Crack xlsx password kali. PDFCrack 2019-03-03
Cracking Microsoft Office (97

From the command prompt navigate to where you have OclHashcat actually CudaHashcat for me. Hacking a password protected zip file can be done with many password cracker utilities available online. The wordlist should not contain duplicate lines. Leave me a comment if it does. If the password is successfully cracked, you will find it in the output file specified and in the cudaHashcat.
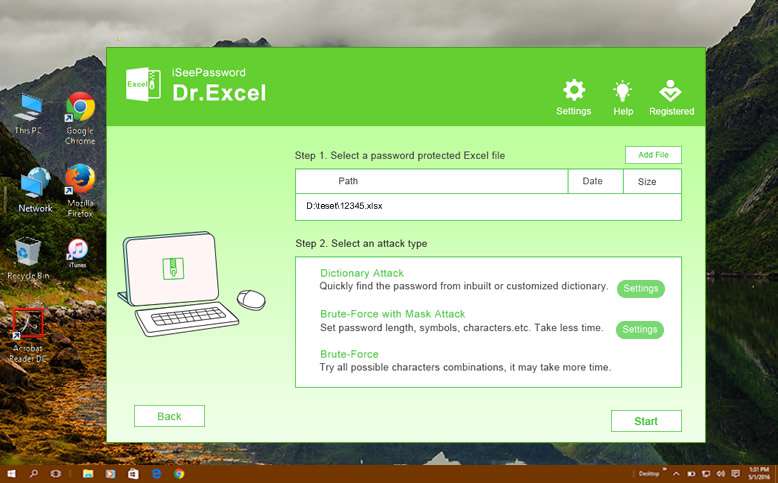
.xlsx password protected excell 2013... password crack

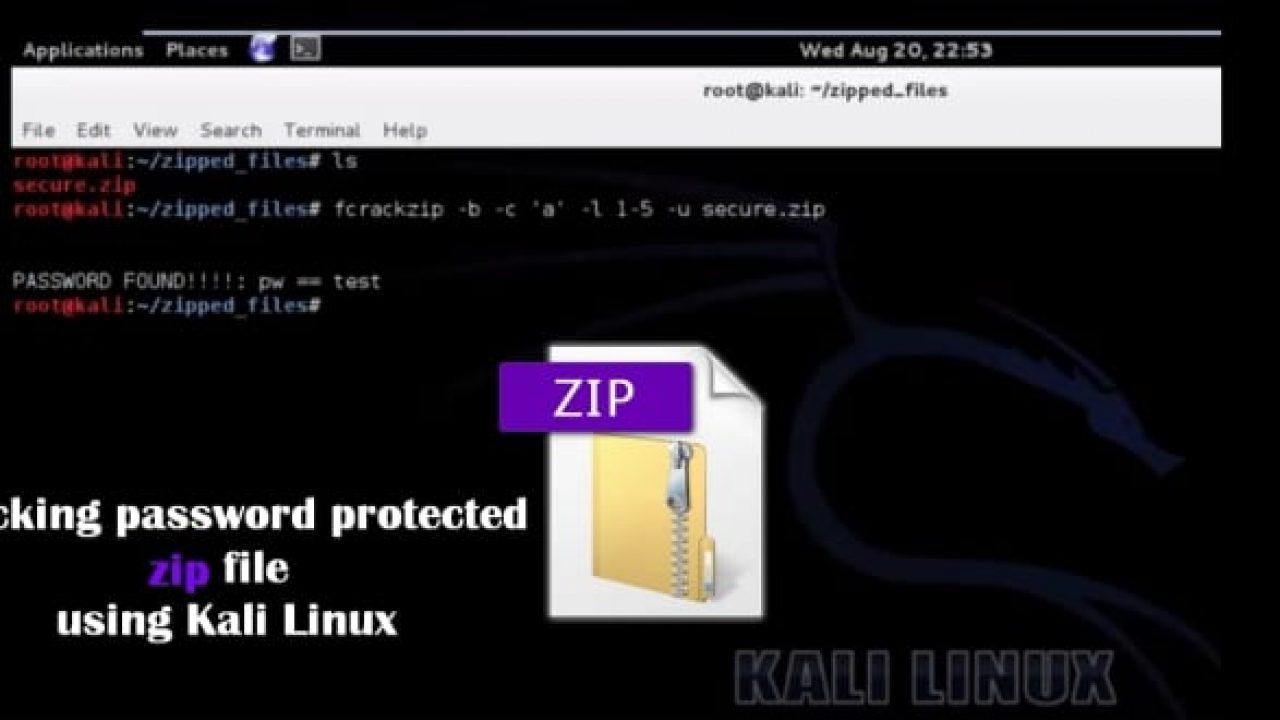
If you have these older encrypted. For the wordlist we shall be using the password list that comes with john on kali linux. Total cracking time will be almost the same, but you will get some passwords cracked earlier, which is useful, for example, for penetration testing and demonstrations to management. There are were a lot of commercial programs available in the past that could do the trick, nevertheless they are only able to resort to brute-force attacks. However, if you are a Kali Linux user, password cracking becomes that much more easy with an open source tool called fcrackzip. Step 2 — Now Navigate To The Directory where windows password files are Stored.
.xlsx password protected excell 2013... password crack

