Avg online shield service. AVG using about 40% of CPU all the time 2019-04-23
mySteganos Online Shield VPN
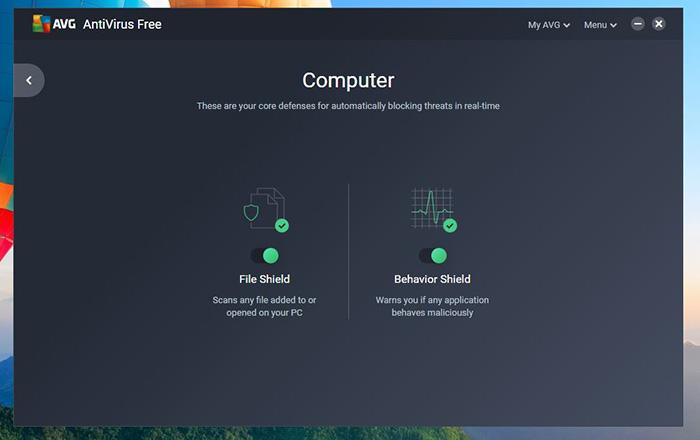
Service 14,442K and 37,042K during scanning While idle, the total memory usage was around 20,486K. Anytime our antivirus encounters an unknown threat, it uploads it to our ThreatLabs team for analysis. About the Author James T Wood is a teacher, blogger and author. Behavior Shield Like an alert watchdog, this feature works in real-time to sniff out suspicious behavior of any software running on your computer and warn you if anything is amiss. Click to Resident Shield and you will see Resident Shield window similar to the one below. This scan merges scan methods to detect malware, poorly rated browser add-ons, and performance issues. To turn it off, click on the slider within the button.
AVG 2016: Disabling AVG Components
Started having problems after upgrading to ver 9. Free Antivirus 6 had the lowest resource consumption. Repeat for each of the remaining checkboxes on left After you have done that, we will be able to diagnose if anything else needs to be done If the problem is resolved. Click the curved arrow icon next to Virus definitions on the left side of the screen to perform an update. Troubleshooting of the situation will continue over e-mails. CyberCapture Cloud-based technology helps stop even the newest malware variants and outbreaks in real-time.
How to disable AVG antivirus Resident Shield (Disable/Enable AutoProtection)

