Cisco router download config. Cisco IOS Router Configuration Commands 2019-04-02
Basic Cisco Router Configuration Step By Step
The Config File Manager tool will fetch both the startup and running config files of the specified cisco device in the background. Step 3: Log into the access point through a Telnet session. Instead, you copy them directly to the router console from a dCloud data center. Step 1: Connect console cable at the console port of the router and the other end to your computer or laptop. For the rcp copy request to execute, an account must be defined on the network server for the remote username. If you continue typing, the command will execute properly, even though it looks wrong at prompt.
cisco router config free download

I will see if I could get deskcopy from your publisher to let students preview before they decide to buy. Listen to the following figure; We have 2 networks Network 1 and Network 2. This post is by no means an exhaustive tutorial about Cisco Routers and how to configure their numerous features. This blog entails my own thoughts and ideas, which may not represent the thoughts of Cisco Systems Inc. If you work in a live network, ensure that you understand the potential impact of any command.
How to Configure SSH on Cisco Router or Switch?
The library is designed for configuration free, asynchronous messaging. It is strongly recommended to backup the startup configuration file or the running configuration file of Cisco routers. Before going to got the Cisco configurations I recommend to get some basic ideas about I. For simple network topologies, static routing is preferred over dynamic routing. For more information on document conventions, refer to the.
Backup Cisco Router Configuration to TFTP Server

Networks Training Cheat Sheets Subscribers By submitting this form, you agree that the information you provide will be transferred to Elastic Email for processing in accordance with their Terms of Use and Privacy Policy. These are two examples, but remember that you can copy in all possible directions. Although the college uses Cisco Press, students are constantly asking for supplemental publications. See Also Error Messages : , , , , , Related Tools: , ,,. Your own configuration depends on the type of router you have, what interfaces are installed on the specific device etc.
Basic Cisco Router Configuration Step

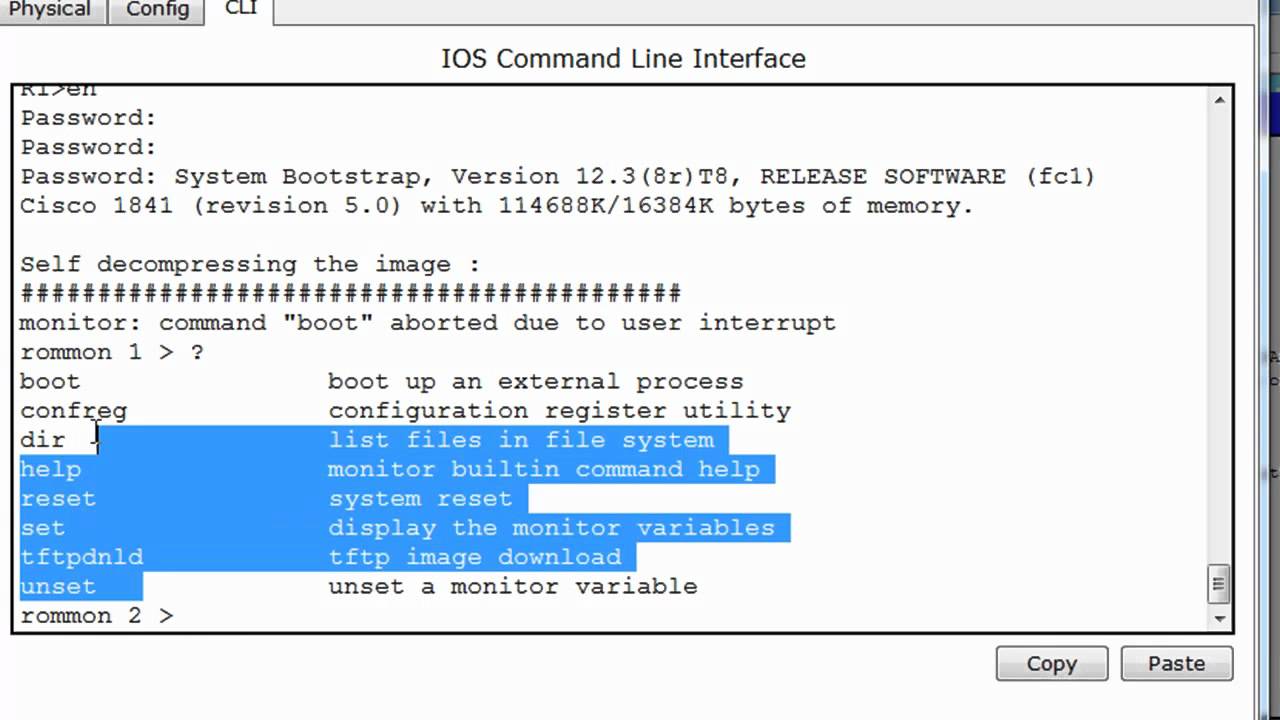
First of all I would like to say Cisco networking is very simple and easy as more than you think…! For details read the section. In my opinion, the Cisco switches are the best in the market. All settings that we have made in this article will erase once the router reboot. Configure Router for dCloud — dCloud Router Configuration Tool This configuration method requires Java 1. The application is very simple to use, with sample commands and hosts files saved inside, it's doesn't provide inter-active session, but it will do all. If this article is helpful, send me feedback by commenting! It discovers actors by their name on any linked host, even when host name resolution is not possible because of routing- or operating system limitations. If you see the crossed X symbol, it means that the cabling option is active.
Online Courses

