Does superantispyware remove viruses. Does spyware doctor just scan or does it also remove virus 2019-01-11
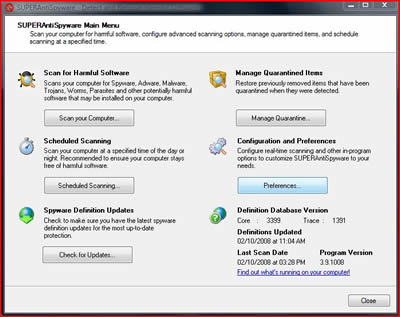
Does SAS detect and remove viruses?
Immediately after being run, it reaches out to api. Go to Trend Housecall see link below and use their free scanner, which works well. As a result they are notalways picked up by virus scanners. Autoruns is a Microsoft tool that shows you the various programs that started up with your current session. Depending on your computer, the quick scan can take anywhere from 5 to 20 minutes, whereas a custom scan might take 30 to 60 minutes or more. If your files have been encrypted by GandCrab, you may still be able to decrypt them. You could try downloading it from www.
Does SAS detect and remove viruses?
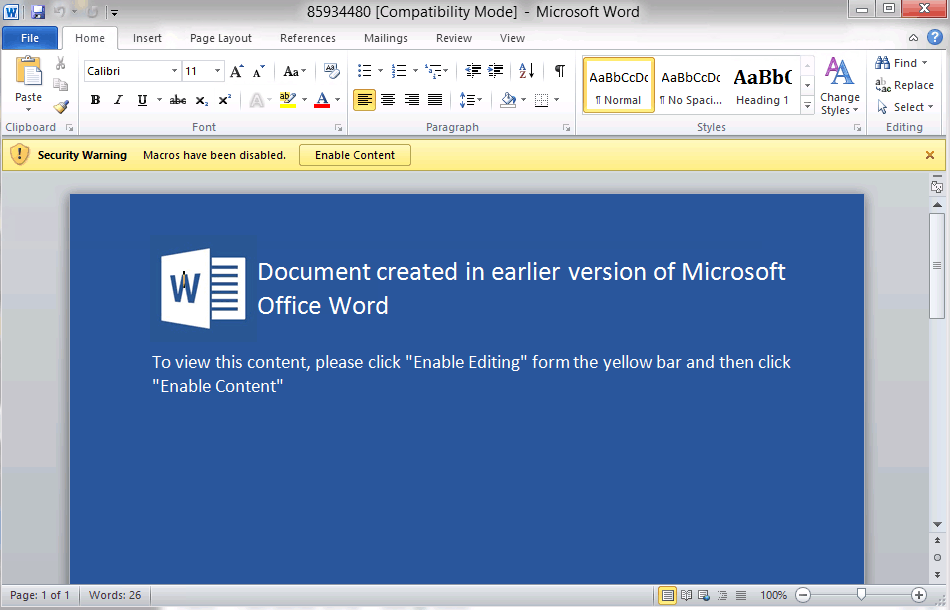
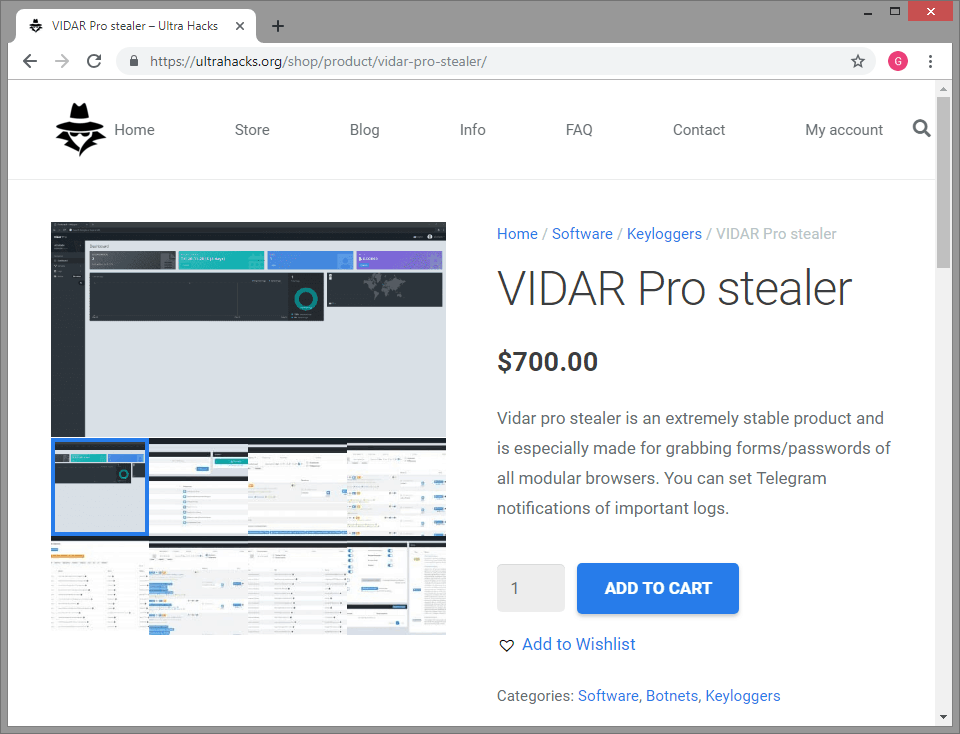
They just want you to buy their product, nothing is ever free. Once you run the malicious file, it begins to encrypt your personal documents, after which it will demand you send payment to regain access to your files. Another fascinating thing about Anatova is its resistance to analysis. The infection cannot run on its own as Microsoft has automatically disabled macros more than a decade ago to help stop these malicious scripts. The last thing that you want to do is to look at the folder location and click on Local. It is of high importance to modify installation settings in order to prevent infiltration of potentially unwanted programs. For example, Trojans may appear to be a Java or Flash Player update upon download.
How to Remove Spyware: 10 Steps (with Pictures)

