Encrypted itunes backup forensics. How to Find Passwords for Encrypted iTunes Backups 2019-02-25
iPhone Forensics
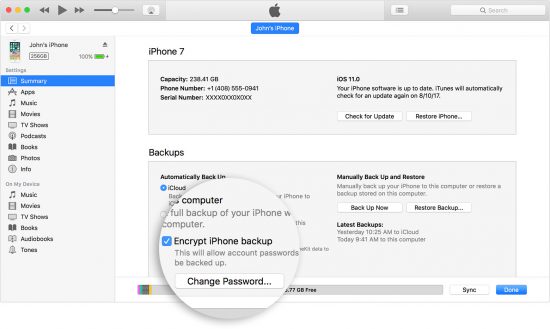
Later these class keys are used to decrypt the protected files in the backup. It includes backup state, a flag to identify the full backup IsFullBackup , date and version, etc. Encrypted iTunes backup cracking As we explained in , Evidence Acquisition from iDevices, and in the first part of this chapter, an iTunes backup can be encrypted with a password chosen by the iDevice user. Your tool can only get you so far. So it is really important for you to remember the password of your encrypted iPhone backup in iTunes.
Encrypted itunes backup.
If you have the ability to get a full file system dump, even better. List of protection classes available for the files are shown in Table 1. In February of 2017, this loving couple was on their way to see a Badgers basketball game. The script decrypts the Backup Keybag, grabs the protection class keys from 6 to 11 listed in Table 2 and decrypts the keychain items. To protect your privacy and security, you should only run these scripts on a machine with full-disk encryption. Keys in the Backup Keybag facilitate to store the backups in a secure manner.
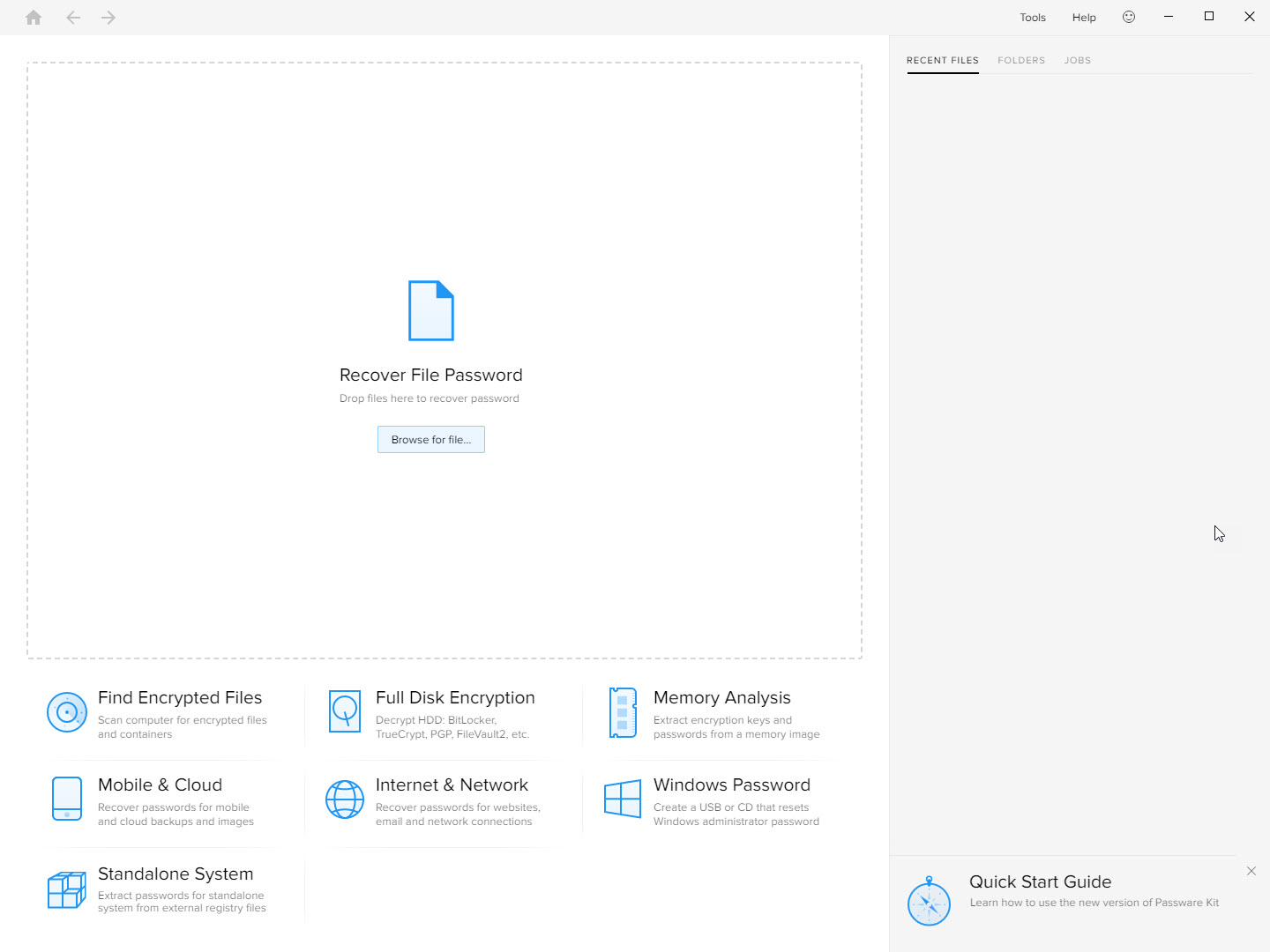
Smartphone Forensics Investigations: Using HashCat to Crack an Encrypted iTunes Backup

