Bitlocker windows 7 gpedit msc. BitLocker with TPM in 10 Steps. 2019-05-05
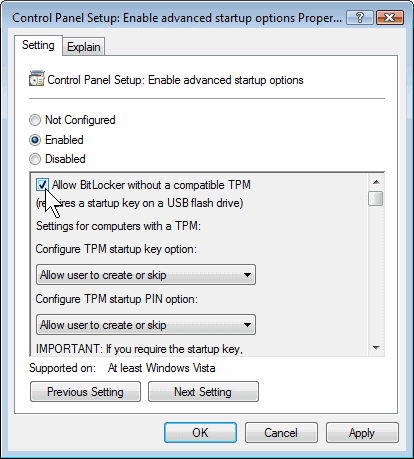
How to Allow BitLocker Without a Compatible TPM in Windows 10
For more information about the tool to manage BitLocker, see. When disabled or not configured No BitLocker encryption key is generated Reference This policy needs to be enabled before any encryption key is generated for BitLocker. If BitLocker To Go Reader bitlockertogo. Hi Superfranz83, · What is the complete error message that you receive when you try to apply bit locker on your system partition? How you configure these policy settings depends on how you implement BitLocker and what level of user interaction will be allowed. When enabled Users will be unable to save a recovery password to any location. Which means — it is recommended to generate a new recovery key on the new computer.
How to Enable a Pre

To recover this data, you can use the Repair-bde command-line tool. To configure a greater minimum length for the password, enter the desired number of characters in the Minimum password length box. Policy description With this policy setting, you can control the encryption method and strength for drives. The recovery key is a text file that can be opened in Notepad. All you have to do is the following to enable gpedit. Reference For more information about the recovery process, see the. When enabled All removable data drives that are not BitLocker-protected are mounted as Read-only.
BitLocker Group Policy Settings
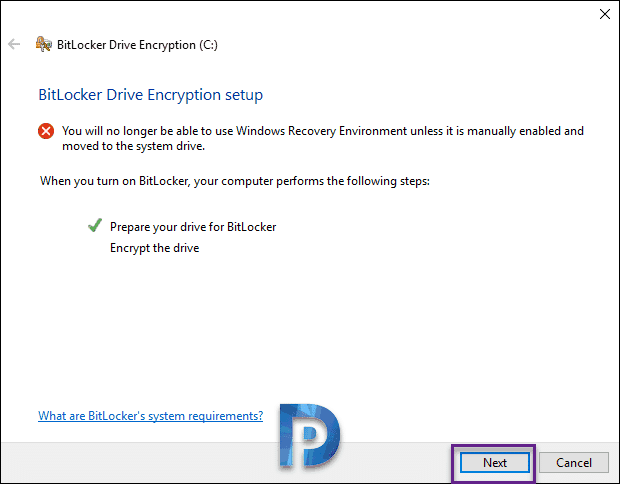
To do that, we have to configure some Group Policy options. Choose Full encryption to require that the entire drive be encrypted when BitLocker is turned on. Instead, BitLocker recovery options for the drive are determined by the policy setting. This policy is required to enable BitLocker Network Unlock on a network because it allows clients running BitLocker to create the necessary network key protector during encryption. When disabled or not configured The BitLocker Setup Wizard asks the user to select the encryption type before turning on BitLocker. When disabled or not configured The Windows Recovery Environment must be enabled on tablets to support entering the BitLocker recovery password.