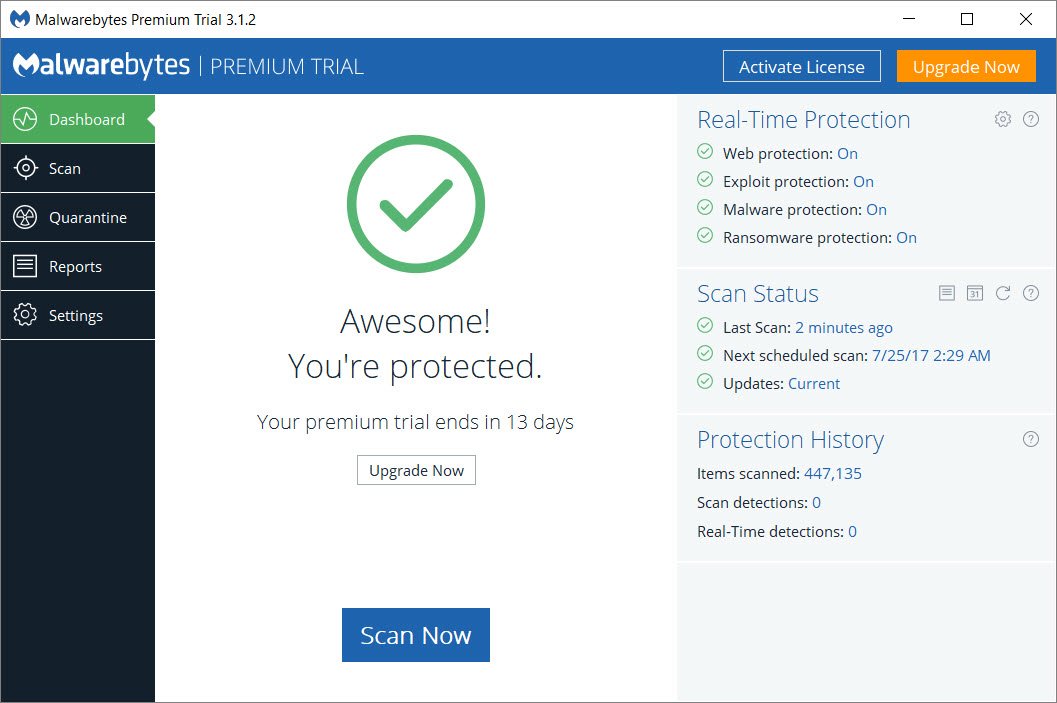
The adware will display advertisements for the same or related products or services to entice you to click or make a purchase. This allows the attackers to gain access to your as well as any passwords, usernames, bank account information, and more. You need to run these 4 essential steps to remove all the spyware on your computer. Click here: Anatova is the nickname given to a new brand of sophisticated that looks to encrypt your personal or business files and then demands payment to decipher them. If automatic updates are available, configure your antivirus to use them. Note: Since spyware scanners have become so popular, the spywareproducers themselves have gotten into the business of producingtheir own spyware scanners. Please press the Yes button to allow the program to download and install the latest updates so that it can properly detect and remove the latest malware.
McAfee Virus Removal Service
Follow this step-by-step guide for instructions on how to get rid of malware. These documents attempt to convince the victim to enable macros in them by saying that the content cannot be viewed until macros are enabled. While in most cases the file is safe, it is not digitally signed, which provides malware authors great opportunities for system exploitation. They claimed that, after converting videos, they noticed multiple ads, pop-ups, banners, deals, offers, and similar commercial content was interrupting their daily browsing sessions using Google Chrome, Internet Explorer, Mozilla Firefox, Safari or another browser. This means that it was designed to have new features added to it at any time. It fully encrypts files that are less than 1 Megabyte, and encrypts only a single Megabyte of files larger than that. Such information might be collected by third-parties should reach someone you cannot trust, besides, the collected data is typically used to deliver targeted advertisements, and it also means that it can be used to serve deceptive, but luring content for you.
What is Malware? How Malware Works & How to Remove It
A campaign from Emotet over the Christmas season read like a friend sending a friendly season greeting. Run a complete scan with free curing utility … Dr. If prompted, allow the scanner to as appropriate. Look for cybersecurity that includes real-time protection. How do you remove malware? How it works Hancitor uses a new template that attempts to fool the user into believing that it is a FedEx tracking number. It encrypts most of its internal strings, cleans its own data out of memory, causes bugs in common analysis programs, and stops execution if it detects that it is in a virtual or test environment.
How to Remove Spyware: 10 Steps (with Pictures)

