Elcomsoft ios forensic toolkit full. Elcomsoft iOS Forensic Toolkit 2019-04-30
ElcomSoft iOS Forensic Toolkit 4.0 Free Download

You also may like to download. The most important point is: we never keep our methods secret. Is it possible to perform data carving through unallocated space, or restore deleted files? Extract Adobe reader and Microsoft Office locally stored documents, Minikeepass password database and a lot more. Cracking of the passcode is not possible at all, thanks to Secure Enclave. For the time being as Apple has at long last begun to truly secure the working framework. On the other hand, works only with iTunes and iCloud backups. Access to most information is provided instantly.
Elcomsoft iOS Forensic Toolkit
What is that all about? Image device file system, extract device secrets passwords, encryption keys and protected data and decrypt the file system image. Real-Time Access to Encrypted Information Unlike previously employed methods relying on lengthy dictionary attacks or brute force password recovery, the new toolkit can extract most encryption keys out of the physical device. What about iPhone 5, 4th gen iPad, iPad Mini, and latest iPod? If a lockdown record is used, some files may not be accessible unless the lock screen passcode is removed. Access to most information is provided instantly. Breaking these passcodes is much more lengthy, considering that the recovery speed is about 5 passcodes per second.
ElcomSoft iOS Forensic Toolkit 3.0 Full Crack Fshare

This step returns less information than physical acquisition and it is recommended to create a logical backup of the device attempting more invasive acquisition techniques. The only way around this problem is using physical acquisition. Once you got it, everything else should run smoothly. What is the benefit of physical acquisition? Presently keep holding down the Home catch for an additional 10 seconds. You can still use the Toolkit with it.
[ASP] Elcomsoft iOS Forensic Toolkit cracked version download

