Conhost.exe process info. orgmode.com process 2019-02-09
What is orgmode.com Windows?

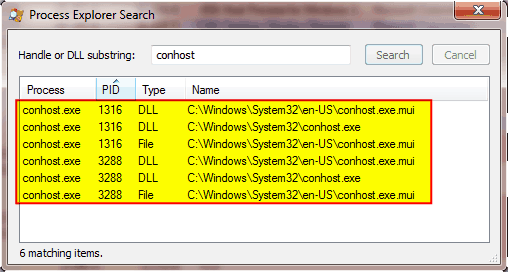
Once you are reduced to the place where you have to uninstall conhost. Distribution Method Spam Emails, Email Attachments, Executable files Detection Tool See If Your System Has Been Affected by conhost. Process Explorer checks all processes, and returns any process, dll, thread or file that is related to conhost. After the reboot click on Enter Safe Mode With Networking Fifth Option. Why Are There Several Instances of the Process Running? Take a look at the following things: Type msconfig in the search field and hit enter: you will be transported to a Pop Up window. Before reading the Windows backup instructions, we highly recommend to back up your data with a cloud backup solution and insure your files against any type of loss, even from the most severe threats. Again, if it is in system32 it should be safe, if it is not, it is probably not.
why is orgmode.com is running after executed a consoleApplication
Browser setting reset guide After you removed the Conhost. When the Control Panel appears, choose Uninstall a Program from the Programs category. The properties of the conhost. By using this program, you can determine which apps are causing problems, and can look into it further. Simply download and run it there is no need to install, its a portable application. Dragging the program or its folder to the recycle bin can be a very bad decision.
orgmode.com: What Is It and Why Is It Running in My Task Manager

Another way to decrypt the files is by using a Network Sniffer to get the encryption key, while files are encrypted on your system. Your computer may get effect with like Now kindly read the complete the article to decide either conhost. Keep in mind, that Combo Cleaner needs to purchased to remove the malware threats. It is recommended to run a scan before purchasing the full version of the software to make sure that the current version of the malware can be detected by SpyHunter. However, if you wish to receive a response, please include your email and name.
Fixed: What is orgmode.com and Why it running on Computer

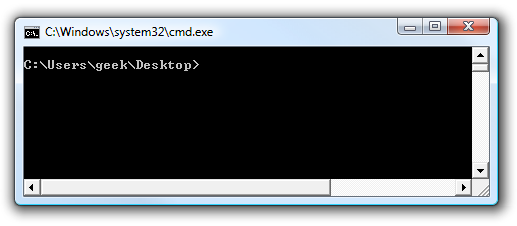
We suggest you for your Windows. If you consider yourself a skilled user, you can try to delete this adware on your own. They backup your personal files and documents and encrypt them, demanding ransom hence the name for releasing them. Follow the instructions above and you will successfully uninstall most programs. I explain what the process is later on in the guide, but you can invoke it by launching a new command prompt window for instance. Hackers employ bots to send out thousands of phishing messages to random or targeted victims.
What is orgmode.com ? orgmode.com info

You are now in the Control Panel. To do this, press the Windows key + R at the same time and then type 'appwiz. If it is not and you are experiencing a slowness of your system, redirects, advertisements and other kinds of anomalies, then you most likely suffer from an adware infection. These parasites are usually concealed inside a legitimately looking file, which is attached to spam emails. It becomes more stable and flexible than it is used to be and you are enabled to use the scrollbars as normal and drag files correctly in Command Prompt as well.
orgmode.com Miner Virus
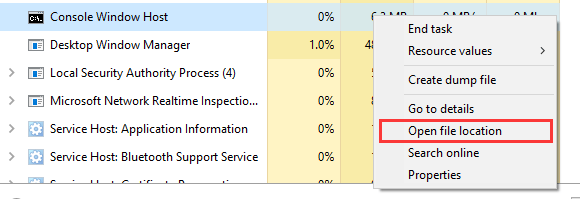
Microsoft does not control these sites and has not tested any software or information found on these sites; Therefore, Microsoft cannot make any representations regarding the quality, safety, or suitability of any software or information found there. Send me an email when anyone response to this Security code: Please enter security code that you see on the above box. The malware may damage the components of your computer due to overheating them if it remains in the long term and since it utilizes over 80% of your central processor at all times, it is advisable to immedately stop conhost. There , find the malware and select Remove. This file is part of Microsoft® Windows® Operating System. In such a case, a significant amount of damage can be done to the system, as additional payloads might be installed during the operation of malware. As soon as it invades to your system, it starts adding malicious entries to your Windows registry and changing your system settings.
What is orgmode.com Windows?
Every time when you run this anti-virus it will start an automatic standard scan of your computer. If you think there is a virus or malware with this product, please submit your feedback at the bottom. Until the Windows 7 operating system, conhost. Is it a legit process? He started out as a network administrator. Typically, the software enters computers as a trojan horse. They will help you get rid of conhost.
orgmode.com Monero Miner Virus
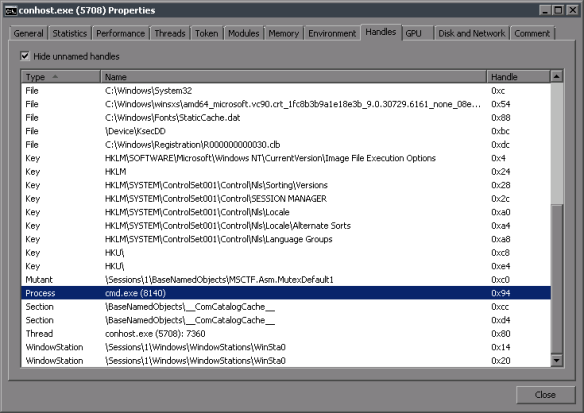
If something goes wrong, you can just revert. Not the answer you're looking for? Normally, in Windows systems, conhost. Also, End the process after you open the folder. You can find this guide higher. In such a case, the original executable of Conhost.
orgmode.com Information

We must remind you when you eliminate adware manually, all the unexpected consequences and risks are lying on you and you alone. If you already know how to do it, just skip this and proceed to Step 2. This objective can be accomplished with a program like which is a powerful tool that was specifically created to take care of different types of dangers, consisting of these ones. We recommend you to read more about it and to download. You may get relax that it is just a process designed for all type of operating system. You can choose any of the three Safe Mode options by pressing its corresponding number and the machine will restart.
orgmode.com process
These three buttons are located on the far left of your keyboard. For that reason, the file was also dubbed Conhost. So I became suspicious and assumed its a virus. This is useful information, as you can quickly check whether conhost. Malware is written in a complicated code and alters several processes of the operating system, including Windows registry.