Crack password hash python. Python Script to crack Unix Hash 2019-01-18
Cracking Cisco ‘Type 5’ Passwords

One of the more primitive measures taken was simple password hashing. Since I had root on the server, I was able to connect to the database and explore the tables, but found nothing related to passwords or salts. Nice secure door, but weak walls. According to the docs, StrongPasswordEncryptor is a: Jasypt is also on Github, and I found the source code for both classes and. Next is calling of testPass function. Even if you hate them, I'll still continue Python, I enjoy it.
GitHub

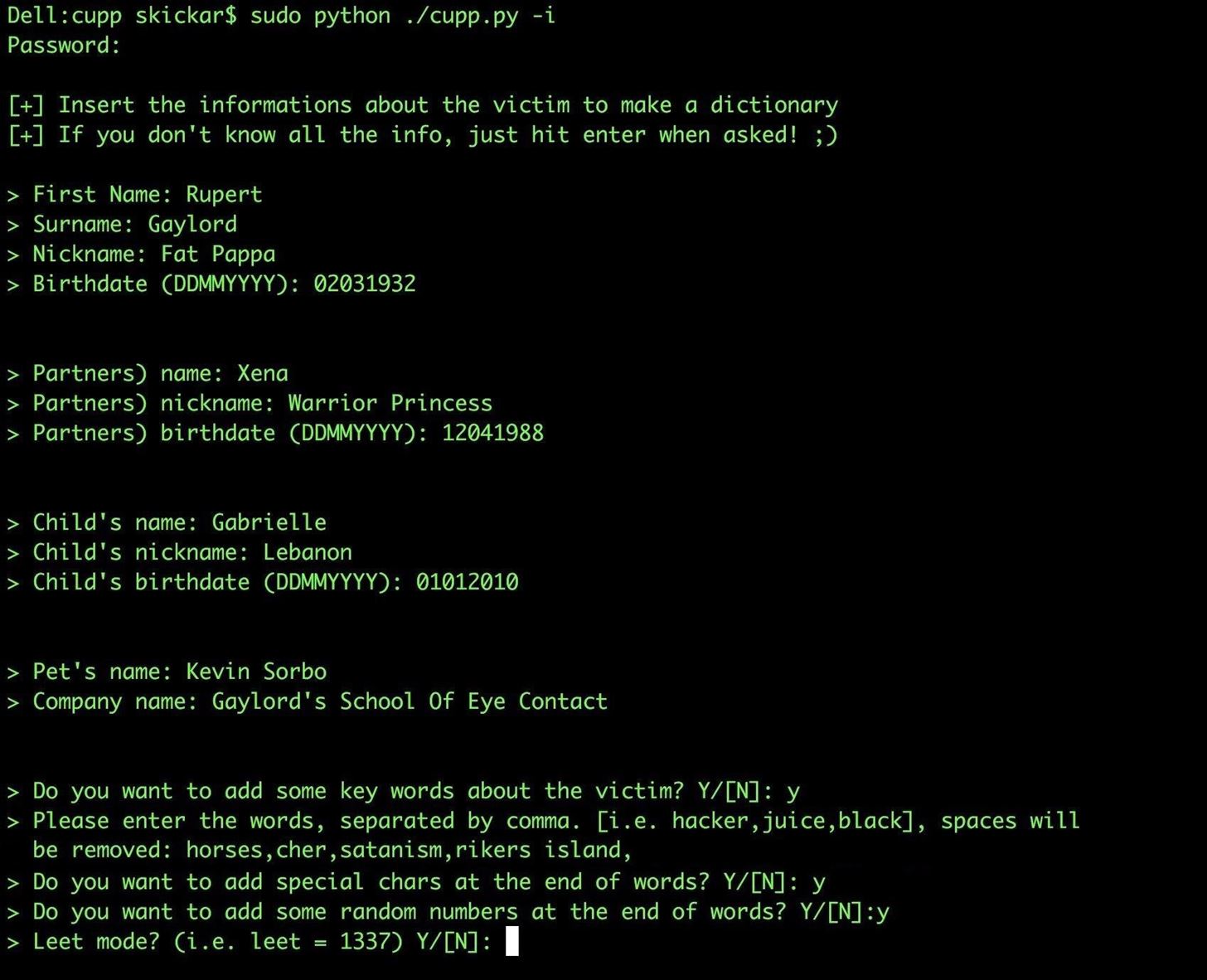
This popular bitcoin wallet website? This process, however, is exceptionally cumbersome, and the results are slow. The file just contains masks, and it might looks like this:? I am in a Distributed Computing class this semester. Additionally, hashcat also can utilize rule files, which greatly increases the effectiveness of the attack. Sources Last revised: 3-4-14 9:50 am. You may have noticed I added the -O flag to the end of the command. From until to this point and all the previous proceedings, it's worth mentioning about this which helped me a lot to reach this point. Try it out yourselves, it'd be great.
authentication