Image device file system, extract device secrets passwords, encryption keys and protected data and decrypt the file system image. At this time, we have no plans to develop such a product. Tôi lập trang web cá nhân hoquangdai. Please follow the instructions carefully. I've got a problem when my problem goes to sleep during Toolkit operation.
ElcomSoft iOS Forensic Toolkit v5.0 Crack [Latest] ~ APKGOD
If a password is known or not set, the acquisition is possible, at least in theory, but would require a special loader specific to each particular device. The possibility of remote wipe routinely makes police officers shut down smartphones being seized in an attempt to preserve evidence. As opposed to creating a local backup, which could be a potentially lengthy operation, media extraction works quickly and easily on all supported devices. Physical Acquisition for Legacy, 32-bit and 64-bit Apple Devices Physical acquisition is the only acquisition method to extract full application data, downloaded messages and location history. Since encryption keys are based on the passcode, most information remains encrypted until first unlock.
ElcomSoft iOS Forensic Toolkit 3.0 Full Crack Fshare
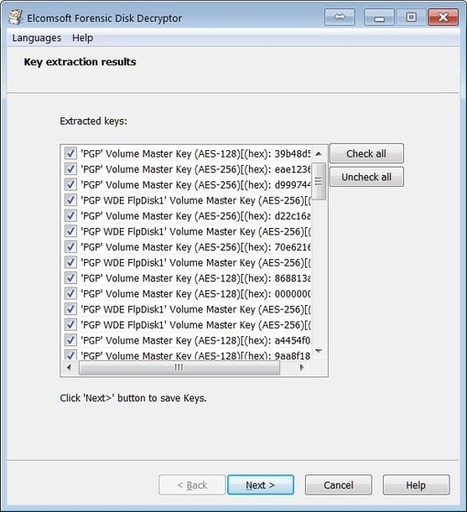
Some problems that may occur can be halted passcode recovery or incomplete device imaging. Instead, the toolbox uses a rootless jailbreak with a much smaller footprint than traditional jailbreaks. In the first step that is a physical acquisition, it extracts full application data, protected keychain items, downloaded messages and location history. It produces a standard iTunes style backup of information stored in the device, pulls media and shared files and extract system crash logs. Extract Adobe Reader and Microsoft Office locally stored documents, MiniKeePass password database, and a lot more. Image device file system, extract device secrets passwords, encryption keys and protected data and decrypt the file system image. If the device is configured to produce password-protected backups, experts must use to recover the password and remove encryption.
ElcomSoft iOS Forensic Toolkit 5.0
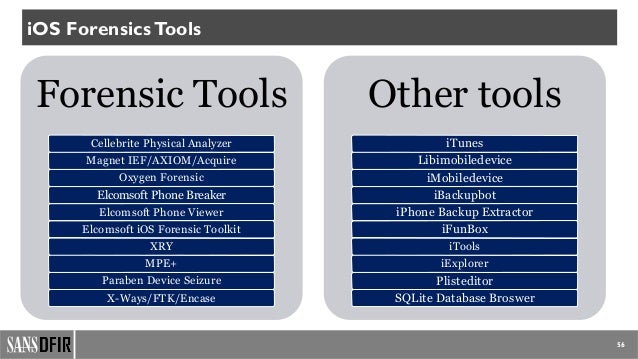
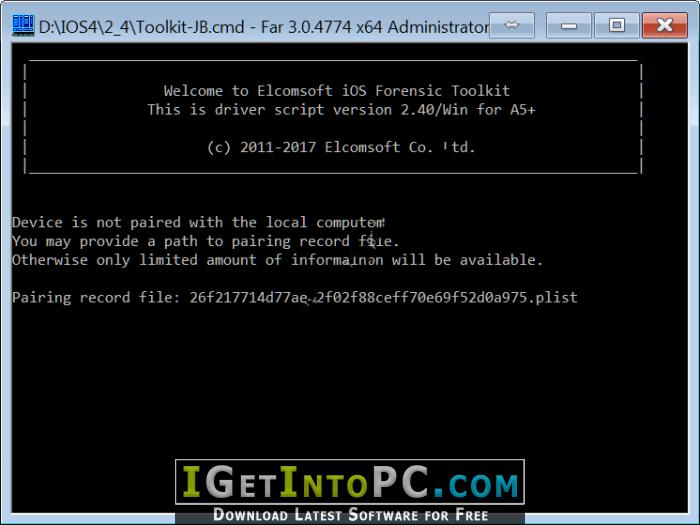
In this mode, you get a text-based menu listing the operations you can perform. In contrast, physical acquisition allows you to get everything, i. What is the difference between Guided and Manual modes? An image device file system, extract device secrets passwords, encryption keys and protected data and decrypt the file system image. The software is useful for quickly extracting multimedia files, such as the camera roll, books, voice recordings and the iTunes multimedia library. Based on the tfp0 exploit, various teams have released their own versions of jailbreaks.
ElcomSoft iOS Forensic Toolkit v5.0 Crack [Latest] ~ APKGOD
The Locked iPhone The use of Faraday bags is still sporadic, and the risk of losing evidence through a remote wipe command is well-known. The cell phone screen goes clear. There are other possibilities as well. Is it possible to run an offline passcode attack, e. Ways to Extract Media Files There is more than one way you could use to extract media files. But please start reading from this version as it provides basic information on the product.
ElcomSoft iOS Forensic Toolkit Free Download

A sensible security control in fact. See Compatible Devices and Platforms for details. Access to most information is provided instantly. The only way to unlock the iPhone 5s and newer is hardware-driven. It can also recover device passcodes some limitations apply. Media and Shared Files Quickly extract media files such as Camera Roll, books, voice recordings, and iTunes media library. While you can still extract raw data, decrypting the data will not be possible, so anything obtained from the device will be completely useless for an investigation.
[ASP] Elcomsoft iOS Forensic Toolkit cracked version download

We are working on adding support for jailbroken devices in the same way as It was made for iPhone 4S etc. Apple is still not without its imperfections. Unlike creating a local backup, which could be a potentially long operation, media extraction works quickly on all compatible devices. Thankyou for reading the article! If a lockdown record is used, some files may not be accessible unless the lock screen passcode is removed. There is something much more important, and it is gong to affect everyone.