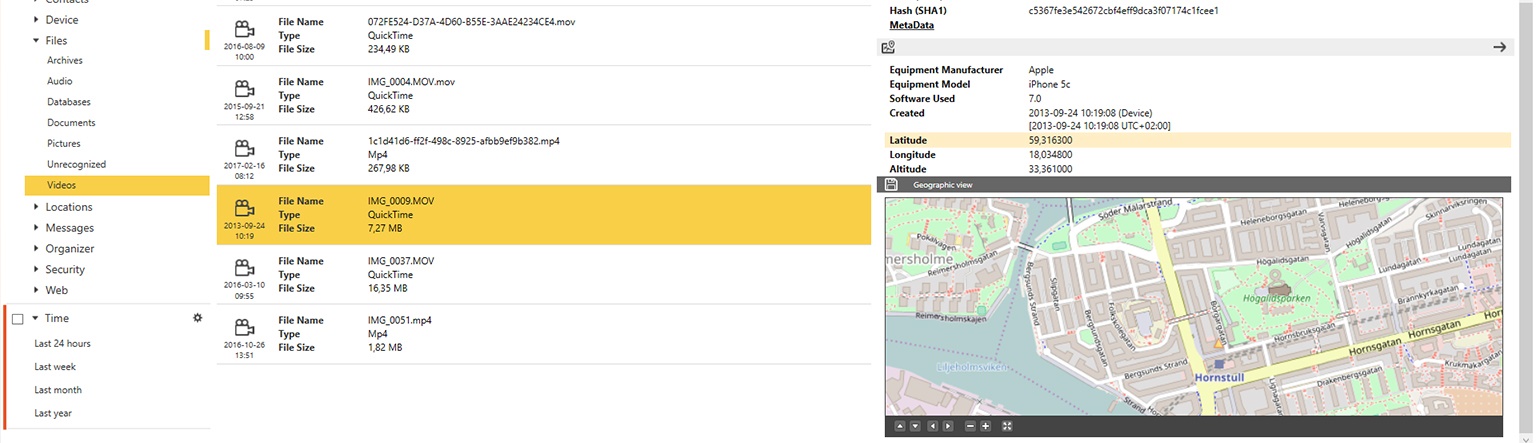
We had the credentials and consent to access the account. These file keys are stored wrapped by a class key from the Backup Keybag. How to Turn Off iTunes Backup Encryption? Now that you know how to enable encrypted backups, you can sync all of your private information to iTunes, including passwords and Health and Fitness data. Below, you can see what Physical Analyzer is reporting for my location information. Backup files created by iTunes are platform independent and can be moved from one operating system to other. If the backup was encrypted, you will see a lock next to it.
iTunes backup forensic analysis

The first was 0000 and Elcomsoft laughed at this and provided the password before I could even sit back in my chair to watch. The behaviour can be observed by looking at different timestamps for the files in the backup. So decryption of protected files in the normal backup is not possible without having access to the actual device. Of course, you must know user-password, but if you do — you can get the password for the iTunes backup you found. On the iPhone, protection class keys are stored in the System Keybag. A password is required to enable and make changes to your encrypted backups. The difference between being successful in getting to the data or failing lies in carefully thinking about the problem and considering options.