Modify your program to use Unicode, as shown below. The same techniques work for Linux and Mac hashes, but thousands of times slower, because Windows uses especially weak hashes. Running through all of these characters will take some time, but it will recover another password. Mask attacks by themselves are great, but typically when you work with a mask greater than 8 characters, the time it takes to complete the attack becomes an issue. To begin, you can probably understand why it is important to encrypt passwords to begin with. A popular one is darkc0de.
MD5 Password Cracker In Python

If you just saw that hash in a database, you'd have no idea what it meant. Hybrid attacks can use a mask after the word -a 6 , or prior to the word -a 7 , but can not do both at the same time. In the end, this didn't actually help me at all on my pentest as I was low on time and had to pursue other avenues, but it was fun exercise nonetheless. Now, they will have to crack passwords by brute force, the same as before, only now it is one measily password at a time. If your database stores plain-text passwords, at the very least, you are going to see the passwords yourself, and so will anyone who has access to your server. To accomplish this, I download the zip of the repository, extracted extracted the Passwords folder, and then in a terminal navigated to the Passwords folder.
Password cracker in C++ & Python (MD5, SHA1, SHA256, SHA512) : MrRobot
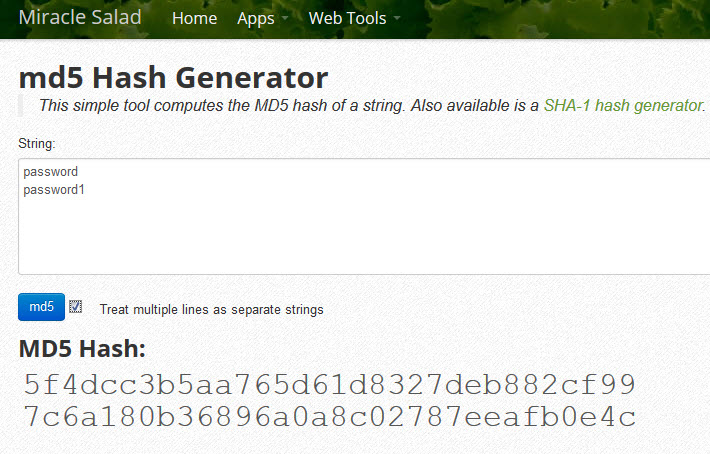
Hashcat supports lots of hash types. That is a very interesting attack you should check out and practice on. I made a hash cracker in Python for purely educational purposes , but it's really slow ~120 seconds for a 4 character string. Putting a string through a hashing algorithm will always result in the same hash output. Pre-Reuisites:You will need only pyhton installed in your operating system. Other people have thought long and hard about all this sort issues so you better take advantage of this.
Password cracker in C++ & Python (MD5, SHA1, SHA256, SHA512) : HowToHack