How To Enable Group Policy Editor (orgmode.com) in Windows 7/8/10

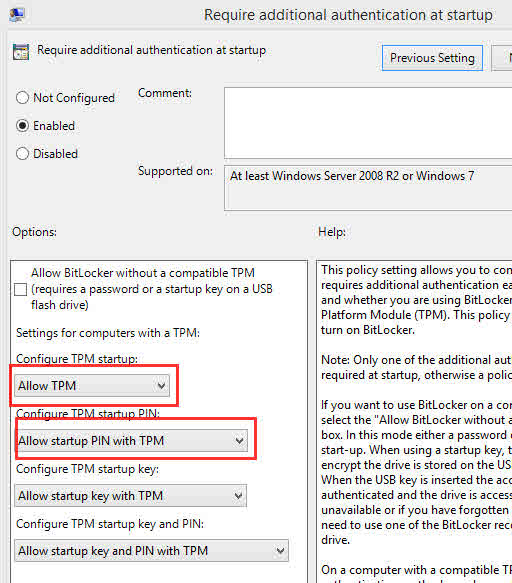
The Allow data recovery agent check box is used to specify whether a data recovery agent can be used with BitLocker-protected operating system drives. For more information about adding data recovery agents, see. Policy description With this policy setting, you can control whether the BitLocker Setup Wizard on computers running Windows Vista or Windows Server 2008 can set up an additional authentication method that is required each time the computer starts. Choose Full encryption to require that the entire drive be encrypted when BitLocker is turned on. In a similar manner, BitLocker updates the BitLocker To Go Reader only when the identification field on the drive matches the value that is configured for the identification field.
Configuring BitLocker in Windows 7
Configure use of passwords on removable data drives This policy setting is used to require, allow, or deny the use of passwords with removable data drives. The Allow data recovery agent check box is used to specify whether a data recovery agent can be used with BitLocker-protected removable data drives. This policy setting is applied when you turn on BitLocker. This way we can even install hard drive from one machine to another and use the recovery agent to recover files from BitLocker encrypted drive. Reference This policy setting is applied when you turn on BitLocker.
Bitlocker Error Fix: The Startup options on this PC are configured incorrectly

It also provides security for decommissioned computers. By introducing this software development practices, Microsoft built better software using secure design, threat modeling, secure coding, security testing, and best practices surrounding privacy. Курсор не будет регистрировать нажатия клавиш при вводе номера. When using data recovery agents, you must enable and configure the Provide the unique identifiers for your organization policy setting. When disabled or not configured The default recovery options are supported for BitLocker recovery.
BitLocker Group Policy Settings
You can require smart card authentication by selecting the Require use of smart cards on removable data drives check box. You can configure one or more partitions for your data drive D, E, etc. You can also specify whether you want to restrict the encryption algorithms and cipher suites that are used with hardware-based encryption. Choose drive encryption method and cipher strength This policy setting is used to control the encryption method and cipher strength. When disabled Platform validation data is not refreshed when Windows is started following a BitLocker recovery. If you have a Windows 7 Enterprise or Ultimate license then this is a great feature to protect the family photos and wife cooking trade secrets from falling into the wrong hands.
Использование редактора групповой политики BitLocker для включения проверки подлинности в предзагрузочной среде Windows 7 / 8 / 8.1 / 10
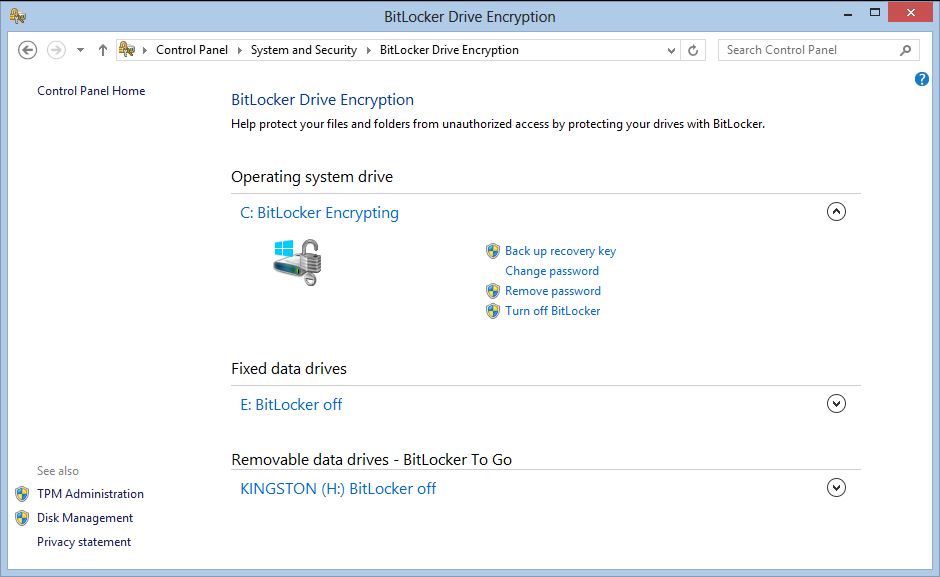
After this is complete, BitLocker is compliant with the Group Policy setting and BitLocker protection on the drive can be resumed. This policy setting is applied when you turn on BitLocker. If the Removable Disks: Deny write access policy setting is enabled, this policy setting will be ignored. When a computer transitions to Sleep, open programs and documents are persisted in memory. The next thing to do is to configure group policies for BitLocker. Better for Home users who really want to mess with the registry to back up the registry before experimenting and after successful mods.
