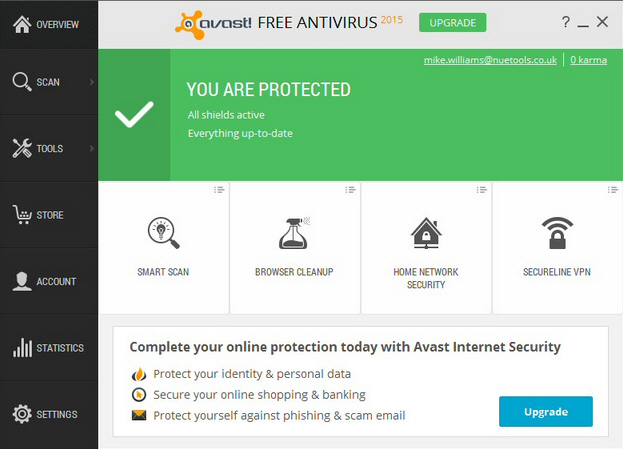
Avast virtual machine. #13367 ([FIXED IN SVN] VirtualBox 4.3.16 got stuck when running any VM while previous versions were good) 2019-04-11
Avast and a Virtual Machine?

So Tor relays generate a certificate for a random domain name to see how, look at the code in. Setup is unfortunately not as easy as running a program on your machine. The installation instructions list other dependencies that you do need to install on the target machine. Does this help with the 'man in the browser' attacks I hear about on the news? The firewall in the host should not be aware of any traffic going to the guest. I've tried various driver updates and a bios update and several system restores along the way, but to no avail. I have a windows dump that has recovered from an unexpected shutdown.
Avast releases machine

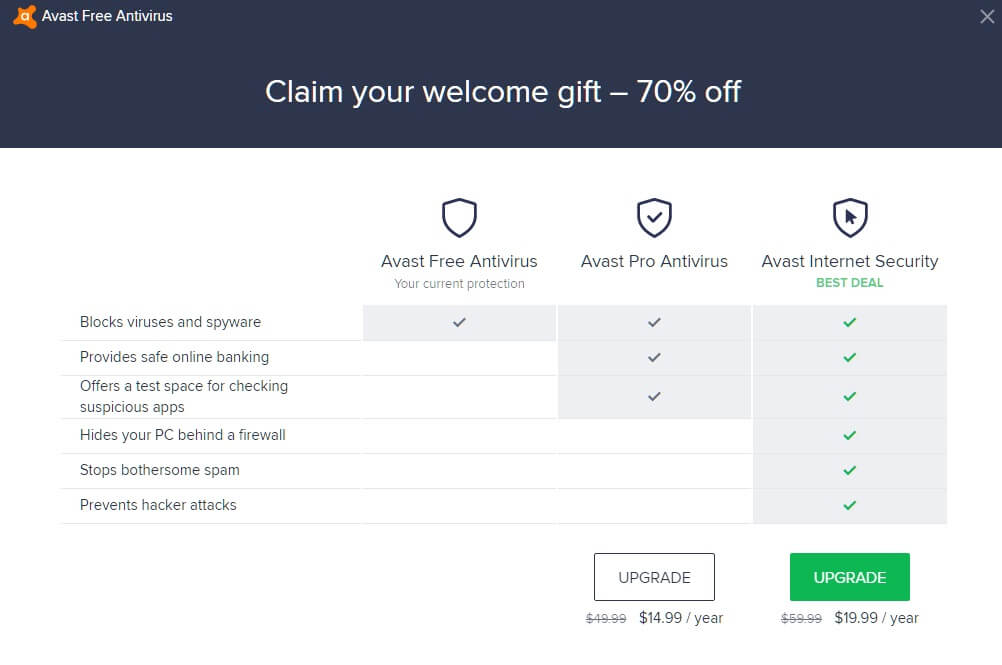
The purpose of a specification is to create a clear description and requirements for engineers to code to. I'm looking at different ways to prevent infection, as I think it is better to prevent issues than trying to find and cure them. We combine virtualization of suspicious applications and deep instrumentation to see at the high level, as well as at an instruction level, what the examined program is trying to do. Reinstalled, no fun until I see your post. He also said it's a bit like having a dual boot, and it can use a separate operating system. Features are collected during emulation and malware is then blocked according to our unique rule engine. Firewall is a component of Avast Internet Security and Avast Premier, and creates rules each time an application or process starts for the first time.
#16356 (Installing Avast Free anti

Adjust access restrictions You can set connection allowances for each application or process to determine how strictly Firewall monitors incoming or outgoing communication. Similar help and support threads Thread Forum Hi Admin's, Please help to check on my dump. The garbage collection process was especially controversial. Hi Tobias4051, Have no problems with sandboxie. Try searching the forums first with Google and add the site filter for this forum. Software interoperability was a bold concept at the time, but few developers today would think twice about it. The Host and Guest are networked together, and you might like the Shared Folders option when you see it, that lessens the security again some.
Setting up Firewall Application Rules in Avast Antivirus

