Encrypted pdf file unlock. 3 Best Ways to Unlock Password Protected PDF File for Editing 2019-01-17
How to remove encryption from a PDF file

It is doubtful that the resulting downloads can be copied or shared as they would remain encrypted and controlled within the Bookshelf downloads folder where they can spy on users and report on their whereabouts when opened. Document object that you pass to another LiveCycle method to perform an operation. It could have been called something like pdf-to-pdf. Most modes support processing files in a bulk. Bookshelf apps appear to be proprietary and not recommended. The mere presence of source code does not guarantee absolute safety. Files with an owner password can be unlocked instantly.
Top 10 Protected PDF Hacks

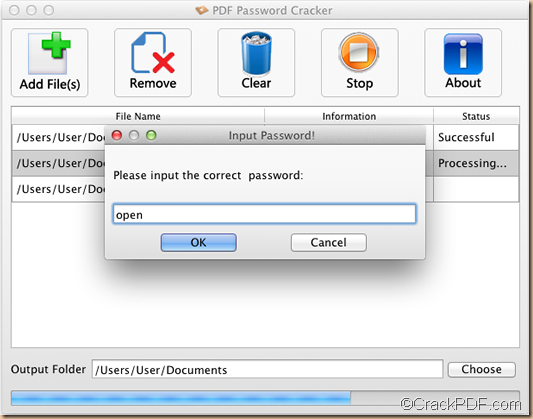
There are simply too many possibilities. . The first password is known as document open or user password, and the second is permissions password also known as a master or owner password. In some instances, password-secured permissions within documents only allow users to fill in forms, and can prevent individuals without passwords from copying or printing text. Hopefully you guys found this article useful and will share it with your friends and families on Social Media. BasicHttpBinding object by getting the value of the EncryptionServiceClient.
PDF Password Recovery
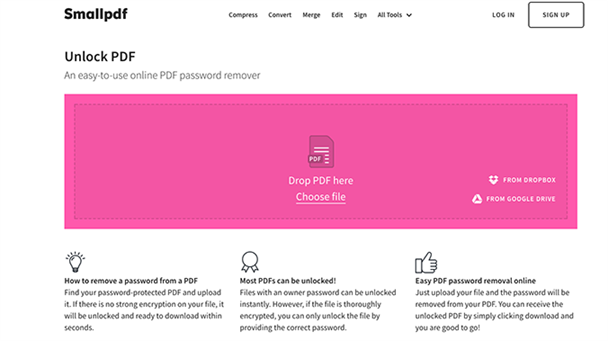
With the right software, the owner password can be removed instantly. Your files are deleted one hour after processing. These websites are not very efficient and may disappoint you. But you need to choose the third-party software very carefully. Basic to the field BasicHttpBindingSecurity. They do not actually work against 3rd party server passwords. Step 2 Password Unlocking Settings There are three types of password unlocking engines within the program.
How to Remove a Password From a PDF File

