Disable cyberghost update. What the Hell is CyberGhost Up To? Updated 2019-01-11
What the Hell is CyberGhost Up To? Updated
Why they want permission to identity files on phone when installing, no answer? Conclusion CyberGhost may not be doing anything major wrong other than lying about keeping logs. Its behavior, however, appears to be shady in the extreme. . I have just purchased a plan for another year. Surely, there are more around, but unfortunately so far I had no chance to test them currently. And that may, indeed, be all CyberGhost is using it for.
What the Hell is CyberGhost Up To? Updated

What is a root certificate? I have also asked this from Cyberghost. I am not happy about the stuff mentioned in this article which I wrote, after all! CyberGhost promises to keep no logs at all, but we just have to trust its word about this see later. If you look carefully when you are installing you see how it flashes on screen and it can be found from mmc. But it is worth checking, and manually if necessary. As it is a hash it's not possible to reverse identify a users computer.
What the Hell is CyberGhost Up To? Updated
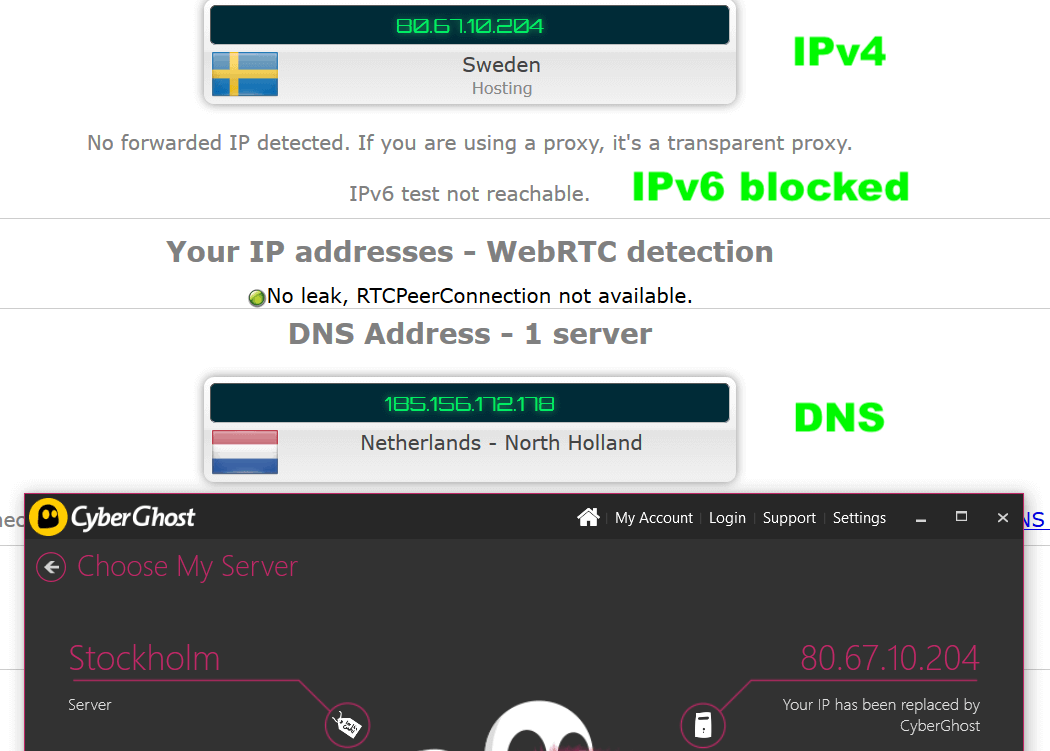
A member of last moths posted evidence that CyberGhost is logging the of computers that have its software installed. But when i installed it on older Android 4. The service is particularly notable for its rather good free option. On new Android phone you can´t see what is happening. It claims these logs are hashed, but we have only its word for this. The decision to do this in the first place, however, remains questionable. The reason for its installation appears innocuous enough — to enable advanced Internet Protection features.
What the Hell is CyberGhost Up To? Updated

Of particular concern is the root certificate. Furthermore, even when hashed, this data constitutes a unique fingerprint of each users' hardware. I find their server performance quit well. But the fact that CyberGhost installs a root certificate on your system means that it has access to much more sensitive information than is usually the case. So you cant go over your computer limit and so forth. Logs for which can then be immediately discarded by a provider offering a true no-logs service.
What the Hell is CyberGhost Up To? Updated

On my computer Cyberghost still installs that Root Certificate, on version 6? In Windows you can check which root certificates are installed using the Microsoft Management Console If a browser is presented with a valid certificate then it will assume a website is genuine. Then please see my new. See Fiddler for more details. Thanks to a series of criticisms from us including this article CyberGhost has worked hard to meet the high standards we require before we can recommend a service. Being a root certificate, however, means that you must place a huge amount of trust in CyberGhost to not abuse its power to spy on everything you do on the internet. .
What the Hell is CyberGhost Up To? Updated

. . . . . . .
What the Hell is CyberGhost Up To? Updated
. . . . . . .
What the Hell is CyberGhost Up To? Updated
. . . . . . .