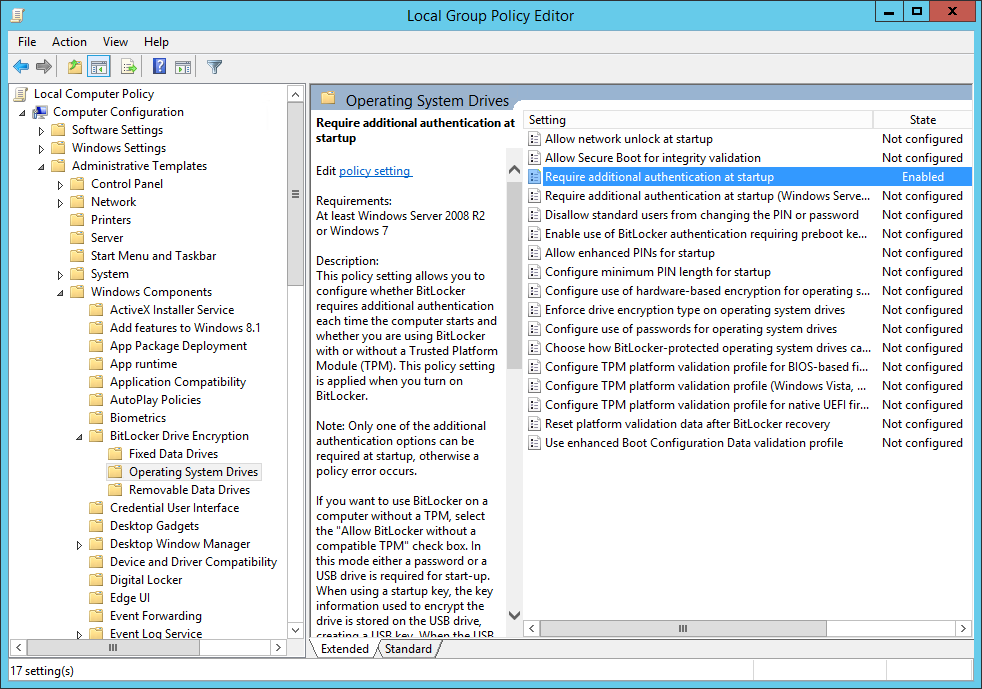
Bitlocker Error Fix: The Startup options on this PC are configured incorrectly

Changing the encryption type has no effect if the drive is already encrypted or if encryption is in progress. Introduced Windows Server 2008 and Windows Vista Drive type Operating system drives and fixed data drives on computers running Windows Server 2008 and Windows Vista. Allow Secure Boot for integrity validation This policy controls how BitLocker-enabled system volumes are handled in conjunction with the Secure Boot feature. The recovery key is used to recover the data on a BitLocker protected drive. Navigate to Computer Configuration — Administrative Templates — Windows Components — BitLocker Drive Encryption, Operating System Drives: Require Additional Authentication at Startup.