Dns switcher android. Android Switcher Trojan targets routers changing DNS settingsSecurity Affairs 2019-04-22
[GUIDE] How to Change DNS in Android Device (8 methods)
. Switcher malware The security researchers have identified two versions of Switcher malware. It offers privacy and better performance over other apps. Works without root and for both WiFi and mobile network data connections. In addition, you will find them in the message confirming the subscription to the newsletter.
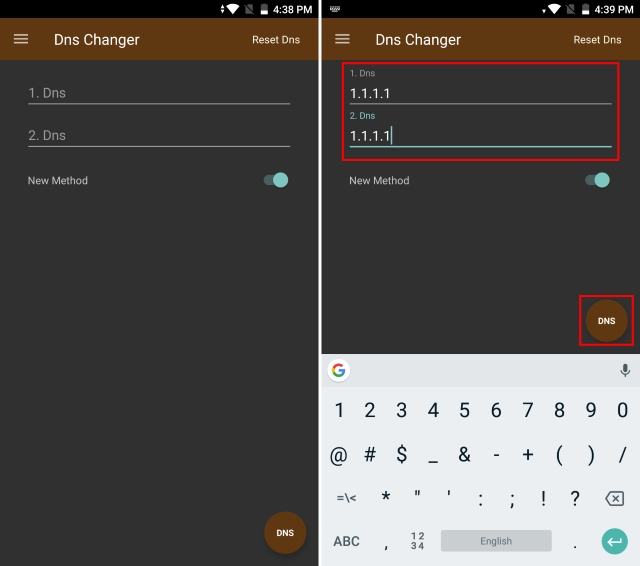
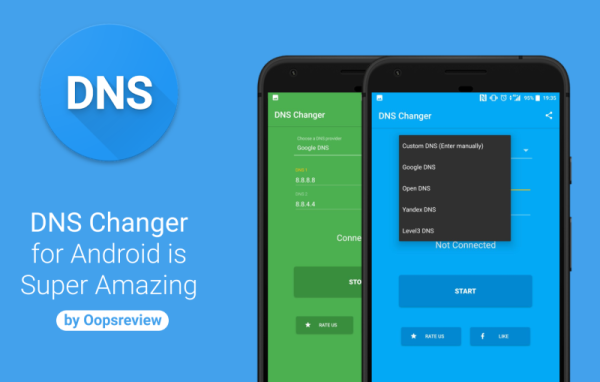
DNS Switch for Android

The app is open source and completely safe. That number is likely to climb. Downloading the Utility Once you are ready to begin, you will need to download the. I also use some regional apps. Very Well Explained and Great Design on Web. This top Productivity app is just 2. With the help of JavaScript it tries to login using different combinations of logins and passwords.
'Switcher' Android Trojan hits routers, hijacks DNS
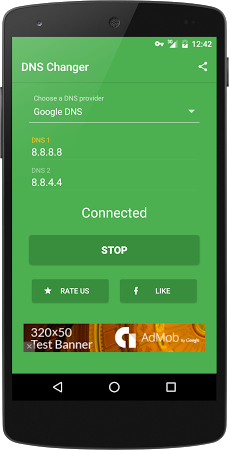
You can find more interesting apps at 9Apps! Nothing wrong in trying 1. By the end of last year, there were 1,280 reported infected networks. Instead of attacking the user, Switcher targets Wi-Fi network of the connected user or the Wi-Fi router of the network. When you type — www. Once your two servers are selected, Dns Changer will notify you of a successful connection.
DNS Jumper: easy DNS switcher with IPv6 support
I have tried the mod on Bluestacks and it works really good. Looking for the latest Clash of Clans Private Servers? You can quickly upgrade your troop levels and attack other players and do a lot more. From there, almost any kind of attack is possible on other devices or systems connected to that network. Often what seems simple is unfortunately hard to follow for many. I know the feeling and this is where the updated private servers come handy.
