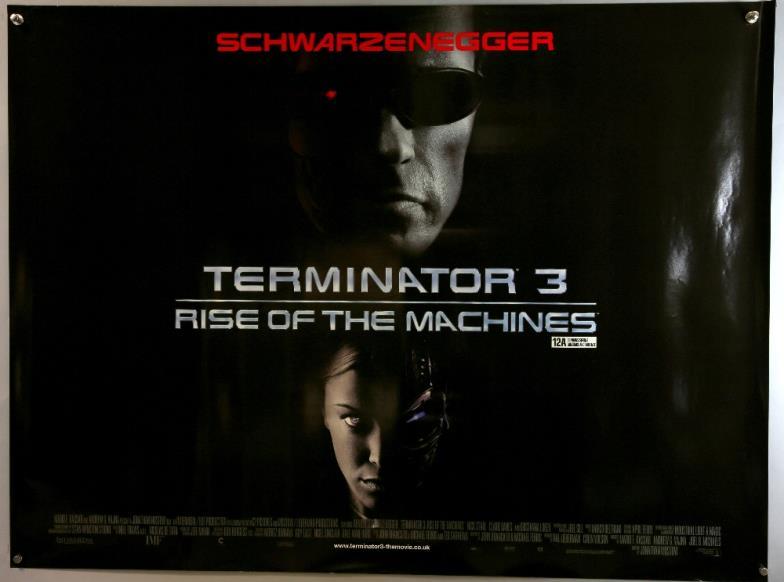
Eraser film poster. Eraser Movie Poster Software 2019-03-03
JUNIOR MOVIE POSTER 1 Sided ORIGINAL ROLLED 27x40 ARNOLD SCHWARZENEGGER

They kill Petrovsky, his henchmen, and DeGuerin's mercenaries. This option is only available after you have won an auction or completed a buy it now purchase. The first reports of cyber attacks appeared in the media and social networks on Friday, May 12. This can also be the contents of the entire hard disk or the Documents folder. Along with Agents Calderon and Schiff and newcomer Deputy Monroe, they raid a remote cabin and kill mercenaries holding DeGuerin's witness hostage, but DeGuerin discreetly kills her when the mercenary leader reveals DeGuerin as the mole. A complete guide for assessors Google is a 160 pages book. The screenplay went through numerous drafts with some of the most prominent screenwriters in the business, with a great deal of uncredited script-doctoring work being done by and.
Eraser Movie Posters From Movie Poster Shop

Check Out Later: You can choose to check out later, then you will be notified by ebay via e-mail that you have won the auction. Williams came to the attention of the Kopelsons when , the wife of Arnold Schwarzenegger, suggested her for the role. Following shooting in New York production moved to For the action sequence which takes place in the Reptile House of New York City Zoo, interiors were built on the soundstages of the Studios in Burbank,. The section on using the Foreign Language label for pages in a foreign language like Ukrainian and Russian is replaced with an example of Catalan and Spanish. A window that offers you to create a website appears after the confirmation of the company page. After erasing mob witness Johnny Casteleone, Kruger is given a new assignment by his boss, Chief Arthur Beller, to protect Lee Cullen, a senior executive at Cyrez Corporation, a defense contractor. One of the most demanding action sequences in the film featured the character of Kruger forced to flee from a speeding through the skies at 250 miles per hour.
Eraser 1996 Poster

The virus infected computer networks of the Ministry of Internal Affairs, Megafon and other organizations in Russia. Using a mainframe backdoor in Donohue's terminal, they decrypt Lee's second disc. Additional rewrites were made by as a favor to Schwarzenegger. So, people will be attracted towards them. Checkout Check Out Now: Click the pay now button at the top of the page to proceed to checkout and process your payment.
Eraser Movie Posters From Movie Poster Shop
DeGuerin has Kruger and Lee branded as fugitives. The was initially the work of Tony Puryear, who had a background in and videos. Why should you use posters for an event? They can't escape before the train slams into the limo, killing all three. Therefore, referential audits are needed if there were any violations in the history of the resource. About 65% of all the reports led to manual sanctions. The shot took seven takes to get right.
Eraser Movie Poster Software

We are still investigating what we can do about it. The reason is that the crawler already scans the content that fast, so the benefits that the browser receives web pages loading time is decreased are not that important. Thus, in the case when before a website owner was engaged in buying links or using other prohibited methods of link building, then conducting an audit of the reference profile and rejecting unnatural links is necessary in order to avoid future manual sanctions. Synopsis: The infamous cult classic about a numb-brained everyman wandering through what amounts to a sick, ironic parody of the modern urban landscape, innocently impregnating his girlfriend and fathering a pestilent embryonic mutant. Kruger saves Cullen from Scar at , who pursues them; Kruger releases several alligators that devour Scar. In addition, it will be optimized for cross-platform devices.
Image Gallery eraser 1996 poster

It is important to remember that rejecting links can lead to a decrease in resource positions in the global search results, since many webmasters often reject links that actually help the website, rather than doing any harm to it. Or they can process them in different ways, taking into account Noindex attribute. You need to verify ownership of the company page in My Business to access the tool. A more positive review came from , who gave the film 3 stars out of a possible 4. It is noted in Europol that the motivation of hackers is not fully understood. Using Canonical, you are telling that two pages should be processes identically.
60 Best Eraserhead images

For instance, the pseudoscientific and fake content details have been clarified, comments displaying pornographic ads on websites that do not contain adult content have been removed, new examples of pages with the lowest quality have been introduced, as well as a completely new section on the display of results in English for non-English-speaking locales. The new feature is primarily targeted at corporate Google Drive users. They can be used for anything and everything. We can cache data and make requests in a different way than a regular browser. With the help of a new tool they will be able to create them. After finding Lee's hidden camera and threatening her with a pistol, Donohue commits suicide in front of her.
Eraserhead Movie Posters From Movie Poster Shop
Vice President William Donohue, her boss, detects Lee's intrusion and orders her into his office. The data and photos placed on it will be used to create the website. You had elements that were live action, elements that were miniature, sometimes computer-generated, and they're all married together in the final processing. I was excited about doing a film that had heroic proportions. Surreal and bizarre, the film has an inner, completely unpredictable logic all its own.
60 Best Eraserhead images

New badges will not always be displayed just like extended snippets. Revealing he, Calderon, and Schiff are corrupt, DeGuerin explains he is the go-between for the black market buyer, and Kruger from the plane to rescue Lee from DeGuerin's mercenaries. By buying 1 Displate, you plant 10 trees. Since the auto update to Backup and Sync is not planned, the company recommends installing a new application immediately after being released. Typically, this type of attack is revenue-oriented. This time, the changes are even smaller than in the previous version of the document, which was published in May 2017.