I just disabled Identity Monitor. For instance, I saw memory usage around 19,496K at idle and 61,520K while scanning. To turn it off, click on the slider within the button. This means the features are scanning the websites and providing protection against threats within malicious or hacked websites. In comparsion, my browser is using around 1,817,924K, but that is with like well over 30 tabs opened and having not restarted my browser for days, which would usually drop it down to 400,000K. Please store these account credentials in a safe location and for your own privacy and safety, do not share them with anyone.
Resident AVG Free Shield Alert Does Not Allow Me to Remove Infections
Since the file never got onto your computer, there is no infection to be removed. The effectiveness of malware detection, how well it catches infections, is the chief characteristic to consider when choosing an antivirus program. If a threat is found, the file will be blocked and you won't be able to save it to your computer at all. Here I discuss the system requirements, download sizes, and the installation process. Custom built Pen 4 2. This scan can take several minutes.
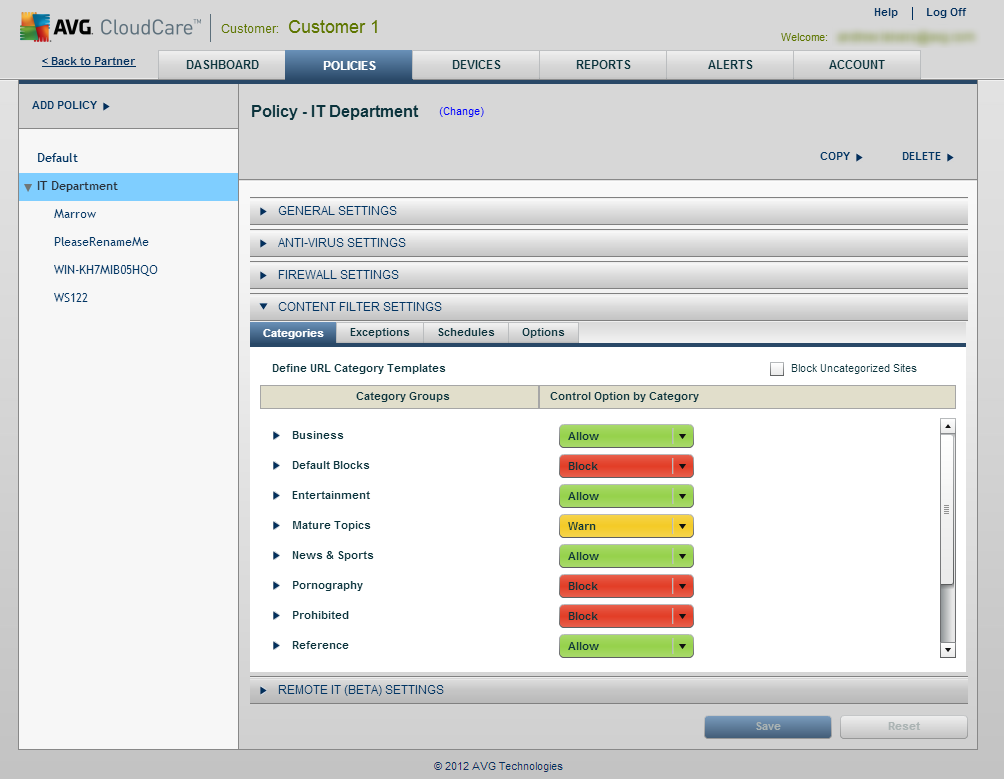
Configure AVG Firewall

The virtual private network makes your computer invisible. Copy and Paste the result of the scan in the reply box below. The speed slow up was significant and they were leaving in droves. Note: You can re-enable Resident Shield using the same steps, but this time place a check to the Resident Shield Active box in Resident Shield component settings. Run the registry cleaner checking 1 box at a time in the left panel.
Online shield results
To check your anti-spam options, consult your web mail service provider. The bind moggles Mike mike. I also found avast uses a caching feature to help speed up real-time and manual scans. In the settings I found a couple resource control features. The email address is the same address where you received the confirmation email after purchase.
mySteganos Online Shield VPN

Fragments Bytes Clusters Name 13:40:44. Payments Protection Shop and bank online freely and securely Whether browsing, banking, or shopping, this is the added internet protection you need. If you see a red status, a critical issue needs your attention. We block spam and scams, and even help you avoid fake copycat websites, to prevent you from accidentally giving our passwords or credit card numbers to the bad guys. We do not recommend disabling any component indefinitely by selecting Stop permanently. That means nobody messes with any of your private data, files, photos, and passwords — no hackers, no ransomware, nothing.
How to Set a Program as Trusted in AVG
After running a scan, you can access the Quarantine from the results page. It does work, is new but will get better. When done, tell it to clean those entries. If the application is not in the Blocked Apps list, try adding it to the Allowed Apps list. Advertiser Disclosure: Some of the products that appear on this site are from companies from which QuinStreet receives compensation. Your product is now activated. Browse safely and anonymously wherever you are.
Is Your Free AV a System Hog?
But persisting behavior could point to some conflict with other installed protection applications or firewall or remains of incorrectly uninstalled , which needs deeper analysis. I also found two useful scan scheduling settings for laptops: you can enable it to not start if running on batteries and pause if you begin to use batteries. The download file at 59. We recommend you to try a 1 week subscription - the optimal way to check out how it works, and extend it later with a longer duration to optimize the subscription cost. If the icon is red, you are not fully protected and the feature requires your attention. I don't know if the paid version does it.