Brute force download github. Instainsane 2019-04-25
android brute force attack free download
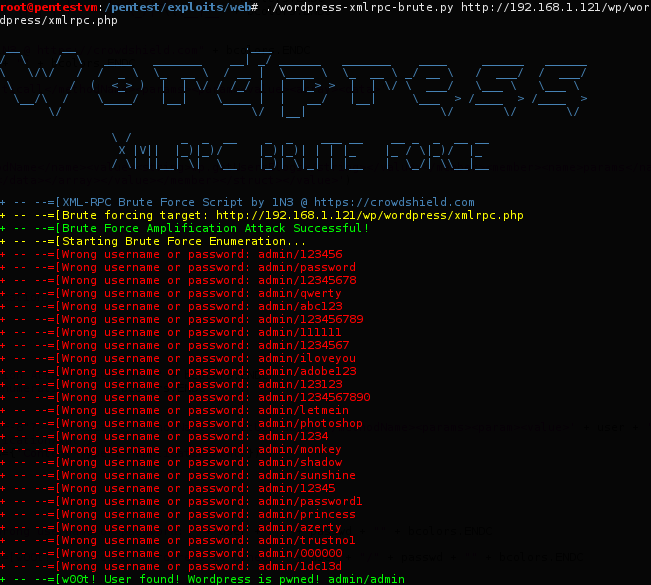
Brute Force attack is a kind of attack on personal accounts and encrypted pages through the password guessing. It is available for both Windows and Linux and supports all latest versions of these platforms. This attack sometimes takes longer, but its success rate is higher. InternalServerError: u'internal-server-error', '' Be ware of scammers i have been scammed 3 times because i was trying to know if my husband was cheating until i met this hacker named; who helped me hack into my spouse phone for real this great hacker hacked into my spouse whats-app messages,Facebook messages. The passwords in that file were encrypted, but researchers said the encryption method used by Adobe made it possible for attackers to. But if the password is short, it can give quick results.
Instainsane

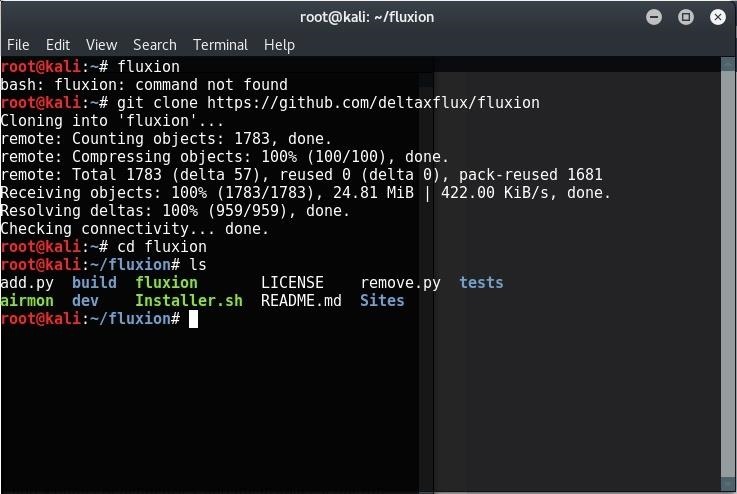
Download DaveGrohl from this link: Ncrack Nrack is also a popular password-cracking tool for cracking network authentications. So unless those are all well secured and they may be, no clue then moving to Android is no magical fix. I believe that this happened here too. I also mentioned this tool in our older post on most popular password cracking tools. Jennifer Lawrence has all the rights to take private nude pictures of herself in the privacy of her own house. Popular tools for brute-force attacks Aircrack-ng I am sure you already know about Aircrack-ng tool.
Crack Instagram Password By Kali Linux And Brute Force Attack
I loved my family so well that i could do anything to make them happy, but my daughter is not always honest with me, a man got her pregnant and for the past 2 months my daughter hasn't told us the father of the child i tried but there was no way but the only way was to get into her iPhone X but she has a finger print and also a pass code so i went in search of a hacker called jeajamhacker gmail. In this, attacker tries one password against multiple usernames. To prevent password cracking by using a brute-force attack, one should always use long and complex passwords. Not weird at all, makes perfect. Later, developers released it for various other platforms.
Popular Tools for Brute
Download John the Ripper from this link: Rainbow Crack Rainbow Crack is also a popular brute-forcing tool used for password cracking. He claims the hackers got them from iCloud hacks, and other more social engineering hacks. This process is very usually time consuming; if the password is long, it will take years to brute-force. . It generates rainbow tables for using while performing the attack. This can very well be the leak used to access the celebs nude pics.
