Difference between udp and tcp in java. sockets 2019-01-25
Comparison Between TCP and UDP Protocol
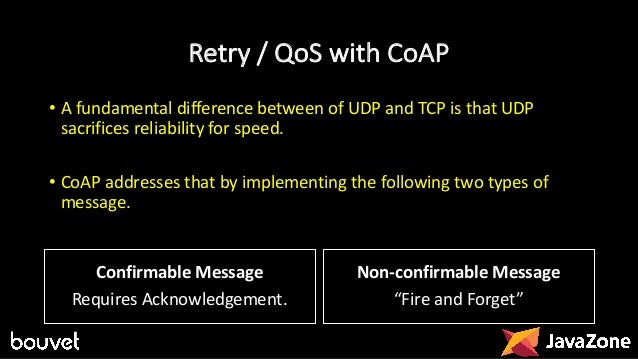
There may be multiple packets per read call. Therefore, it can be accessed that most websites prefer transmission control protocol, but most applications and games prefer user datagram protocol. A datagram package may be lost in transits. Losing all this overhead means the devices can communicate more quickly. The protocol supports error detection via checksum but when an error is detected, the packet is discarded. Datagram packets may arrive in any order.
DiffTech: Differences between tcp and udp

Read the Wikipedia thoroughly, it will probably answer the questions you'll have after reading this answer. Streaming of data: Data is read as a byte stream, thus no distinguishing indications are transmitted to the signal message Packets are sent individually and after the arrival the packets are rearranged Weight: It is heavier as it requires three packets to set up a socket connection, before any user data can be sent. It depends entirely on the intervening network. Recovery from the error would be pointless because by the time the retransmitted packet is received, it won't be of any use. The connection is established by sending handshaking messages before sending actual data.
networking
Whenever the message is passed from a source to sender, it must pass from each layer of the protocol stack. As it fails to guarantee data arrival it cannot be termed as a reliable communication mode. It makes sure that the data sent from source computer are received accurately by the destination computer. The header contains 10 fields that must exist and an optional extension field. It needs three packets for handshaking or to connect before sending data packets. There is no ordering of messages, no tracking connections, etc.
Difference between TCP and UDP
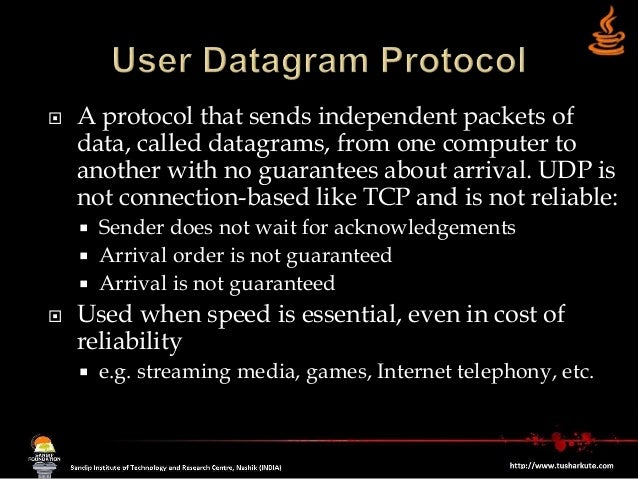
One more reason, why Java developer should understand these two protocols in detail is that Java is extensively used to write multi-threaded, concurrent and scalable servers. Because if the data is missing or out of order then it would not be beneficial to you. It ensures data reliability and takes action if any glitches occur during congestion. The correct term here is not 'compatible' but supports. Handshake is not required as connections are not present in this protocol.
Difference between TCP and UDP
Protocols define the rules, conventions and data structures that govern the data communication. Thanks a lot creator s of this. You then proceed to speak and once done you hang up the connection. So the total size of the packet will be 28 Bytes plus the size of the payload. This uses a DatagramSocket on the server side and a MulticastSocket on the client side. So after receiving all disordered packets, it is not possible to order them.
sockets

How they differ from each other is explained in the lines that will follow. If it gets lost along the way, the server will re-request the lost part. This means complete integrity, things don't get corrupted. They have their pros and cons as well. Computers that are interacting with each other may differ in various attributes like hardware, software, specifications etc. Function As a message makes its way across the from one computer to another. Writing fix engines and server side components for high-speed electronic trading platforms needs capable developers with a solid understanding of fundamentals including data structure, algorithms, and networking.
Comparison Between TCP and UDP Protocol

It offers error control and flow control facilities. There is no single answer to that. There are no virtual circuits. Again, latency and ordering are the two biggest concerns. We can simply say that it is a language that computers use to talk to each other. Packets have definite boundaries which are honored upon receipt, meaning a read operation at the receiver socket will yield an entire message as it was originally sent.
9 Difference between TCP and UDP Protocol
Handshake — No handshake connectionless protocol 9. This is because there is no overhead for opening a connection, maintaining a connection, and terminating a connection. These two terms are two different ways of transmitting this data. All these features make it the most common protocol available. It is more often used by applications and games which require that the data is sent quickly and in bulks. It doesn't, however, define how client and server are identified and how client specifies which server it wants to talk to.