Magnet AXIOM 1.0.10 Now Lets You Decrypt iOS 10.2 iTunes Backups
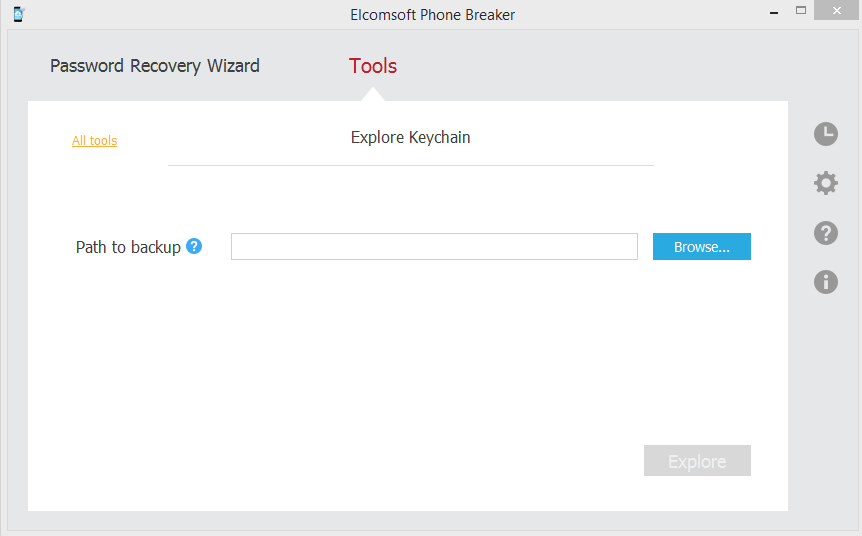
But could I be sure that I could do that without losing user data? When the stakes are high, thinking through things is important. Unwrap each wrapped key according to. Make sure it's a password you will remember -- or write it down for safekeeping. However, you cannot see how many backups exist, let alone the dates of their creation. Maybe you can actually get answers directly from Apple's security team if you tell them your good intentions. But the good news is that you can actually turn off backup encryption in iTune without the password. I used Elcomsoft Phone Breaker v 6.
Encrypted itunes backup.

Escrow Keybag allows a paired device normally a computer to gain full access to the iPhone file system when the phone is in a locked state. One can restore an encrypted backup to a different device, which suggests all information relevant to the decryption is present in the backup and iTunes configuration, and that anything solely on the device is irrelevant and replacable in this context. When attempting an Advanced Logical in Physical Analyzer, the option to encrypt the backup is provided if the backup has not been encrypted via iTunes by the user. This will allow account passwords. Once the backup is complete, it will prompt you to open it.
Update: Solutions for iOS10
During the encrypted backup, iTunes prompts the user to enter a password as shown in Figure 3. So the hash of DomainName-filepath will match to the correct file in the backup. It's not, and to my knowledge it hasn't been done. Then, derive the final decryption key by unwrapping it with the class key that was unwrapped with the backup password. Would you like to answer one of these instead? Then, check to ensure that it was properly encrypted. Has anyone tested connection the Iphone device to a new valid Itunes account and making a new backup with no encryption? And if you want to restore the encrypted backups without the password, a iTunes backup password recovery tool may be able to help you. This made me realize that I should write down everything I put into a webcast.
