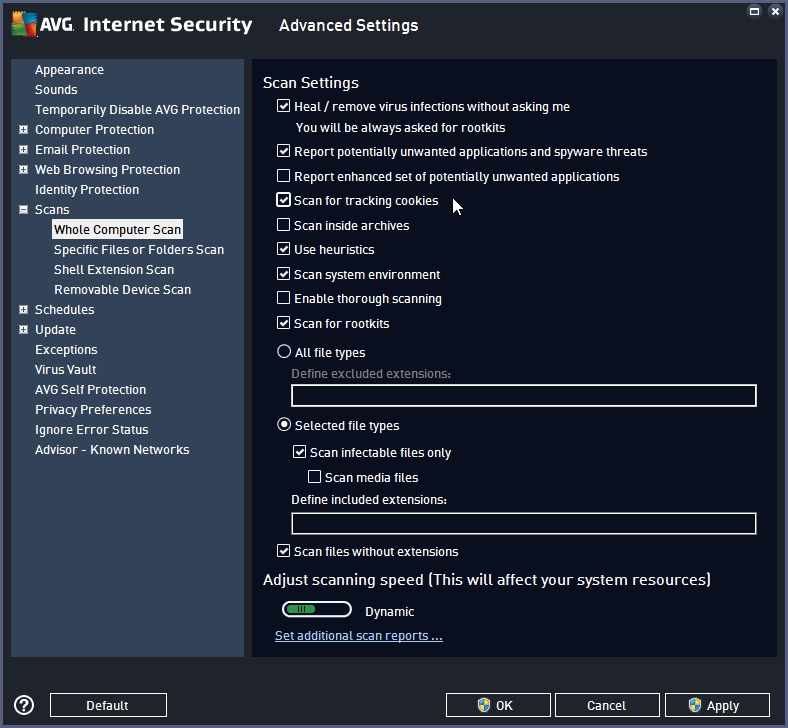
Avg ransomware protection settings. Protecting Your Business from Ransomware 2019-02-25
AVG Internet Security voor al uw apparaten

For instance, cybercriminals hit businesses that use online sites for recruitment. Anytime our antivirus experiences an unknown threat; it uploads it into our ThreatLabs team for analysis. Selecting this option may result in frequent and potentially annoying alerts. Users are urged not to pay the fees. We had no issues in either case during the installation process. The ransomware protection module allows the preset of folders that will be protected.
Protect Your Computer From Ransomware With Eset Smart Security With The New Protection Settings 2018
It is the security program which will show the user the status of their safety. PowerWare — PowerShell hijacker 9. To specify which types of files are protected in each folder, click Change protected file types. Both platforms run on the Avast security network but maintain separate features. The application blocks cyber threats and the download of harmful files. It has a small tuneup package and ransomware protection, as well, making it better than Avast Free read our. Results were great every single time.
AVG Internet Security Review: A premium antivirus suite that you can put on all your household PCs

Op die manier weet u zeker dat u alleen op echte websites terechtkomt. Windows 10 Controlled Folder Access feature is disabled by default, however, it can be enabled from the Windows Defender Security Center. It's a robust, two-way firewall that did well in testing, but didn't go beyond the expected. While ransomware has evolved into targeted attacks rather than mass spam campaigns, it is still a significant threat to businesses and consumers. As of now, the antivirus benefits from a shared engine that protects against online threats.
AVG Internet Security 2019 review
If you want to shop around, make sure to read our other. . The results showed that it did. It can automatically whitelist addresses from the Outlook address book, and it lets you correct any mistakes it makes such as missed spam messages or valid messages tossed into the spam folder. But the growing frequency of these attacks have made us realize that we need a more drastic approach, and so Ransomware Protection was born.
AVG Internet Security 2019 License Key Full Version With keygen

The first of them offers access to your web cam only to those applications that the product considers safe. Little things stand out such as the way it makes every encrypted filename unique to make it more difficult to understand the damage. You can go lightweight and just install basic protection or do a more muscular package including features such as webcam protection. Alternatively, you can add the application to the list. Hackers niet, ransomware niet; niets of niemand. Most users should leave this set to Medium, the default.
Windows Defender Antivirus in the Windows Security app

If you're not an outlook user, you must define a message rule in your email client to handle marked spam. In fact, I was surprised enough to repeat the lengthy test, with no better results. The setup procedure is easy, and you have to choose the part you would like to maintain your group and exclude the processes it is not vital. You can check this against the latest version available for manual download, or review the change log for that version. The activation of the firewall module offers non-stop monitoring of both traffic as well as your Internet and network connections.
AVG Internet Security Review: A premium antivirus suite that you can put on all your household PCs

This window is very reminiscent of Norton Security. With Locky and Cerber, CryptoWall is still the most common ransomware threat. This works for almost any connection on the world wide web, such as those on Facebook and Twitter. The safest way to connect Your email has never been safer. Ransomware cannot be removed with Antivirus or Anti-Malware programs. This module helps you delete the cache and application logs.
AVG Internet Security 2019 Crack + Key Full Download

After using the module, we tried retrieving the files using different dedicated software applications. Every time we do a review, we test the Data Safe featured on a security solution. Most ransomware is spread hidden withi… What is 'WanaCrypt0r 2. The system will be protected in the case of an attack. Only a true firewall maven should consider switching away from the default level the firewall suggests. The Tune-up option identifies possible problems on your computer. New Ransomware Shield Insurance has no price when your personal files and photos are at stake.
AVG Antivirus: Ransomware Protection

Ransomware protection The number of ransomware attacks has increased by more than 200% in 2017. Did you try to update windows? Its interface is functional rather than beautiful and appealing in its simplicity. We make sure your express permission is required for unknown programs to alter them. If you still have doubts about getting a product with antivirus and antiransomware protection, think of the record number of cyber attacks that affected 2017. To get the data back, the users are required to pay a ransom money in bitcoins and once the ransom is paid, the attacker is supposed to release the data back to the users. Now the specific shields should be disable and you should see something like this. Voor Android: Arabisch, Chinees traditioneel , Chinees vereenvoudigd , Deens, Duits, Engels, Fins, Frans, Grieks, Hebreeuws, Hindi, Hongaars, Indonesisch, Italiaans, Japans, Koreaans, Maleisisch, Nederlands, Noors, Oekraïens, Pools, Portugees Brazilië , Portugees Portugal , Russisch, Servisch, Slowaaks, Spaans, Thais, Tsjechisch, Turks, Vietnamees en Zweeds.
AVG Internet Security 2019

It can also help identify outdated software that can possibly turn into a security issue. Additional protection measures, such as download monitoring and email protection, are included, as well. Upsell Issues Avast's feature set is littered with upsell items, features that tell you there's a problem and offer to solve it…for an additional subscription fee. To check on that possibility, I time many runs of a script that moves and copies a large collection of files between two drives, averaging the results. Our tests include established testing tools, not malware found in the wild. By 2017, it is everywhere, supplanting all other forms of malware as the number one menace. For more information on how to configure Software Restriction Policies, please see these articles from Microsoft: and What can you do? These programs create a malicious website, run a spear-phishing campaign to get the malicious software distributed — including inserting themselves into known good sites — and then disappear after six hours.