Any one experience a locked xlsx document, I'm looking for ways to crack this password protected file. See here: The below is a link to a free tool. For illustration purposes, I have created a Word 2007 document example. Previously you had to rely on a flaw in the document, some sketchy software or an even sketchier website. Important note: This is not a guide on how to install and use hashcat in general. There are 6 different flag codes implemented for the 97-03 hashes depicting different implementations of the hash and one implementation for each of the other versions of Office, as shown below.
How to crack password protection on Excel Spreadsheets « Null Byte :: WonderHowTo
In some cases it is faster to use some other pre-defined incremental mode parameters and only crack simpler passwords, from a limited character set. Just as long as it has the same hash. By default, Windows will hide file extensions for known file types. John the Ripper is accessible for several different platforms which empower you to utilize a similar cracker everywhere. Successfully guessed passwords are also tried against all loaded password hashes just in case more users have the same password. Fcrackzip is a fast password cracker partly written in assembler and available for Kali Linux. The default may vary depending on the version and build of JtR.
break stuff majorly: Cracking Microsoft Office File Passwords

You can get all the possible options by typing To list all the possible formats To list all the possible subformats To bruteforce the It will take some time to get the password cracked. As long as the wordlist is sorted alphabetically, John is smart enough to handle this special case right. John uses character frequency tables to try plaintexts containing more frequently used characters first. As the number of such potential passwords is fairly low, it makes sense to code a new external cracking mode that tries them all, up to some length. John is in the top 10 security tools in Kali linux. If it were not there then john would have failed. It tries both dictionary and brute force attacks.
*New* John the Ripper
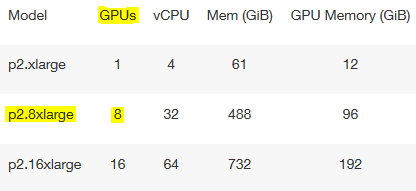
A simple google can help you discover more. There are also online services that do this, and they obviously use cloud resources to increase compute power. So sad to loss this data. I was asked if this password could be cracked. You'll of course also need John installed google it and will need a target Office file. You can get it from github here: Or, you can download a copy I put here: Depending on your cracking strategy, you will likely also need a dictionary file for the attack. After you edit the file, save it, close Notepad, and then try reopening it and see if it still has your modifications before you re-compress the zip.
Cracking linux password with john the ripper
But how to do that? In fact, it is recommended that you do not truncate candidate passwords in your wordlist file since the rest of the characters beyond the length limit of your target hash type are likely still needed and make a difference if you enable word mangling rules. Some of these utilities may be obtained here: 2. If enabled, all of the rules will be applied to every line in the wordlist file producing multiple candidate passwords from each source word. This works for both interrupted and running sessions. The return code is the number of valid passwords found, 0 if none was found. Long story short john the ripper another password cracking suite is also capable of doing this, but I prefer OclHashcat.
Cracking Microsoft Office (97
If running John on a Unix-like system, you can simply disconnect from the server, close your xterm, etc. Some of the noteworthy attempts are: 1. Select the files as required. Include a or use the website to generate the reddit table markup from your spreadsheet. The process is simple but not as straight forward as a novice might want. It can also perform a variety of alterations to the dictionary words and try these.
How to crack password protection on Excel Spreadsheets « Null Byte :: WonderHowTo
In this example we are going to use the default password list provided with which is another password cracking tool. On Kali Linux, it is per-installed. I will create a new user on my linux system named happy, with password chess. There are a lot of other guides available on this topic, an example would be. It will open the terminal console, as shown in the following screenshot. I'm doing this from Kali 2.