I stumbled upon a website that provides a free download to a piece of software that im 90% convinced it is actually a virus. A software specification or spec is a human-readable design document that describes how a software system should operate. Set actions for unauthorized connections In addition to defining the types of connections you authorize for applications or processes, you can also specify how Firewall behaves when it detects a non-authorized connection. You always run the risk of malcode escaping from the sandbox. This causes me an issue though that my Avast Firewall on my Windows host wont let the virtual instance connect to the internet. The machine only returns to normal after it is restored to the previous state of the machine before installing Avast.
Avast install stuck on virtual machine
They had to address that bug. What about the Avast sandbox with an upgraded version of Avast? Back to using only File system shield. The default profile setting when no profile is selected is Public. About 30-50% of the times I run tails in a vm my avast pops up a notice on the host complaining about some problem with a certificate. I would be very grateful for an help and instance , if you guys could just point me in the right direction that would be great. I taught i was all set but then it asked me if i would like to create a virtual hard drive and which type i would like it to be. If any one of them encounters malware, Avast uses 6 layers of protection to identify, block and inform the entire network in a matter of seconds.
Avast Enterprise
I installed the latest version of Avast and noticed it's making VirtualBox running very slow. To create a new group, click New Group and provide a name for the group. Is there not a chrome type browser built into the internet security version of Avast that works a bit like a reverse sandbox, not letting malware on the computer affect the page, does it also work like a sandbox at the same time? The Java Virtual Machine is a program whose purpose is to execute other programs. For information about the correct network port to specify for an application, contact the application vendor or refer to the application's documentation or support pages. Hope that helps someone out there, enjoy! Thanks for contributing an answer to Tor Stack Exchange! Id like some information on how to set up my virtual machine as secure as possible so there would be minimal to none leakage.
#16356 (Installing Avast Free anti
I don't know enough about Avast to suggest how to disable this behaviour, but it is safe to ignore it. You should run inside a virtual environment when handling material that you expect to be malcode. But it is a very effective additional layer. I have contacted Avast to see if they know of a solution , though because this is an unusual situation , I don't expect that many of the customers will want to use virtual box with bridged network I am not sure that they will be able to help. System Security I was faffing about with Virtual box yesterday then when i turned my computer on today i got this screen. The normal Sandbox is meant to help prevent infections from occurring in the first place, for your everyday browsing. Since it got my attention, i have the urge to test it out.
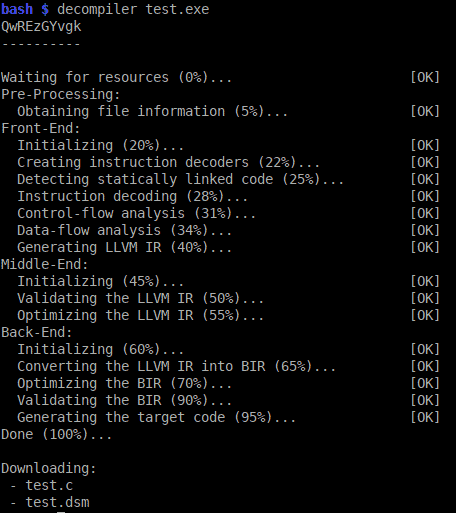
What is the JVM? Introducing the Java Virtual Machine
It is pretty much the exact opposite of a compiler, a program that turns source code into executable files. The scenario requires one Virtual Windows Server 2003 and one Virtual Exchange Server 2007. You think of SafeZone, it is like a reverse-sandbox that uses an Avast! Additionally it definitely was affecting normal use of Windows by slowing things down more even with a fairly powerful pc. From the developer's perspective, the underlying class loader mechanisms are typically a black box. I've never used it, but if you gave the free trial a spin, and installed a keylogger for example, then used SafeZone, the keylogger would be unable to record what happens. By peeling off layer by layer with deep dynamic introspection, the generic unpacker component is able to unveil known malware samples that could be hidden in heavily obfuscated and encrypted ones.
Avast install stuck on virtual machine

Basically, what a decompiler does is take an executable file as input, to source code. Application Rules are organized into groups, predefined according to application vendor. I have already set up a system restore point and am running Avira anti virus and Malwarebytes anti malware. When Firewall is set to the Public profile, the default higher level of security is applied to all networks, including the ' Friends' networks. In the attached dump files, the last. Every Java Virtual Machine includes a class loader. I had another vmware linux open and everything fine here.
Avast and a Virtual Machine?
I have also allowed Virtual Box to do whatever connection it wants. I have tried searching Google for a solution but haven't be unable to find a solution. Sounds simple, might even look simple from outside, but it is a massive undertaking, especially given the power and flexibility of the. On the dialog that pops up there is a check box about in the middle maybe a little lower of the page to enable Internet Sharing. Internet Security for my software host based firewall and anti-virus on my Windows boxes. I am a very safe surfer,and make sure everyone else in the house is aswell,is it worth changing to f-secure or.