Best antivirus and vpn for mac. Best 3 Antivirus for Mac of 2019 // Updated: April 2019 2019-01-26
Best VPNs For Mac in 2019

It blocked 100 percent of malware during the August 2018 testing. Over time, three distinct protection methods have developed and evolved. And while the lack of real-time protection means Malwarebytes can't stop attacks - only remove existing infections - it also ensures there's no real impact on your system resources and the app is unlikely to conflict with other antivirus tools. I have a quick question on these providers that I hope you can help me with. Whenever a cybersecurity firm discovers a new malware, its sample is added to the database. Pros: Largest collection of servers. Last, and certainly not least, are spies and government agencies.
Best Antivirus for Mac 2019: Abjuration for Apple

In addition to its multi-system compatibility, HideMyAss also allows for simultaneous connections. However, this is not even entirely accurate. Mac antivirus software isn't often checked by the independent testing labs, but Avast's most recent results were good, with finding the package detected 100% of sample threats. For protection on a single Mac, or protection across devices with Total Security, Kaspersky is a great choice. On-demand scanning to clean up infected systems? The problem isn't your Mac, per se. It was 100 percent effective against 507 samples of malware discovered in the four weeks leading to the test. Additional management tools that let you set policies can help mitigate this risk.
Best VPNs For Mac in 2019

A one Mac, one-year licence can be yours for £49. Intego partners with Panda Security for Windows protection, a decent provider that, unfortunately, loses some luster because of poor performance. Online security is a big reason why downloading and installing a is becoming an ever more popular thing to do, but of course there are plenty of other reasons why you may be hunting for a Virtual Private Network. This new location allows users to access content that they may have originally found restricted. Users, therefore, have little chance of remaining anonymous. But it's the added little extras that make CyberGhost stand out from the rest. To help you, we have analyzed the global pricing strategy of each firm to find out which offers the most value for your buck.
Best VPNs For Mac in 2019

This, sadly, is not the case. Examples include phishing and social engineering. The hacker can then remotely access your device and use for its nefarious plans, which range from fairly harmless to identity theft. It was 100 percent effective in the malware tests, better than the 95. The firm's dedicated app is intuitive and very user-friendly, featuring a one-click option for connecting, as well as some advanced options. We have no control over the third-party websites we link to and they are governed by their own terms and conditions.
The best Mac VPN 2019
Having more server locations means that you'll always have a server nearby, which is important because a server that's close to you will be faster and more reliable than one that's far away. Using this method, the antivirus software executes the potential malware in a safe environment in which it cannot cause harm. These are valid concerns, but as with a company's information gathering policies, we think it's best to assume everyone is innocent until proven otherwise. They also automatically log you in on your favorite websites when you visit them. Fewer options than Windows version. The first bricks of the web were laid by government and university academics who were interested in making information sharing faster and easier.
Best Antivirus for Mac 2019: Abjuration for Apple
Virus definitions are updated in a timely fashion, too, regardless of how long the initial updates might take to finish. The best services log as little information about users and their activity as possible, and should explain why in their privacy policies. That said, the Maximum Security package is much better. You can run on-demand full system scans if you suspect a problem, or launch a more targeted check on specific files, folders or drives. The feature monitors files and folders you specify and blocks changes to them. These digital signatures can be viewed as patterns, in either activity or code, that indicate the presence of malware. In this method, the source code of suspicious files is compared to the source code of known malware in the database.
Best 3 Antivirus for Mac of 2019 // Updated: April 2019
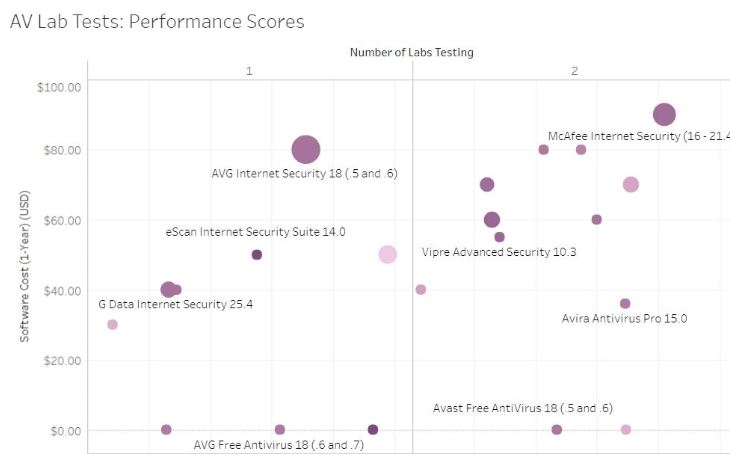
False Positives False Positives makes up 5% of the total score When a clean file is flagged as malware, we speak of a false positives. The prices start low and we found in our tests that its encryption was strict in ensuring your anonymity online will be protected. Additionally, with its watertight privacy settings, your data is always private. Although this looks all very basic, use Bitdefender Virus Scanner for Mac for a while and you begin to notice some very neat touches. Among many others, these include: Website advisors: A tool that warns you before you access a website known for malicious intent. A status display keeps you up-to-date on how your system is doing, and four buttons enable running a quick scan of critical locations, an in-depth check of your entire system, or speedy scans of running applications or a folder of your choice.
Best Antivirus for Mac 2019: Abjuration for Apple

New software releases and updates frequently come with security flaws. An option to exclude files and folders from the scan - network shares, system backups - is another plus, reducing the work the engine has to do and significantly speeding up your scan times. You can learn more about it in our. While the amount of Mac malware is still considerably less than that targeting Windows, its still 100 times higher than what experts predicted just a few years ago. Protection from Malware Protection from malware makes up 50% of the total score Protection from malware and other online threats is the most important feature of any cybersecurity product. The risks are increasing, which is why you need protection. This is particularly useful because public Wi-Fi networks might not have the most robust security.