Download dumpper and jumpstart. Dumpper and Jumpstart Download Full Version And How To Use 2019-04-04
Download Dumpper And Jumpstart And Hack Wifi
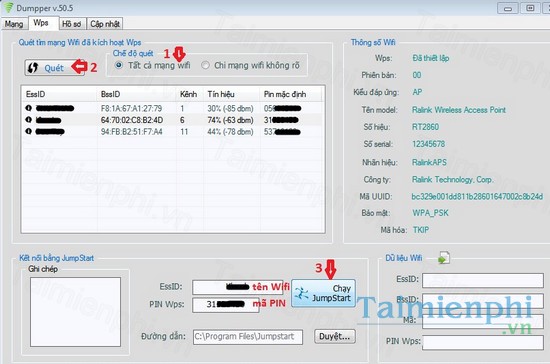
Even though solutions for wireless security have been in place for quite some time, it is estimated that as many as 70% of home networks remain open and vulnerable to security breeches by even the most novice of hackers. So Many People are Doing this Hack in their Desktops. According to Atheros, D-Links Systems, Inc. Update: We have also Added the Process to Hack Wifi in Desktops Below. JumpStart for Wireless addresses this problem by allowing a secure wireless network configuration with as few as three mouse clicks. I will definitely get it solved.
DUMPPER V.91.2 +JUMPSTART+WINPCAP 2018

Do you want to see the password so you can get on from other devices without doing this process? So I will provide the original link for you as well. JumpStart - Populating a development database with identical records presents problems with testing your database applications. I know that writing posts is boring and time consuming. This was made by the creator to demonstrate weaknesses in wireless networks and for educational purposes only. I'm truly sorry if this ever happens. D-Link will be Atheros' customer to offer products containing JumpStart Technology. Sponsored Links: Hacking The Wifi on Desktops? After getting the Product Proceed as Above to hack WiFi with Dumpper and Jumpstart.
DUMPPER V.91.2 +JUMPSTART+WINPCAP 2018

This data will more closely represent what your real data will look like. You cannot download any of those files from here. And it does it very well. I'll help you as much as I can. It is worth the product and it is only last thing you need.
Dumpper v.30.3 + JumpStart Torrent Download
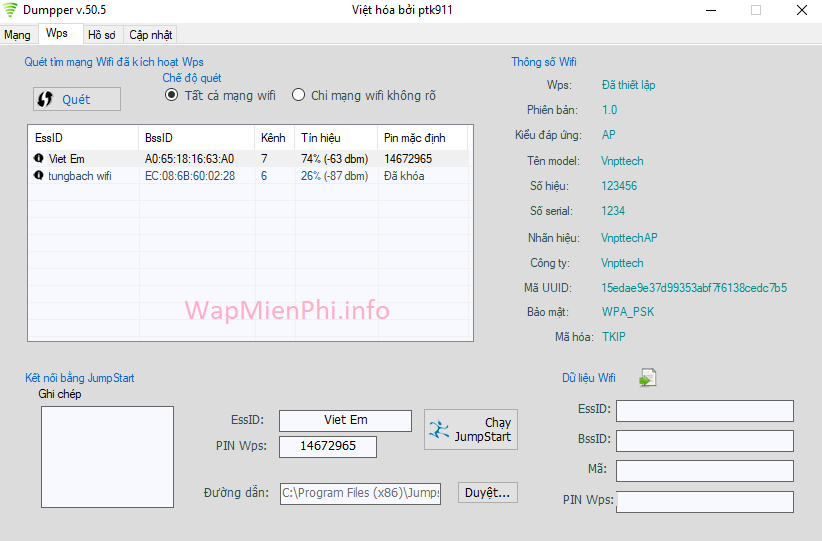
JumpStart creates an encryption key and automatically self-negotiates to the highest level of security level of each device on the network. . First, download all of the programs above. Feel free to ask them to do the same to protect your rights. If you want to test this tutorial, try it on your own home network. You just need to buy the Wireless Adapter and Install it in your desktop.
Dumpper and Jumpstart Download Full Version And How To Use
Be careful of what you download or face the consequences. During the process of your testing, developers tend to put unrealistic looking data into the system because development is usually considered more important than typing in test data. By using a database data initialization tool, you as a developer can populate your database with sample data easily and quickly. The new posts are unique and pass the copyscape test. This list is automatically generated from the torrent file above which is simply metadata for the bittorrent protocol.
Free download JumpStart + Dumpper v 30.3
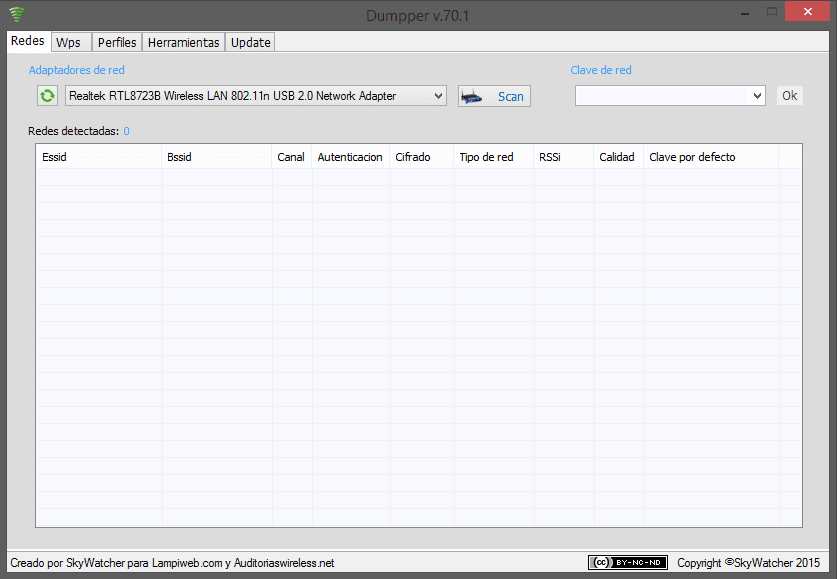
But please note that torrentbag does not cache any torrent files, it's a simple sipder that crawls pages on other sites. But unfortunately Desktops are not compatible for using this Hack. The zip is protected with the password www. With this type of setup, you can now start your application and measure performance against data that is easy to distinguish and provides some variety so that indexes can be tested accurately as well. Additionally, JumpStart supports Microsoft's Wireless Zero Configuration and Windows Connect Now profile management tools. But did you know that there is a tool that allows you to create new posts using existing content from article directories or other blogs from your niche? Another big advantage is you can generate test data for demonstration purposes.
Download Dumpper And Jumpstart And Hack Wifi
Please use the comments section and feel free to ask any question. The advantages to this are that you can setup various scenarios and do performance testing. When you demo the software, the names and other data look realistic. . . . .
Download File List

. . . . . . .
Hack any WPA2/WEP/WPA Wifi using Dumpper and Jumpstart

. . . . . .