This online password remover is totally free. This hack can not and does not work over the Internet with content locked by a 3rd party plugin. If we need a password from you, it will not be read or stored. Taking Bruce-force with Mask Attack as an example, you'd better set the mininal and max length. You can determine the size of the byte array by getting the System. These programs could contain anything. The process might take hours or even days.
Unlock Encrypted PDF File without Password to Read/Edit/Print
However, due to the cost we incur by launching tens of high-end servers to unlock the file in such a short period of time, this service comes cannot be offered for free. This browser is more or less available to everyone! It all depends on your computer's processing power. That is they are programs for which no source code can be viewed. Additional may track the file whenever and wherever it is opened, reporting potential Copyright violations. The key here becomes knowing something about the password, and using that knowledge to somehow limit the passwords that are attempted.
How to Remove a Password From a PDF File
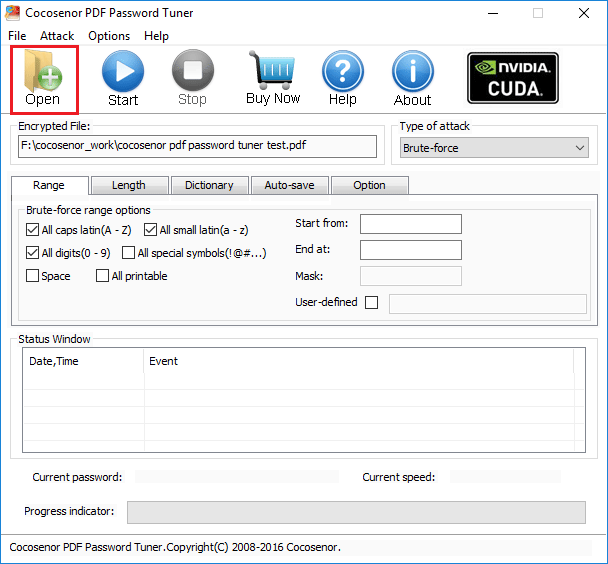
Step 3: Scan password recovery type in Type of attack drop-down list, and choose one appropriate. New viruses, bugs, and backdoors are made all the time. No sign up for subscription required. No need to update your software, or deal with installation issues. You can also try file decrypt tool or software for help. Will this product allow me to retrieve or by pass the password? Furthermore, one could surmise that renaming. You can either save the files in the same location as the source files or save them in your preferred location.
Adobe LiveCycle * Unlocking Encrypted PDF Documents
All files are processed in the cloud and there is no need to download or install any software. These operations can belong to other services, such as the Reader Extensions Service. However, if the file is thoroughly encrypted, you can only unlock the file by providing the correct password. We expect to be able to modify our digital assets for our own uses, such as for offline presentation on other devices. Just follow and see how to fix this trouble on your own now. But most of the time users get an error message! If not, there are plenty of free ones available. This makes sense having read somewhere that there is usually no problem with renaming.
How to Unlock a Password Protected PDF File

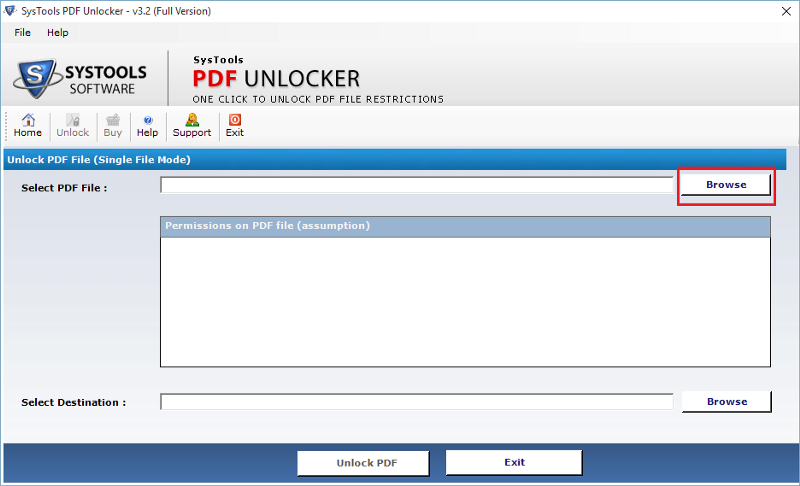
It is not good practice to go around downloading and running proprietary software. Why Cracking is Not Necessary This information is provided for personal, professional, and educational use only! They would have to hack the server to do that. Why Use Free and Open Source Tools? Owner passwords can be found with the -o switch. All these features are available through modern and user-friendly interface. It is not very effective or efficient but it works sometimes. Your document may have been protected using different types of password restrictions.
12 Free PDF Password Recovery

It is a Windows installable program that is compatible with all Windows versions including the newest Windows 8. This process takes several days on one home computer. When you upload a file it is transmitted using a secure connection. The more you set, the faster the password will be cracked. So performing a dictionary search by going over the words, their combinations and variations allows saving your precious time.