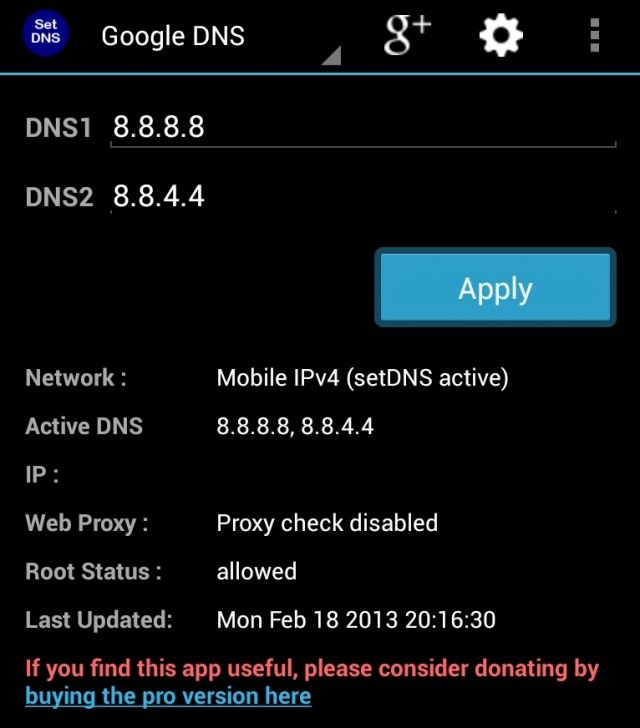
How to Change DNS Settings on Android
Netguard Netguard is popular name when it comes to. Another day, another creepy malware for Android users! Switcher, by the researchers at the Kaspersky Lab. Once in place on a user's Android device, Switcher checks for the local wireless network's basic service set identifier -- the of the local network's access point -- and reports it to the Trojan's before going to work on brute-forcing, and reconfiguring, the router. January 29, 2017 at 1:02 am No prob bud. You need to earn gold, elixir and also gems to upgrade your stuff. Clash of Phoenix The Clash of Phoenix is another great server which is regularly updated.
DNS Jumper: easy DNS switcher with IPv6 support
The other network traffic will not be impacted. Luckily, with a freeware utility and some know-how, you can make it as easy as double-clicking on a shortcut. When victims install the malicious app, the Trojan attempts to guess the login credentials of the Wi-Fi router. Short Bytes: A dangerous Android malware named Trojan. You can also get the upcoming Town Hall 12 in the private servers.
New Android Malware Hijacks Router DNS from Smartphone
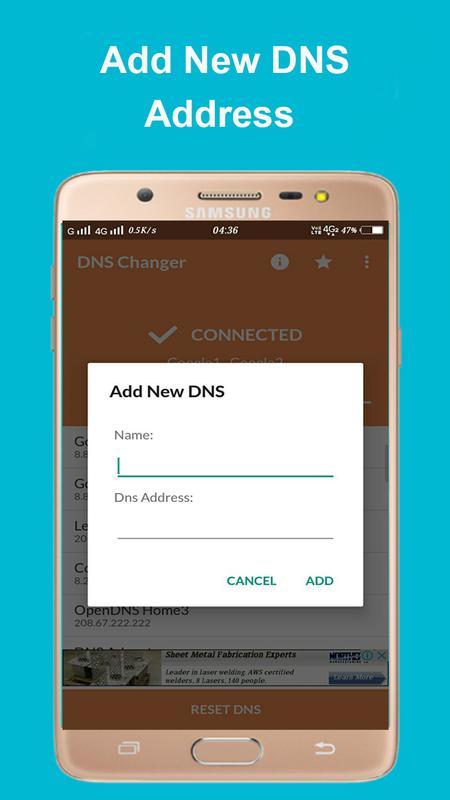
Now go back to browsing the net and have fun! The cyber criminals have even created a website that distributes and advertises these fake apps. Open the app and go to Settings, Advanced Options. One such new Android malware, dubbed Trojan. App is included in Family Library. You can upgrade your buildings, defenses and troops without having to wait hours or even days.
How to Create a Shortcut to Change your DNS Server in Windows

However, there is one problem with the above method. But this is so easy. Let me know your thoughts in the comments below. The Switcher Trojan has been disguised as an Android client for the Chinese search engine Baidu, and a Chinese app for sharing Wi-Fi network details. In fact, I started playing the game on 2014 when I was little kid. You will notice Advanced options there. Meaning the following app works only for Wi-Fi connections.