In the email mentioned above the target may be fooled into thinking that the attached greeting card is legitimate. Before we continue it is important to understand the generic malware terms that you will be reading about. Even worse, in most cases you will have no indication from this point forward that anything is wrong. Yes, out-of-the-ordinary behavior is sometimes the result of hardware conflicts, but your first action should be to rule out the possibility of infection by a virus, spyware, or other nefarious entity— even if you have an antivirus program installed. All this code does is launch a command shell, which then launches PowerShell, a more powerful version of the Windows command shell. If you want something that can help you break down and pa … y for a virus scanner.
Does spyware doctor just scan or does it also remove virus

The meanings of many of these words have changed over time. System monitors are often disguised as freeware. Just like any program, in order for the program to work, it must be started. Many times these programs are quicker to update their definitions then a standard anti-virus program and also target more adware and unwanted programs. However, some fake versions of web browsers can reach victim's computer when installed alongside illegal software.
Is SuperAntiSpyware a virus? If so, how can I get rid of it?
These fake alerts indicate that something is wrong with your computer and that they locked you out of it until you call a listed phone number. For this reason booting into safe mode allows us to get past that defense in most cases. If automatic updates are available, configure your antivirus to use them. The majority of Anatova detections have been in the United States, although infections have been seen across Europe as well. The list below includes both free and commercial anti-virus programs, but even the commercial ones typically have a trial period in which you can scan and clean your computer before you have to pay for it.
Malware, Spyware, Virus, Worm, etc… What’s the Difference?

Be proactive by changing your passwords and notifying your bank to watch for fraudulent activity. Some spyware is known to block websitesthey dislike, websites for antivirus companies and spyware removalsoftware are the usual targets. The upside is that you should be able to use your computer again without paying. Right-click on any of them and select Go to file location. Once Quick Access Menu shows up, select Control Panel and Uninstall a Program.
SUPERAntiSpyware FAQ

BonziBuddy is a well known spyware which was installed this way. If this works, you can save up on lots of energy. Only this time, the potential victims are receiving the message from a trusted email. Some traditional cybersecurity or antivirus products rely heavily on signature-based technology—these products can be easily circumvented, especially by new threats. To do that right click on the entry and select delete. The most common of these are malicious emails but many more exist and are discovered all the time.