Dsploit pro apk. Download dSploit APK 1.1.3c 2019-03-12
Download Dsploit Apk Pro

Start and Stop Network Monitor: For starting or stopping network monitoring process. You may also Like For Using as best vegetable slicer. To install dSploit apk, you android device Not need root. But, to actually execute this, get the basic knowledge of security. Open the app and tap on the module and it will open www. Custom Filter Replace custom text on webpages with the specified one.
dSploit APK Lastest Version direct download
Replace Videos This tool will let you replace all the video on the web page with you customized video. Transfer the apk file to your device and go to the transferred apk file in your device and click on file and click on install button. Packet forger This module aids in forging packets to send to the target. It contains a number of modules that are talented to discuss network safety and security assessments regarding cordless networks. Port Scanner A port of syn scanner to find quickly open ports on a single target.
[ ROOT ] zANTI2 (dSploit) PRO Latest Version APK

Vulnerability Finder Search for known vulnerabilities for target running services upon National Vulnerability Database. Vulnerability Finder Search for known vulnerabilities for target running services upon National Vulnerability Database. It's easy to download and install to your mobile phone android phone or blackberry phone. Replace Images Replace all images on webpages with the specified one. It can additionally scan networks for vulnerabilities, fracture secrets on typical routers, and hijack browser, web site or social network sessions as well as hold on to them.
dSploit APK Lastest Version direct download

On download page, the download will be start automatically. Trace Perform a traceroute on target. Dsploit apk — Dsploit apk download with tutorials Today in this post I am going to tell you about the Dsploit apk and how to use Dsploit tutorials this will be a long post because I will be covering each and every feature of dspolit app. If you have an old version of dSploit anything rather than the last nightly build , please remove it and download manually to have the latest code updates and features. We advise you to take a look at ways to use Dsploit app to delight in the transmission capacity just for you. Here we sharing guide about the how to use Dsploit apk in your android device for solve your regular small problems. Replace images This tool will let you to replace all the image on the web page with you customized image.
★ROOT★ zANTI2 (dSploit) [PRO] Latest APK DOWNLOAD

Allows applications to open network sockets. Root: The device must be rooted. Kill Connections Kill connections preventing the target to reach any website or server. The phone will prompt to give the rooting permission to this or not, go ahead and grant the permissions. Now, you have the app on your Android device and you can open dSploit right after the installation or you can open it from the app drawer; whichever suits you. On download page, the download will be start automatically.
dsploit no root

First, before downloading the app, you need to get root the Android phone or tablet, without rooting access, the tool will not work on your device. Login Cracker A very fast network logon cracker which supports many different services. Root: The device must be rooted. Filed Under: , Tagged With:. Password Sniffer Sniff passwords of many protocols such as http, ftp, imap, imaps, irc, msn, etc from the target. It will display the legal username and password.
dSploit APK 1.1.3c Download

Replace ImagesReplace all images on webpages with the specified one. Furthermore, that also requires some changes that you need to make. It will display a window. BusyBox: The device must have a BusyBox full install, this means with every utility installed not the partial installation. It will show the admission harbor along when the reinforce. BusyBox: The device must have a BusyBox full install, this means with every utility installed not the partial installation. With this tool you can Easily find the connected device with your WiFi networks and it shows the devices on a map as well.
dSploit Scripts app (apk) free download for Android/PC/Windows
Trace Perform a traceroute on target. It will display the admittance harbor along as soon as the bolster. Password Sniffer Sniff passwords of many protocols such as http, ftp, imap, imaps, irc, msn, etc from the target. It is one of the best hacking applications for android users. Now, in order to install third-party apps, these are the steps you need to follow before dSploit installation. Custom Filter Replace custom text on webpages with the specified one.
[ ROOT ] zANTI2 (dSploit) PRO Latest Version APK
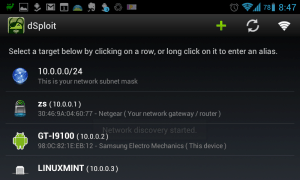
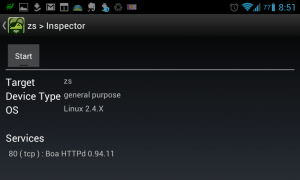
Once dSploit is started, you will be able to easily map your network, fingerprint alive hosts operating systems and running services, search for known vulnerabilities, crack logon procedures of many tcp protocols, perform man in the middle attacks such as password sniffing with common protocols dissection , real time traffic manipulation, etc, etc. Gingerbread: An Android device with at least the 2. Please contact the developer on dSploit issue. Allows applications to open network sockets. Internet Allows to access internet network.
dSploit APK + Mod

Password Sniffer Sniff passwords of many protocols such as http, ftp, imap, imaps, irc, msn, etc from the target. For a safety and security professional, an amateur looking for an inexpensive means to find out more about network safety and security, or somebody aiming to shield their very own network, dSploit can be a beneficial resource. Second, to get the app installed, the setting should be changed. You have to open the dSploit, tap on the Trace module, and then tap on Start. Session Hijacker Listen for cookies on the network and hijack sessions. Session Hijacker Listen for cookies on the network and hijack sessions. This can be done without establishing a referred relationship which is called half-open scanning.