This time you should get the exact hash shown below: This looks more like a hexadecimal hash, but it's incorrect for Windows passwords. The salt and hashed password are being saved in the database. The resulting string can't be converted back into the original string however, so in order to check that the user entered the right password, the password you enter is hashed and checked against the hash stored server side. For the logo , yeah my bad, thanks for pointing it out. This code is supposed to hash a password with a salt.
SHA
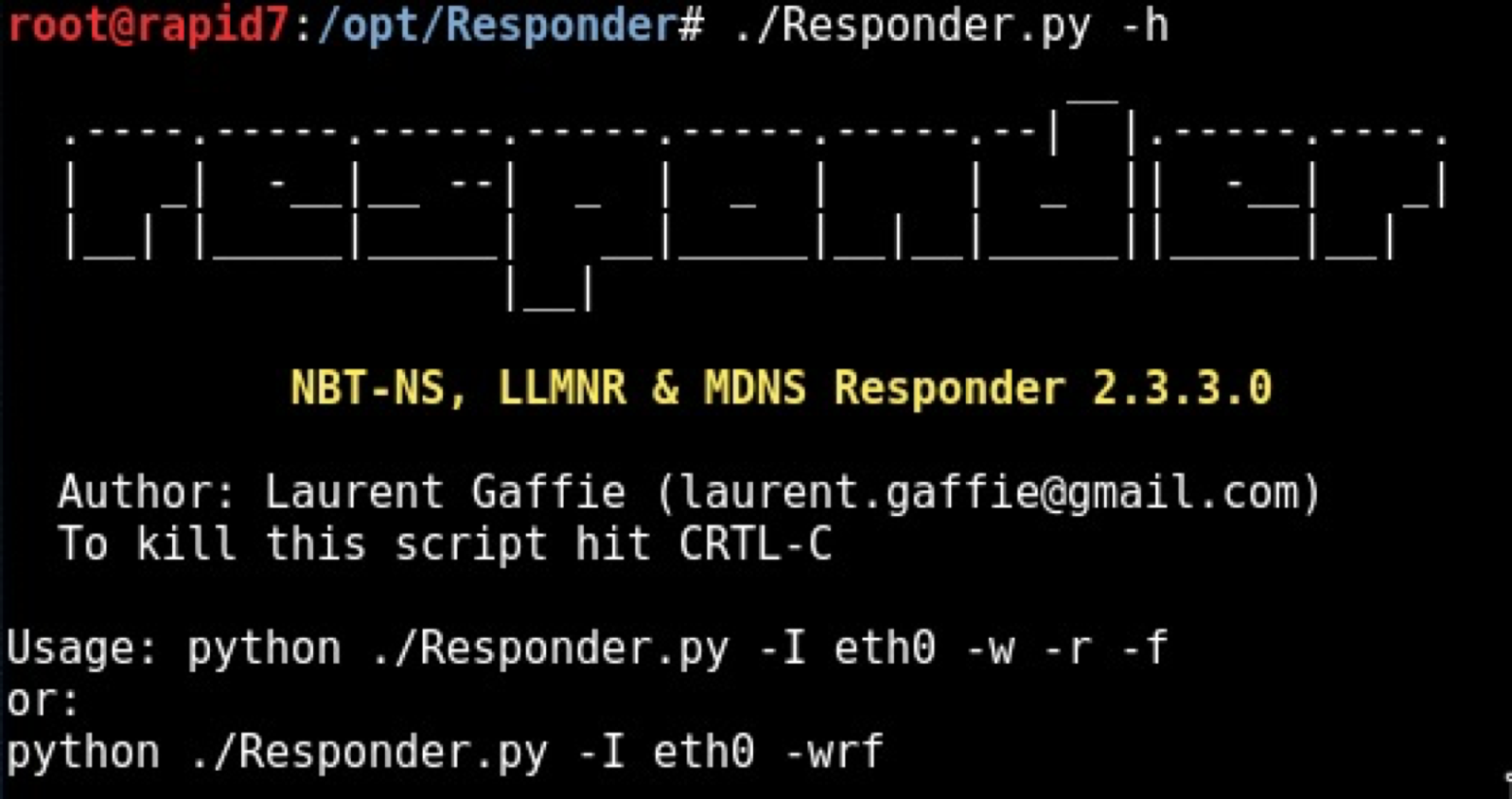
Hashing Algorithm Identification Instead of focusing on the Github code, I turned back to my root shell on the server. Side remark: It seems py-bcrypt is the old pypi package and has since been renamed to bcrypt. I wasn't sure how out of date or how different the code might be between Github and what I was dealing with, so I wanted to try to find the source code on the server where the hash was calculated. This is usually fine, unless you are cracking passwords greater than 27 characters. Writing a cracker Since I still wanted to run some plaintext passwords at the hashes, and I was totally by this whole ordeal, I wrote a simple brute-forcer in Python. Whether it's because they make mistakes or it is because they can be easily social engineered, the people are usually the main target, or at least the reason for the vulnerabilities.
Python Programming Tutorials

Consider the following command: hashcat64. Plaintext Identification Even if I correctly figured out the hashing algorithm used, I still wasn't sure how the salt was implemented, let alone what the salt actually was. So then how might we obscure passwords? I asked on if it was possible to specify number of rounds, but unfortunately found an answer that worked. The program functions by hashing each line from the wordlist, and then comparing it to the hash specified. Somewhere in the Terms of Service, it strongly warns users not to re-use the same password as their Windows password.
Password cracker in C++ & Python (MD5, SHA1, SHA256, SHA512) : HowToHack
What we want instead is a way to generate unique hashes, where their source can be validated easily, but brute forcing will require a brute forcing per password, not a brute forcing for the entire database. However the same might not apply if you pass the string to any external code such as a database. Python doesn't put any restrictions on what you can have in a string. Install it using python-pip if you don't have it already. Here's a simple test case. You can split the salt out again later when you've decoded the salted hash password as you know the decoded hashed password is exactly 32 bytes. You can download a password list.