Crack windows password hash. I can get and crack your password hashes from email 2019-04-09
The 'Cracken': The Evolution of Password Cracking
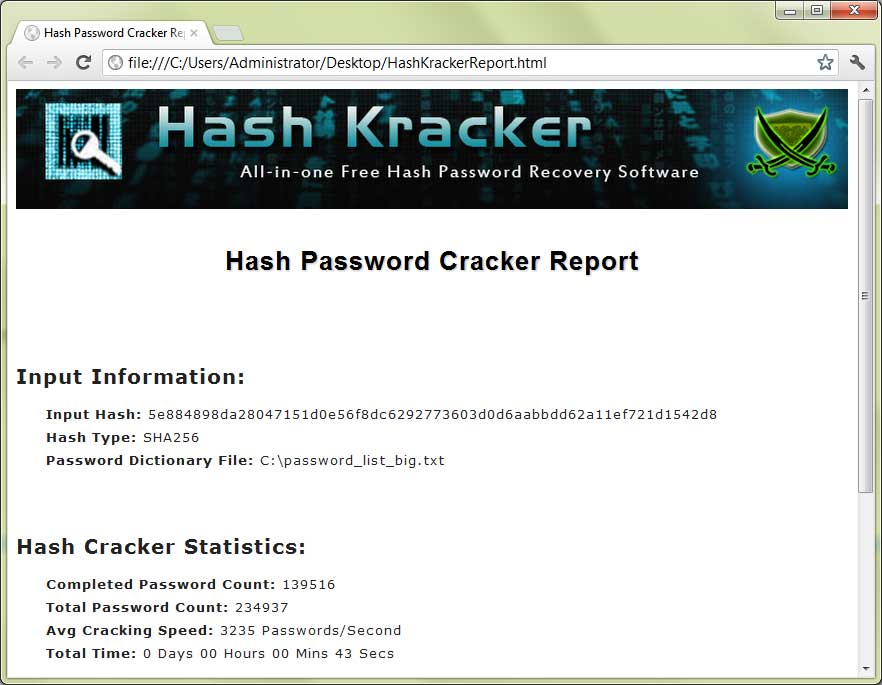
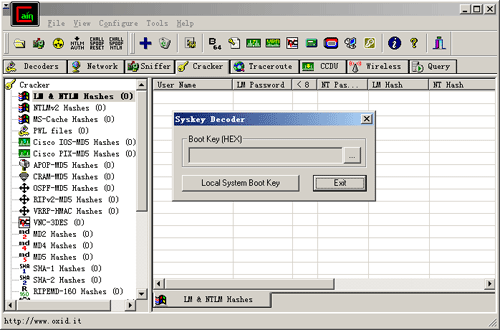
Its ability to autodetect password hashtypes, makes it a preferred choice of ethical hackers to ensure security. . Like any other tool its use either good or bad, depends upon the user who uses it. Cracking Passwords Using Cain and Abel Now that we actually have password hashes we can try to crack them. With this type of hash cracking, all intermediate computation results are discarded.
RainbowCrack
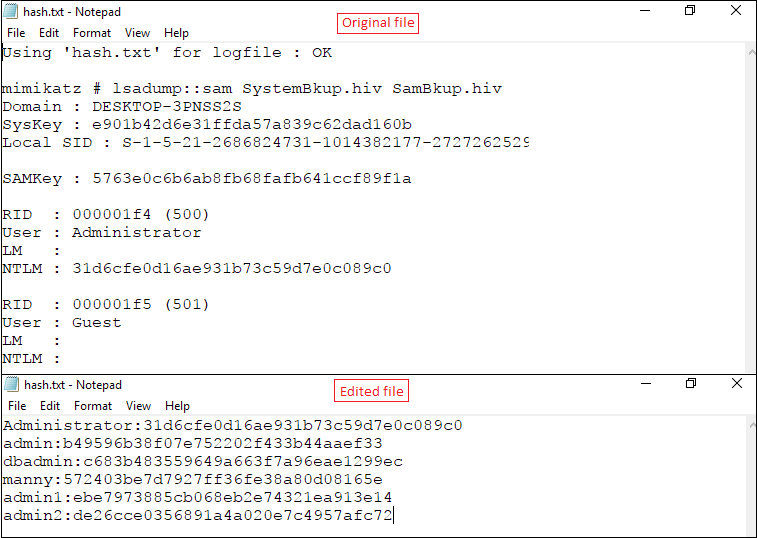
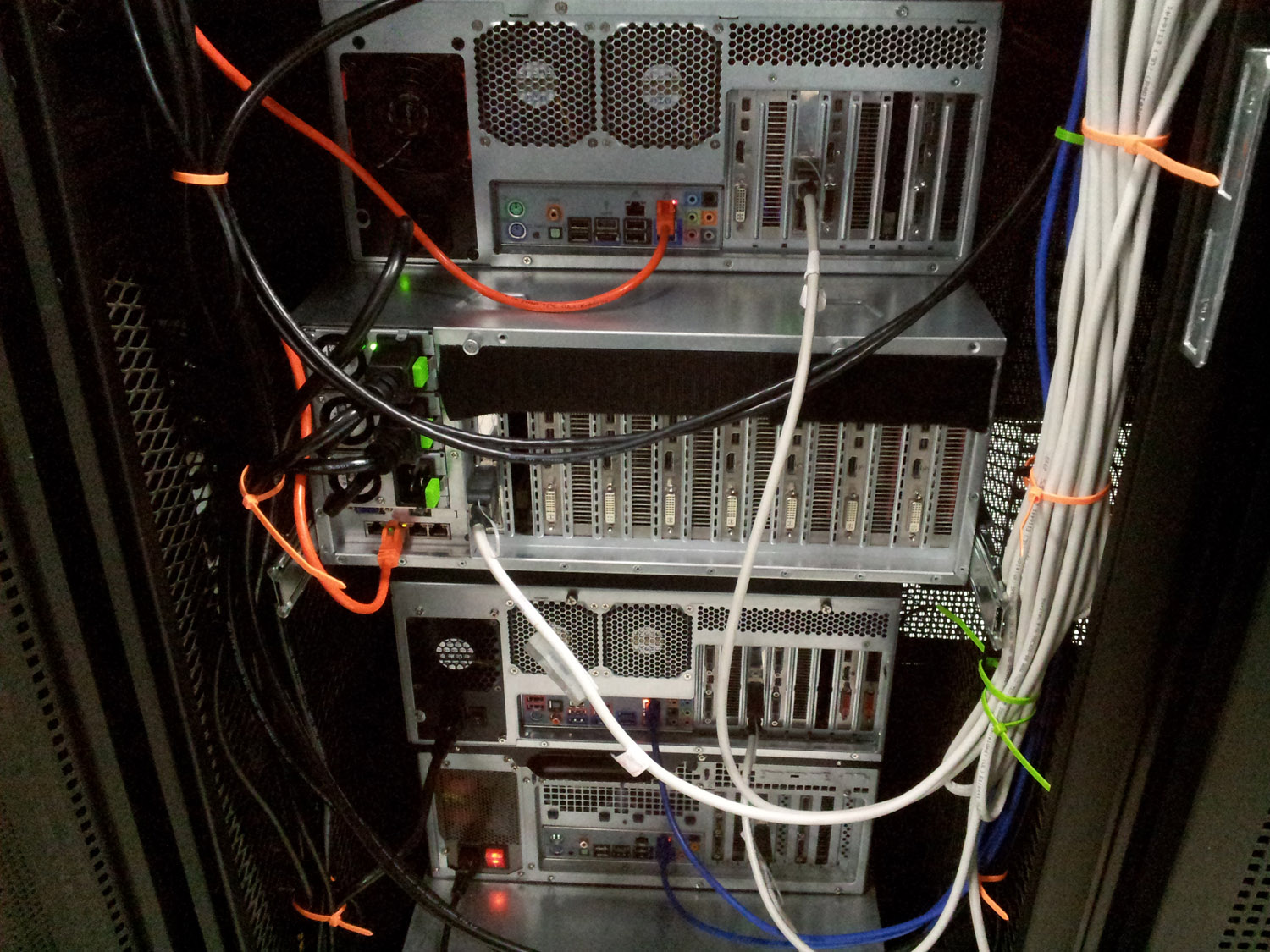
Run ophcrack and set the number of threads under the Preferences tab to the number of cores of the computer running ophcrack plus one. This tool also lets you add new modules to increase the functionality. Of course, this will only work if the client is authenticating to a or accessing resources on another client, otherwise, you are more out of luck than a one armed man in a paper hanging contest. The future of authentication and password security is being assessed by a lot of brilliant minds. It can be enabled by running the syskey program. Figure 3: Password Hashes Output by Fgdump Network Access Finally, if you do not have any interactive access to the machine that has the hashes you want, your best bet is to attempt to sniff the hashes as they travel across the network during the authentication process.