StegCracker
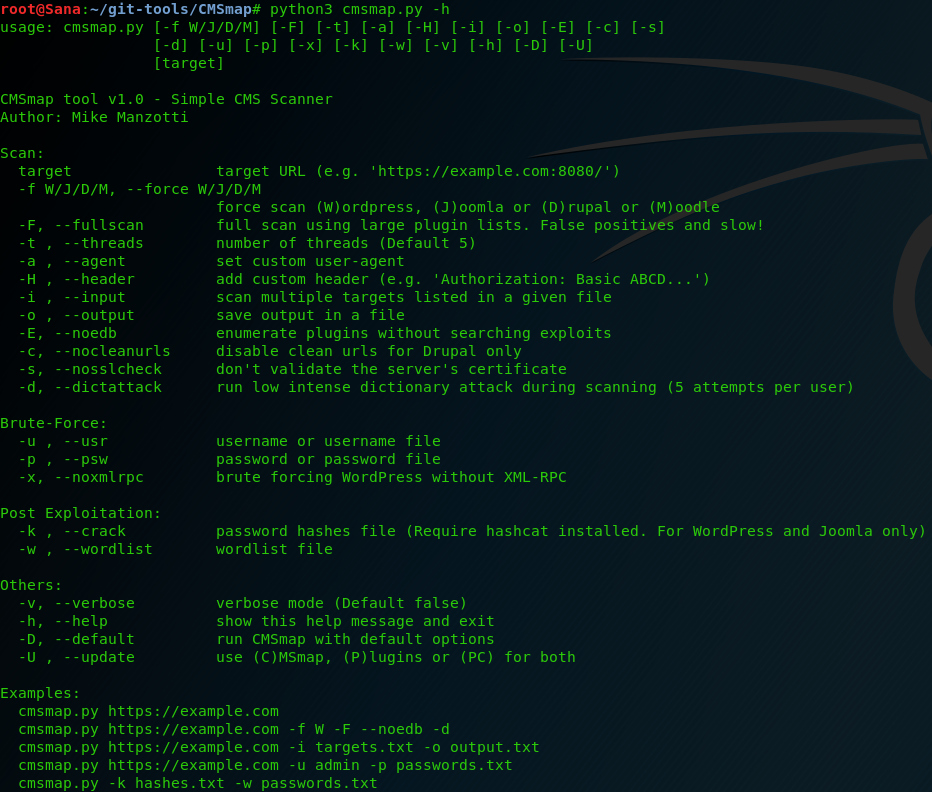
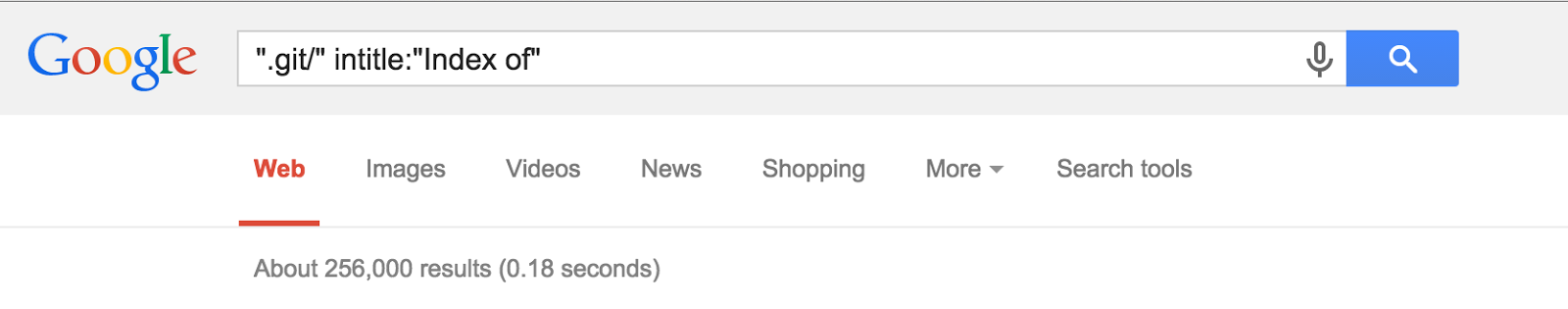
There are various other tools are also available which perform brute-force on different kinds of authentication. However, GitHub uses the bcrypt algorithm to , which is extremely resilient against brute force attacks because it takes an inordinate amount of time to encrypt each password. It is used to check weak passwords by performing dictionary attacks. You can use it in any software, any website or any protocol, which do not block requests after few invalid trials. The full version, due to release March 11, 2013 will allow password protection which helps protect your information by forcing the impostor to not only produce the 65536 bit key, but have your password as well and allows for individual passwords for individual files. He is currently a researcher with InfoSec Institute.
GitHub Fixes RCE and 2FA Brute
Brute-force attack when an attacker uses a set of predefined values to attack a target and analyze the response until he succeeds. Generally it focuses on different 4 areas of WiFi security i. The exact number of GitHub accounts that had their passwords reset was not disclosed and GitHub did not immediately respond to an inquiry seeking clarification. Nobody has the right to steal them, even if her iCloud password was Katniss. When Asked put in the username to brute force 6. Account lock out is another way to prevent the attacker from performing brute-force attacks on web applications. Even among my tech-savvy programmer friends it's common.
android brute force attack free download
Given the deep pockets Apple has, I don't understand how something like this was even possible. There are different tools for steganalysis but almost all of them require a person to manually use them. They have naturally been apprised of this. By far, Hydra has the most protocol coverage than any other password cracking tool as per our knowledge, and it is available for almost all the modern operating systems. Brute-force attacks can also be used to discover hidden pages and content in a web application. Success depends on the set of predefined values.
Updates InstaBrute

But there are a ton of people who don't care and just use the default. It is worth to mention that some virus scanners detect it as malware. Steganography is an art of hiding messages covert way so that exclusive the sender and recipient know the original message. This tool is very popular and combines various password-cracking features. In cases that the target uses a password consists of numbers, letters and symbols, a brute-force attack with a usual system may take months, which can not be justified at all.
GitHub accounts hacked in ongoing brute force attack
This suggests that in addition to users directly affected by this recent incident, users who used weak passwords might also be forced to change them. It supports various attacks including Brute-Force attack, Combinator attack, Dictionary attack, Fingerprint attack, Hybrid attack, Mask attack, Permutation attack, Rule-based attack, Table-Lookup attack and Toggle-Case attack. It includes a wide variety of tools such as packet sniffer and packet injector. It is used to check the weak passwords used in the system, network or application. The whole thing snowballs from there. The company said it wasn't hacked, but someone appears to have used credentials leaked during recent mega breaches to access GitHub user accounts.