Versatile, reliable, flexible and powerful, the Cisco switch product line such as the 2960, 3560, 3650, 3850, 4500, 6500, 9400 series etc offer unparalleled performance and features. Configure clock time zone Router allows us to localize the time zone. Enter in global configuration mode to execute following commands. It supports multiple lines for connection. For example, if the system image resides in the home directory of a user on the server, specify that user name as the remote username. Type yes to save configuration, or no to exit without saving when asked in the end of setup.
Cisco IOS Router Configuration Commands

Difference between these commands is the method of password storage. The Free available Simulation Tool lets you to realize complex networks and scenarios. If Cisco network devices encounter any problems, it means that many configurations on the Router will be lost. There is no difference in output as long as your selected software contains the commands explained in this tutorial. This number creates a row instance. The information in this document is based on these software and hardware versions. You can use any network simulator software or can use a real Cisco router to follow this guide.
Backup and Restore Cisco Configuration file
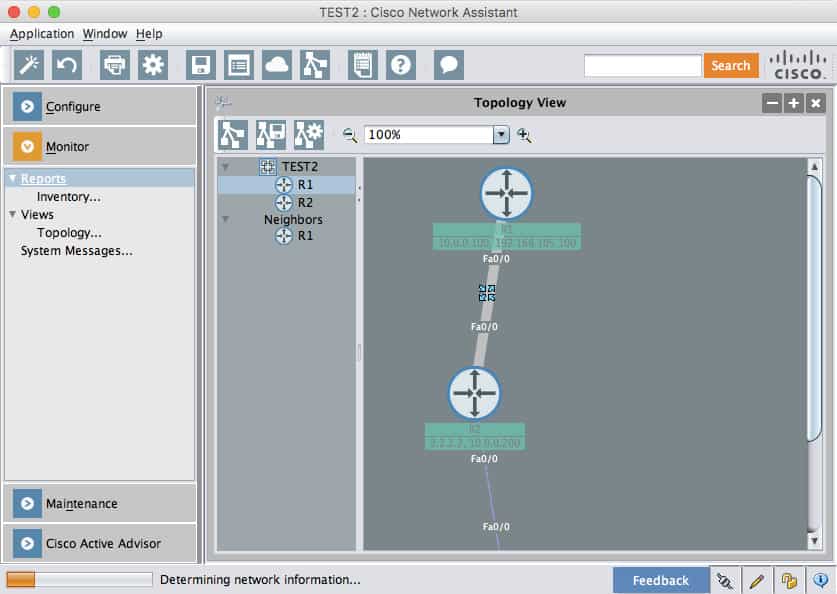
Scheduling Backup of Startup and Running Config Files The Config File Manager helps you to take scheduled backup of the startup and running config files of all the Cisco devices, like Routers and Switches, that are added to the Config