019 Crack With License Key

And the package is also more compatible, running properly on Windows 10, and with a mail plugin which fully supports Windows Live Mail and Office 2019. Fits any type of system environment. It has all the features you are looking for. The year 2018 has begun, and we need our readers to take benefit of this brand new year since we with Eset in cooperation are currently giving out secrets. Users are integrated entirely superior and secure tools and functions that maintain your computer fully at ease from all styles of malicious threats. Another downside: the lack of additional features will frustrate more advanced users. Gives you the option to specify rules for system registry, active processes and programs to fine-tune your security posture.
ESET NOD32 Antivirus 2019 Crack With License Key

You already know therefore significantly in terms of this matter, made me in my view consider it from so many numerous angles. The modern-day Social networking Scanning device stretches protection. It reveals how nicely you perceive this subject. Lets you customize the behavior of the system in greater detail. The Antiphishing module now blocks scam sites and allows feedback both reporting of suspect sites and false positives from users. Another downside: the lack of additional features will frustrate more advanced users.