Android Switcher Trojan targets routers changing DNS settingsSecurity Affairs
Ive tryed So many thing to stay connected. There are several free domain name resolution services that you can switch to. You can easily install the Clash of Phoenix mod on your iPhone. Downloads These are the files for Android users. Long press the Network you're connected to, and tap ' Modify Network'. The app works with Tasker right out of the box.
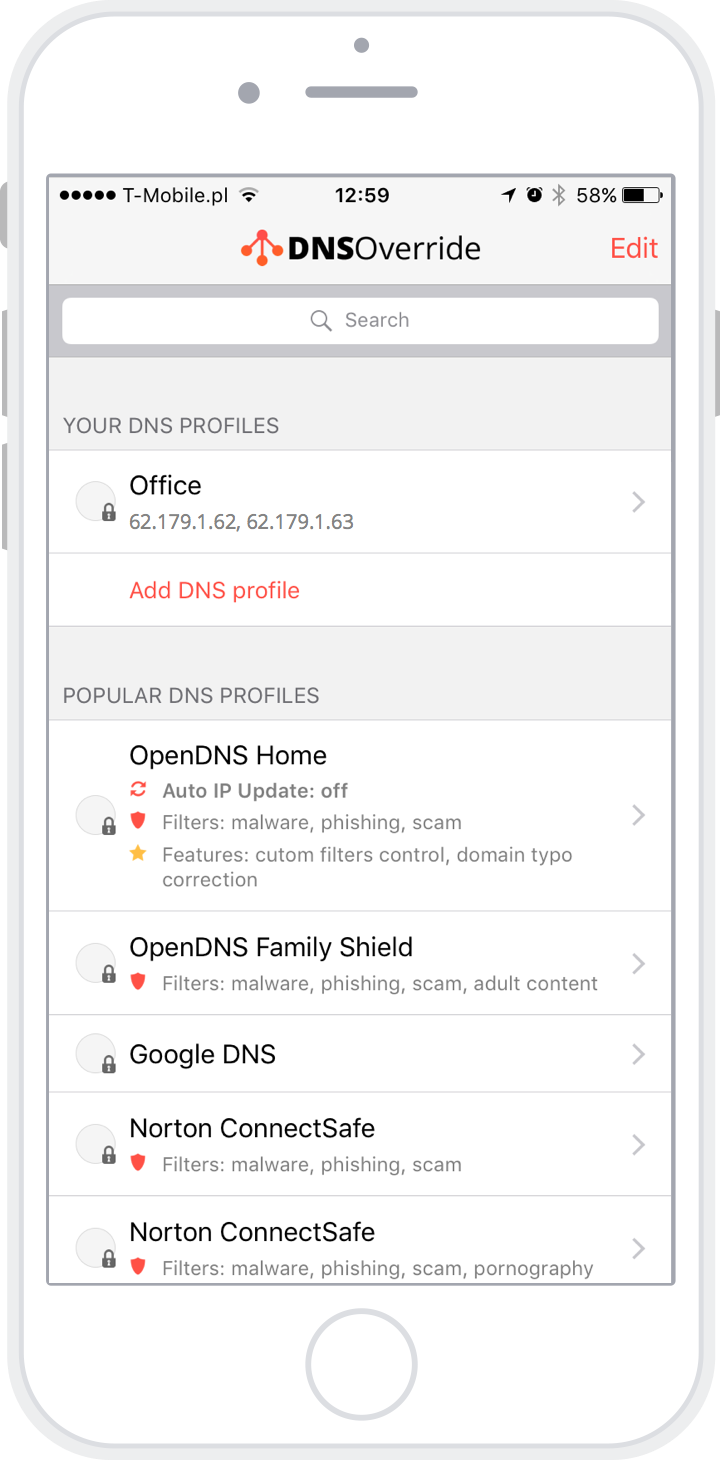
'Switcher' Android Trojan targets routers with rogue DNS servers
In fact, the new Town Hall 12 update is live on the mod. The working of this malware makes it pretty unique. Simplistic, straight forward and easy to use interface. How to join these private servers? The app is free to use and available on Github which you will have to sideload if you are not using it already. Once victim installs one of these malicious apps, the Switcher malware attempts to log in to the WiFi router the victim's Android device is connected to by carrying out a brute-force attack on the router's admin web interface with a set of a predefined dictionary list of usernames and passwords. The other network traffic will not be impacted. The Threatpost editorial team does not participate in the writing or editing of Sponsored Content.