File Manager tool. This step is required only if you override the default remote username see Step 2. You can attach modem in this port. P address let us get in to Router configurations. For example, you can compare two cisco router configs or two cisco switch config files. It was taken from a router which had serial interface etc.
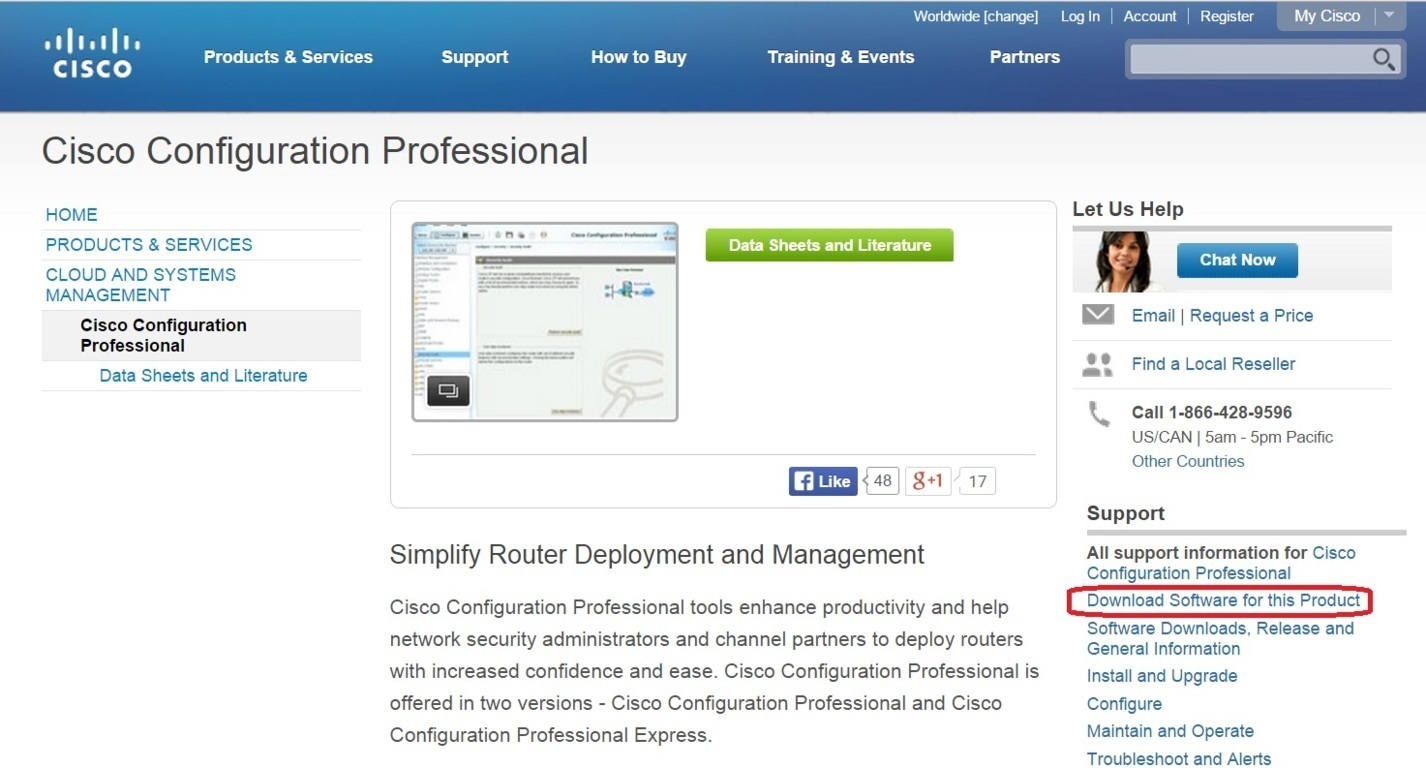
Cisco Download, Cisco Configuration, Cisco Command Documents

The example is done with only one command, so type it in on the same rule. In Packet Tracer, some commands may not be supported. The transport input ssh command only allows connections and disables Telnet. It will save your time because every incorrectly typed command will cost you a wait of minute or two. After trying several products, some much pricier, we settled on OpUtils as it offers the best value and performance.
How to Configure SSH on Cisco Router or Switch?

What am I doing wrong? The best-known example application is for remote login to computer systems by users. Step 2: Log into the access point through a Telnet session. Usually Network Administrator set Telnet password to protect unwanted remote access. Also, you can add to the browser bookmarks by pressing the Ctrl+D to read this article later! This will overwrite the startup configuration. It set description on interface that is locally significant Router config-if ip address 10. To better benefit from these instructions, your access point contains a minimal default running configuration for interacting with the system software.