Rainbow Tables: Your Password's Worst Nightmare

So many people have set passwords for their computer. Capturing a Screen Image Make sure the last several hashes are is visible, including 97, 98, and 99, as shown above. It needs to be done this way to allow you to log in to your computer, even if you are not connected to the internet. When a user visits this web page the script is downloaded to his browser and executed. While these attacks are still possible over network, but executing them is not a cup of tea of someone who has learnt hacking from Hacker in a Week type videos.
6 Ways to Crack Windows XP Administrator Password Successfully
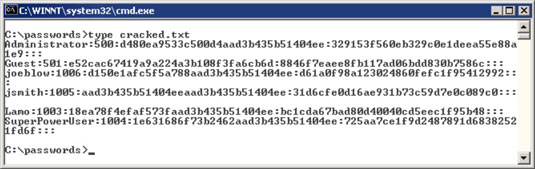
You can use either the inbuilt encryption if you have Pro version of Windows or use any of the programs. Method 3: Through Safe Mode Restart the system press F8 key to boot in safe mode from there log in Administrator Account without password. Complex passwords can often taken some time via this method, but it is typically quicker than allowing your own hardware to do the work. Send in the correct passwords to collect credit. The output will be in hex format, but it works with a simple conversion. If you reused your same password on both the third-party site and your enterprise account the attacker has now gained access to your organization.
Hash Crack v3
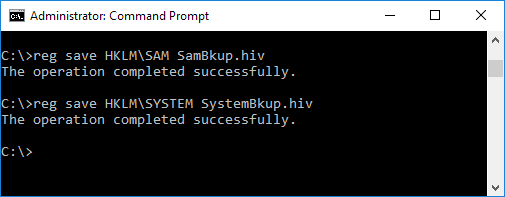
Since these are one way hash algorithms we cannot directly decrypt the hash to get back the original password. There are a lot of different reasons why one would want to hack a Windows password. Using a large-scale time-memory trade-off, RainbowCrack performs an advance cracking time computation. Use Complex and Changing Passwords The most logical way to prevent people from cracking your password is to make it incredibly complex. But What if we just forget the passwords? A brute force hash cracker generate all possible plaintexts and compute the corresponding hashes on the fly, then compare the hashes with the hash to be cracked. It takes us about 12 hours to brute-force it.
Cracking Windows 10 Password: Methods and Prevention

Saving a Screen Image Make sure the Terminal window is visible, showing the found passwords. The use of Rainbow Tables allow for passwords to be cracked in a very short amount of time compared with brute-force methods, however, the trade-off is that it takes a lot of storage sometimes to hold the Rainbow Tables themselves, Storage these days is plentiful and cheap so this trade-off isn't as big a deal as it was a decade ago when terabyte drives weren't something that you could pick up at the local Best Buy. To complete this challenge, email in the correct passwords for all three accounts. Physical Access If you have physical access, one of the most effective methods is to boot the computer into a different operating system. You can monitor the queue status by going to the Search link and searching for the hash, which will tell you its queue position. It's been over a year since Hash Crack v2 came out and a refresh with some additions were needed.
10 Best Password Cracking Tools Of 2016
If you would like to read the first part in this article series please go to. So today i am sharing some some google tricks for using google search more efficently. And it's only a matter of time before more come out to start breaking Windows 10 passwords. That's why it's advisable to remove any unnecessary user account with the Delete button. Targeted Wordlist company name, addresses, employee names, etc. Cain will not accept a simple copy and paste of the password hash, so you will have to place the hash in a text file formatted a special way.
10 Best Password Cracking Tools Of 2016
Go in, inject the password of your choosing. In the past these tables were far too processor and storage space intensive to create and store, but with the advances of modern computing its becoming more and more common for both ethical penetration testers and malicious hackers to keep external hard drives containing sets of rainbow tables. It's a great way to target Windows desktops, networked servers, Active Directory, and primary domain controllers. All you need is a penetration testing tool and roughly five minutes. You can login to your Windows account after restarting. Sometimes, they required numbers or even — gasp — special characters for their passwords.
Hash Crack v3

Press the PrntScrn key to capture the whole desktop. It's widely used to crack Windows log-in passwords. RainbowCrack After you type new password, and possibly file will be updated. Send in the correct passwords to collect credit. Which means brute forcing a hash will not yield the original password back.