Brute force software for android. Is it possible to brute force the android application login? 2019-04-24
Top 10 Password Cracking Tools

It could be used by hackers for carrying out automated and customized phishing attacks to infect the victims or obtain credentials. So, you should always try to have a strong password that is hard to crack by these password cracking tools. Medusa is a command line tool, so you need to learn commands before using the tool. Software can perform Brute force attack against multiple users, hosts, and passwords. Nmap Nmap for Android is a useful app to hack WiFi and taking a look into available hosts, services, packets, firewalls, etc. If the page does not exist, it will show response 404 and on success, the response will be 200.
Brute

This tool also comes preinstalled in many ethical hacking distros, including Kali Linux. It is a free and open-source tool. You can use this either to identify weak passwords or to crack passwords for breaking authentication. The most notable thing is that the tool is only available for Windows platforms. So, use these tools responsibly.
Best brute force password cracking software? : hacking

It performs dictionary attacks against more than 30 protocols including telnet, ftp, http, https, smb and more. Most of the time, WordPress users face brute-force attacks against their websites. If this dictionary contains the correct password, attacker will succeed. For the optimum results, it is important that several clients connected to the server. Software is update with extra feature of password histories display if history is available. Popular security tool aircrack-ng is one such tool, which has been ported to Android by many Android developers and security enthusiasts. In this case, you can try the same password and guess the different user names until you find the working combination.
Brute Forcing an Android Phone

Download Aircrack-ng from this link: John the Ripper John the Ripper is another awesome tool that does not need any introduction. It has been a favorite choice for performing brute-force attack for long time. Why would someone need a WiFi hacking tool? Named after the sons of Adam and Eve, this tool recovers the passwords using different methods like network packet sniffing and performing attacks like brute force, dictionary attack, and cryptanalysis. If the password is strong enough with a combination of numbers, characters and special characters, this cracking method may take hours to weeks or months. Therefore, you can also run it against encrypted password storage.
Brute Forcing an Android Phone

You can download these tables and use for your password cracking processes. That is assuming the drive is not encrypted. Brute-force is also used to crack the hash and guess a password from a given hash. As for the general cracking? Most of the password cracking tools start from there. Although we never encourage using any educational information for any cyber crime. If it is larger, it will take more time, but there is better probability of success. A longer password will take a longer time in guessing.
Brute

This file could make it easier for someone to brute-force their way into phones running the mobile operating system, code named Nougat. Just going by the file name, taht would suggest its a ruleset for seomthing, not a user signature. The attacker systematically checks all possible passwords and passphrases until the correct one is found. We have one around my house as well that is really great at breaking things and leaving them on my desk to fix. Doing so shows that someone has intentionally left it there to make brute forcing the password orders of magnitude easier and thus faster. It claims to be a speedy parallel, modular and login brute forcing tool. However, this traditional technique will take longer when the password is long enough.
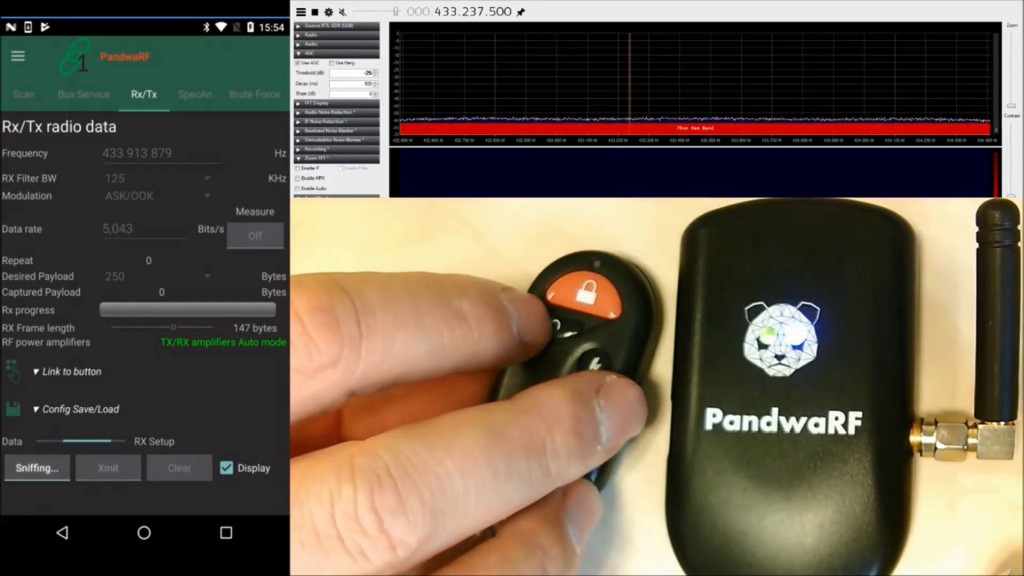
8 Best WiFi Hacking Software And Analysis Tools You Should Use In 2018
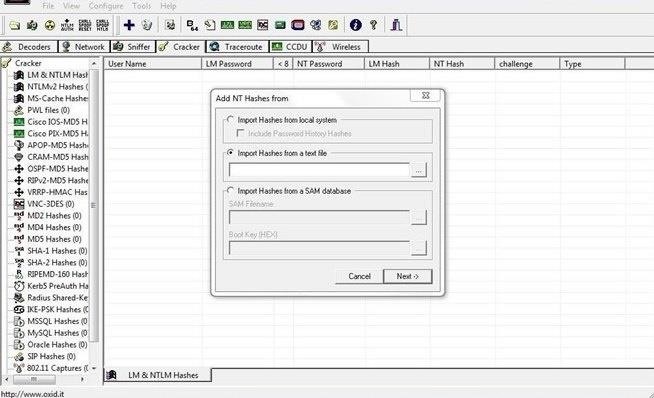
Pwdump : Password recovery tool for Windows Pwdump is actually different Windows programs that are used to provide hashes of system user accounts. By mirroring such methods used by cyber attackers, you can identify the holes in your network and make amends. It can also be used to find hidden resources like directories, servlets and scripts. RainbowCrack : New Innovation in Password Hash Cracker RainbowCrack software uses rainbow tables to crack hashes, in other words we can say it uses process of a large-scale time-memory trade for effective and fast password cracking. It takes a long time about 16 hours for 4 digits 2.
8 Best WiFi Hacking Software And Analysis Tools You Should Use In 2018
Never use same password everywhere. Brute Force Attack I n cryptography, a brute—force attack consists of an attacker trying many passwords or passphrases with the hope of eventually guessing correctly. Later, developers released it for various other platforms. Outputs will be ranked on a variety of factors at present, only number of dictionary words in output are counted. Password cracking tools try the combination of one by one.
Is it possible to brute force the android application login?

It uses dictionary, brute-force, hybrid attacks, and rainbow tables. Brute—force attacks are an application of brute— force search, the general problem-solving technique of enumerating all candidates and checking each one. She really got to me with the laptop ac adapter ripouts until i forced her to use the modemplug trick. It can help in cracking various kind of passwords by performing brute-forcing attacks, dictionary attacks, and cryptanalysis attacks. To save time, you can download those rainbow tables and use in your attacks.