iPhone Encrypted Backup: How to Encrypt iTunes Backup

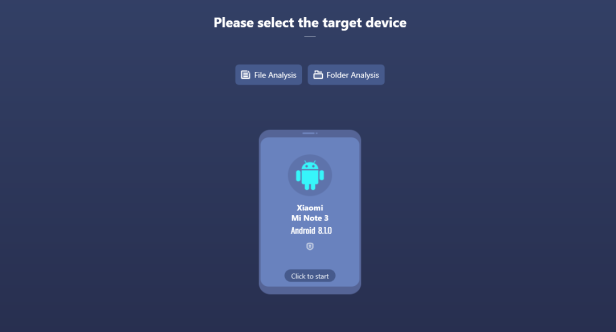
So forensic examiners prefer analyzing the backups to collect the evidence though it is not possible to recover the deleted iPhone data. Have you lost data because you couldn't restore your encrypted backup or maybe forgot the password? This tool is freely available from. Despite the noticeable bend in its body, it still worked! If the automatic sync option is turned off in iTunes, the user has to manually initiate the backup process whenever the device is connected to the computer. The iPhone stores a lot of user data in the backup files. This won't delete your personal data but will erase iTunes backup password as well as reset settings like display brightness. This is easy when they are unencrypted, but not when they are encrypted, whether or not the password is known. Some of the famous tools are listed here.
Decrypting encrypted iTunes backups
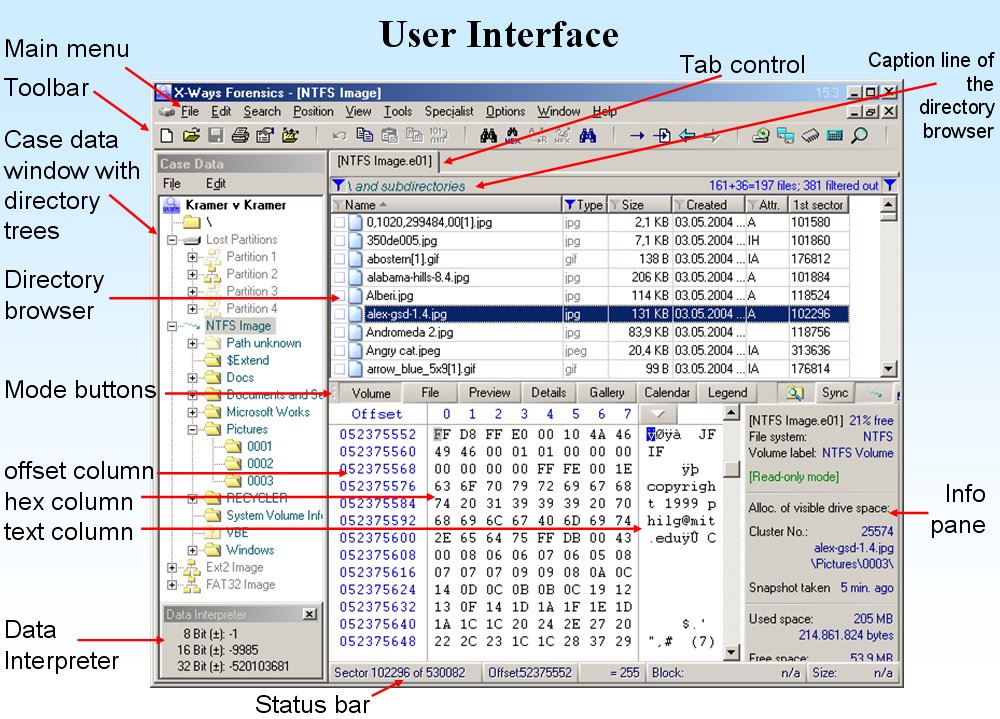
Also, if you don't need this feature, we will also show you how to turn off encrypt iphone backup on iTunes, especially how to turn it off when you forgot the iPhone backup password. In 2019 — I am going to write down what I talk about in webcasts. Even if the password was known, the tools were choking on the data. However the file cannot be opened as the content is encrypted. Is there a way to choose which one to extract, or do i have to pay to extract all 80 when I don't need the other 79 I still have those on my current phone? In critical cases, forensic examiners rely on analyzing the iPhone logical backups acquired through iTunes. Backup file structure in older version of iTunes is managed by two files — Manifest. Unlock your encrypted backup by typing your backup's password.
Magnet AXIOM 1.0.10 Now Lets You Decrypt iOS 10.2 iTunes Backups
If the backup file is corrupt and encrypted, even if you know the password to it you will not be able to restore. As such, I'm trying to figure out the encryption scheme used on mddata and mdinfo files when encrypted. Make sure it is something that you won't forget. In this example, I can tell you what is true and what is not. After all, even they should know that security by obfuscation is not really efficient.